Industrial CVSS: alternative calculations for different needs

CVSS v3, what is it and how does it work?
CVSS is an open and universally used framework that allows you to classify a vulnerability according to its severity. Its use is widespread, especially for IT (Information Technology) environments, but when this framework is used to calculate vulnerabilities that affect industrial devices, different problems arise.
To understand the nature of the same, it is necessary to understand, previously, the metrics used in the CVSS v3, latest version of which currently different scales are available, which, after assessing the different classifications, will result in the severity score final.
In our article “Vulnerability Assessment Metrics: CVSS 3.0” The metrics, as well as the factors that are evaluated in each, are treated in more detail.
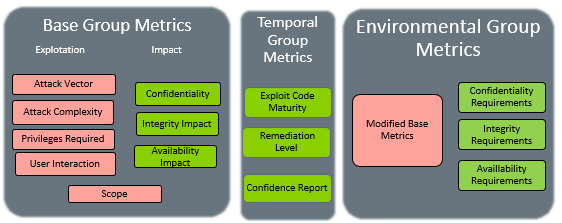
- Metrics corresponding to version 3 of CVSS. -
Using the CVSS v3 calculator in industrial environments
Given that CVSS v3 is oriented to IT environments, different complexities arise when calculating the severity of a vulnerability in industrial environments. The main problem with this calculation is based on the fact that it does not take into account some factors such as impact or environment, among others. To solve this problem, several experts in the sector are looking for alternatives, including RSS-MD, TEMSL and IVSS.
In order to better understand the problem and the alternatives that are proposed, we will take as example a couple of vulnerabilities in which deficiencies have been detected in the calculation of severity and therefore, the final score of these is not very consistent with the impact they would have if an attacker exploits them.
Below are some examples of vulnerabilities where a different valuation can be seen depending on the agency that has carried out the calculation of the severity, since its criteria are slightly different. In these cases, the ICS-CERT considers that the complexity of the attack is high (AC:H), while the NIST considers that the complexity of the attack is low (AC:L).
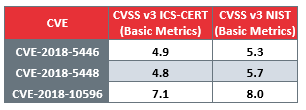
- Comparison of metrics between ICS-CERT and NIST -
Comparison of the CVSS v3 vector between the ICS-CERT and the NIST, for the CVE taken as an example:
- CVE-2018-5446:
- Vector CVSS v3 ICS-CERT: AV:P/AC:H/PR:N/UI:N/S:C/C:H/I:N/A:N;
- Vector CVSS v3 NIST: AV:P/AC:L/PR:N/UI:N/S:C/C:H/I:N/A:N.
- CVE:2018-5448:
- Vector CVSS v3 ICS-CERT: AV:A/AC:H/PR:L/UI:N/S:U/C:H/I:N/A:N;
- Vector CVSS v3 NIST: AV:A/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N.
- CVE:2018-10596:
- Vector CVSS v3 ICS-CERT: AV:A/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H;
- Vector CVSS v3 NIST: AV:A/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H.
To avoid these problems, within the medical sector, the RSS-MD (Risk Scoring System for Medical Devices) is being considered and at a more generic level, the IVSS (Industrial Vulnerability Scoring System) that already incorporates part of its calculation used for the environment part or TEMSL (Threat, Exposure, Mission, Safety and Loss) where other factors such as physical security are taken into account , the objective of the process to which the vulnerability would affect, etc. With these new approaches, it is intended to cover the needs detected by experts in the sector when performing the calculation of severity in vulnerabilities related to industrial environments.
RSS-MD
RSS-MD (Risk Scoring System for Medical Devices) is an exclusive alternative for health sector vulnerabilities that proposes to incorporate new factors, such as the duration of the attack or the chain of exploitation. It is necessary to take into account cases such as the vulnerability in Hospira Plum A + Infusion System (CVE-2015-3956), which allowed the manipulation of parameters in a device that is in direct contact with a patient via intravenous that it is advisable to measure other factors that in the traditional calculation are not contemplated or are not applicable.
On the other hand, and as a contrasting example, we will take the vulnerability in the Medtronic 2090 CareLink Programmer and the URL redirect vulnerability in Schneider Electric Power Monitoring Expert. The first has a calculated CVSS of 7.1; while the second one is 7.4. At first glance, the first vulnerability is less dangerous, however, it could allow a remote attacker to modify parameters of a medical device (with the possibility of endangering the health of patients), while the second allowed the redirection towards a malicious site.
This is another example of the deficiencies shown by the CVSS v3 in certain specific situations that are related to industrial environments.
IVSS
IVSS (Industrial Vulnerability Scoring System) already has a calculator and a description of the metrics and factors evaluated in it:
- Base severity level (BS).
- Base exploitation level (BEX).
- Accessibility, impact and consequences.
- Base score.
- Final IVSS score, made up of all the previous values.
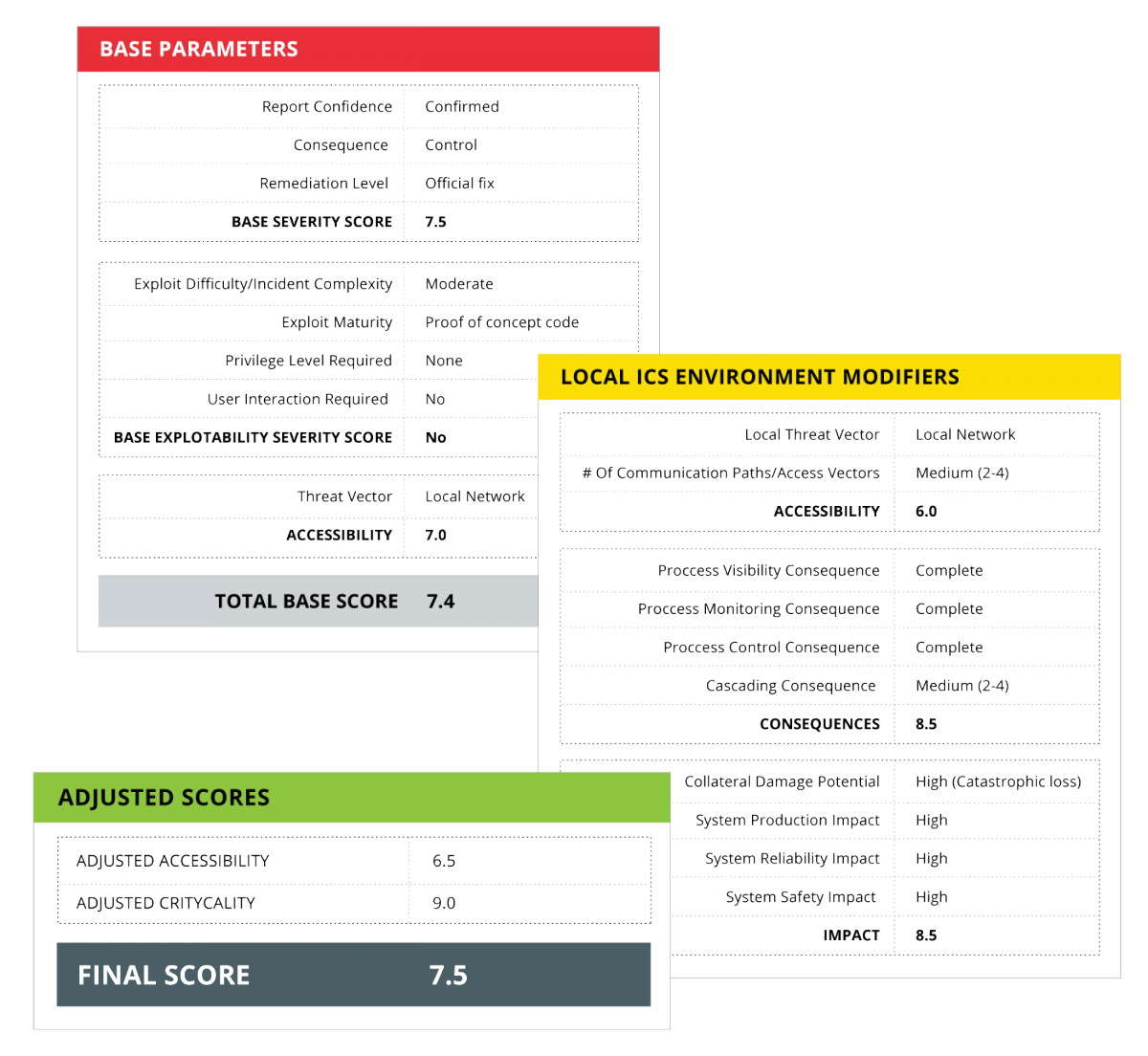
- Example of applying IVSS to calculate the score associated to a vulnerability. Source: S4, Clint Bodungen. -
One of the specific characteristics of this method to calculate the severity associated with vulnerability is that it takes into account the consequences and the impact of it. Among the consequences of being able to assess it correctly is the impact on production, collateral damage resulting from the exploitation of vulnerability, impact on the system safety (physical safety) and the impact on reliability. These consequences and impacts, in some cases, cannot be defined in their entirety, since vulnerabilities are usually detected in laboratory environments. Keep in mind that, although the tests are run in controlled environments, it will always be necessary to keep in mind the location of the device or system analyzed within the industrial process, what other assets could affect it and how it would alter the process in the case that an attacker exploited the vulnerability.
TEMSL
TEMSL (Threat, Exposure, Mission, Safety and Loss) makes the calculation associated to the severity of the vulnerability by means of the use of decision trees, describing:
- Threat: evidence of exploitation of the vulnerability.
- Exposure: reach of the access (external or local network).
- Mission: operation, service delivery, data protection.
- Physical safety: injury or death.
- Losses: costs associated with the exploitation of vulnerability beyond mission or physical security.
The score that can be provided for each characteristic can be 1 (small or non-existent), 2 (noteworthy) or 3 (significant). For example, in the case of the threat, the score that may be associated with said characteristic will vary depending on the following definitions:
- Small or nonexistent (1)
- There is no evidence of a current exploitation of vulnerability.
- Review (2)
- There are rumors about the exploitation of public vulnerability and PoC.
- Significant (3)
- There is direct evidence of the vulnerability implemented in the form of exploit and, in addition, vulnerability reports can be consulted at the technical level.
Each characteristic has defined, based on the scoring levels, descriptions that allow the safety auditor to provide scores to achieve the final score that will define the severity of the vulnerability.
For its part, the establishment of priorities when solving a vulnerability before another is made through a ranking that ranges from never (not to solve), next (solve as soon as possible) to now (obligatorily solve in less than a week).
Conclusions
Although the proposed methods calculate the severity in different ways, all of them have been created with the same idea of trying to adapt the traditional calculation of the CVSS to the industrial environment, taking into account the different needs and in order to more accurately reflect the severity of the the vulnerabilities in the control systems.
Achieving a specific method for calculating vulnerabilities detected in industrial devices is a big challenge given the specific characteristics of each device. Some experts are working in this line to investigate and make proposals to the community to create a “standard” when calculating the severity associated with a vulnerability. Given that within the sectors themselves there are factors that have more weight than others, as in the medical sector with the possible impact of vulnerability, specific alternatives arise.
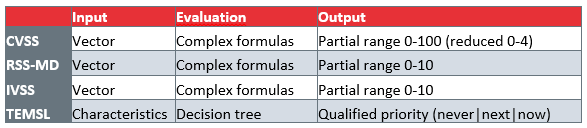
- Comparison between the different calculation proposals. -









