CVSS V4.0: steps for an advanced vulnerability assessment

The CVSS (Common Vulnerability Scoring System) emerges as a scoring system that provides a standard and open method for estimating the impact of software vulnerabilities. This system is structured in four sets of metrics:
- The Base group captures the fundamental qualities of a vulnerability that maintain their constancy over time and across user contexts.
- The Temporal group reflects the characteristics of a vulnerability that evolve over time.
- The Environmental group deals with the specific characteristics of a vulnerability linked to a user.
- The Supplementary are new metrics that describe and measure additional extrinsic attributes of a vulnerability.
The main function of CVSS is to classify vulnerabilities using a score ranging from zero (0) to ten (10), which allows determining whether they represent a low to critical risk.
CVSS 4.0 is the latest evolution of this vulnerability assessment system in which more refined metrics have been incorporated, including new impact categories and attack requirements. Vector chains have been simplified for better understanding and clarity in scoring, improving accuracy and adaptability in threat assessment.
Changes from previous versions
The main changes from version CVSS 3.1 are as follows:
- Temporal metrics were renamed as threat metrics, resulting in clearer and simplified metrics. In addition, the remediation level (RL) and report confidence level (RC) have been removed, with the goal of reducing the CVSS-BTE (Base, Threat, Environment) score, as many base metric results were too high.
- By including the "attack requirements" metric, we have sought to solve the problem caused by entering low and high values, dividing it into "attack complexity" and "attack requirements".
- The "scope" metric has been eliminated and the impact metrics have been expanded into two groups:
- Confidentiality (VC), Integrity (VI), and Availability (AV) of vulnerable systems.
- Confidentiality (VC), Integrity (VI), and Availability (AV) of affected systems.
- Finally, a new group of metrics called 'complementary metrics' has been introduced to convey additional extrinsic attributes, which will be discussed throughout this article.
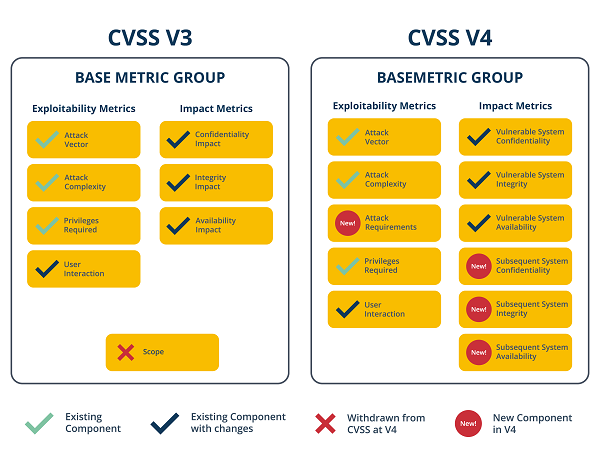
- Example of upgrade in base metrics from CVSS 3.1 to version 4.0; Source. -
Scoring guide
Once values have been assigned to the metrics, the equation calculates the score, generating a text string with those values that is used to communicate how each score was generated. For this reason, the vector is usually displayed next to the vulnerability score. Although it may seem a complicated process, there are several tools that help to calculate the vulnerability score, which makes the classification much simpler, such as the official FIRST calculator.
Once the characteristic values of the vulnerability being analyzed have been selected, the final score will appear automatically. In addition, at the bottom of the base section, you will be able to see the vector chain with the values you have chosen.
Supplemental metrics
As mentioned, the new group of 'Supplemental Metrics' describe and measure additional external attributes of a vulnerability and are used for the purpose of supplementing information about a vulnerability, providing organizations with the ability to define importance and significance about vulnerabilities.
It is critical to note that these metrics do not alter the score in CVSS v4, as their values are primarily completed as internal information and do not influence the vulnerability score. However, these metrics can be used to describe specific aspects of vulnerability.
Given the nature of these new metrics, each of them is briefly reviewed:
- Security: identifies whether it is possible that exploitation of the vulnerability could have an impact on the security of the system.
- Automatable: indicates whether it is feasible to automate the entire process, starting with identification and leading to exploitation
- Recoverability: this metric exposes the ability of the system to recover after an attack, in terms of performance and availability.
- Value density: details the assets that an attacker can take under his control through a single exploitation of the vulnerability. The metric has two options: "diffuse" and "concentrated". Its purpose is to determine whether compromising the vulnerable machine will gain access to diverse resources or multiple assets.
- Vulnerability Response Effort: provides additional detail on the challenges companies face in attempting to provide an initial response to the impact of vulnerabilities on their infrastructure. In other words, it provides supplementary information on the degree of effort required to implement mitigation measures and/or plan for remediation of identified issues.
- Provider Urgency: this metric provides information on the urgency to address the vulnerability.v
- Supplementary metrics; Source -
Example of a modification with a scored vulnerability
In this case, an example of scoring between CVSS 3.1 and CVSS 4.0 will be performed. This is a Node.js vulnerability where a score difference of almost two points can be seen, which is due to the extension of metrics and their refinement.
Vulnerability analyzed: CVE-2022-32223.
- Description: Node.js is vulnerable to execution flow hijacking: DLL hijacking under certain conditions on Windows platforms. This vulnerability can be exploited if the victim has the various dependencies on a Windows machine. It is possible for an attacker to place the malicious "providers.dll" file in a variety of paths to exploit this vulnerability.
- Difference in scores between CVSS 3.1 and CVSS 4.0: The following illustration shows how using the CVSS v3.1 scoring system yields a score of 7.3, while the CVSS v4.0 score is 5.4.
- Score difference between v3.1 and 4.0. Source -
- Analysis in CVSS 3.1: parameters and metrics defined according to the vulnerability detected for CVSS 3.1 version:
- Example of scoring result for vulnerability CVE-2022-32223 using CVSS v3.1. Source -
On the other hand, in the new version 4.0, some parameters are maintained, such as the attack vector or the complexity of the attack, but other parameters also vary, such as attack requirements, which are not shared with version 3.0 and hence different scoring results are obtained.
- Example of scoring result for vulnerability CVE-2022-32223 using CVSS v4.0. Source -
Conclusions
CVSS V4.0 is undoubtedly a major improvement over CVSS V3.1. As was the case with the evolution from version 2 to version 3, the implementation time is usually quite long.
The new supplementary metrics are an interesting addition for infrastructure and OT type vulnerabilities, but it should be noted that they do not affect the scoring of the results, their use could be given to highlight specific characteristics of a vulnerability.









