Hive: response and recovery actions
The Hive ransomware, first detected in June 2021, has quickly established itself as one of the most damaging ransomwares of its generation. Throughout its existence, it managed to put more than 1.300 companies from different sectors in 80 different countries in check , obtaining between 100 and 300 million dollars in ransoms (varying depending on the source consulted).

- Hive Infected Countries. Source. -
During the active period from 2021 to 2022, Hive targeted essential sectors, such as government facilities, communication systems, critical manufacturing, and, particularly alarmingly, the healthcare sector.
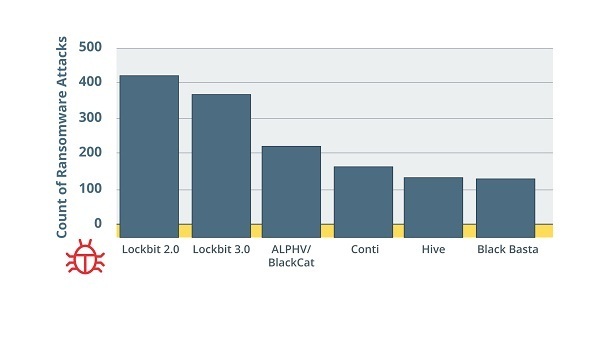
- Most Successful Ransomware Attack Campaigns in 2022. Source. -
On January 26, 2023, the director of the FBI announced the successful dismantling of the network behind Hive, following an international investigation in which the National Police collaborated. This action not only came as a relief to the affected companies, but also demonstrated the ability of authorities to counter large-scale cyber threats.
Characteristics
Motivation
Hive is known for operating under a ransomware-as-a-service (RaaS) model. This meant that the developers were in charge of creating and maintaining the malware, while the affiliates carried out the attacks.
In addition to its infiltration capabilities, Hive introduced another threat: HiveLeaks, a web portal where exfiltrated data can be exposed. In a double extortion attempt, the attackers threatened to release sensitive data on this platform if their ransom demands were not met. This not only put financial information at risk, but also companies' personal data and intellectual property.
During the almost two years of activity, Hive developers produced 6 different versions, of which the v5 version was the one that presented the most evolution. The ransomware was designed to be primarily Windows-compatible, although it features a cross-platform architecture. This was achieved with the choice of languages such as GO (e.g., v3) or Rust (e.g., v5) that offer the possibility of compiling code for multiple platforms, a technique known as cross-compilation . In addition, these languages consolidate all dependencies into a single executable binary and allow the use of concurrent routines to facilitate file encryption.

- Hive Ransomware Variants. Source. -
Infection and spread
Their methods of infiltrating systems were varied and perfected throughout the different versions: from taking advantage of unsecured remote connections (such as RDP and VPN), to distributing malicious emails. But, in addition, it used the exploitation of specific vulnerabilities in widely used systems:
- Microsoft Exchange: The initial indicator of compromise, which put researchers on the trail of Hive, was the successful exploitation of Microsoft Exchange (versions 2013, 2016, and 2019) through the vulnerabilities grouped under the name "ProxyShell". Discovered in August 2021, the ProxyShell vulnerabilities enable Remote Code Execution (RCE). This threat incorporates three distinct security CVEs:
- CVE-2021-34473 (Code Execution)
- CVE-2021-34523 (Elevation of Privilege)
- CVE-2021-31207 (Security Feature Bypass)
- FortiOS: Hive has also been reported to have exploited another critical FortiOS system vulnerability (versions 6.4.0, 6.2.0 to 6.2.3, 6.0.9 and later), being able to bypass Multi-Factor Authentication (MFA) in the SSL VPN. This allowed them to access without requiring a second authentication factor, known as FortiToken:
- CVE-2020-12812 (Security Feature Bypass)
The operation of the attack will depend on the version of the attack. In this article, we focus on version 5. However, there are also other public reports on other versions, such as 3.
Once the initial access is gained, the attacker executes PowerShell commands to download malicious binaries from their Command and Control (C2) server using the Cobalt Strike framework. The malware is downloaded directly into the host's memory and executed using the PowerShell Invoke-Expression cmdlet . Adversaries establish persistence by creating a new user named "user" and adding this new user to the "Remote Desktop User" and "Administrators" groups.
Using system permissions, the attacker invokes Mimikatz, a tool known for dumping credentials. After obtaining the NTLM hash from the domain administrator, the attacker can use a "Pass-The-Hash" attack to take control of the domain administrator account without the need to crack the password. Once inside the network, the attacker performs discovery activities, searching for files that contain the string "password" in their names and collecting IP addresses and device names to amplify the spread.
- Pass-The-Hash Attack Execution via Mimikatz. Source. -
Finally, a process is deployed that encrypts files throughout the organization, leaving a ransom note for victims.
Evasion of detection and recovery
Before beginning the encryption process, Hive takes several actions to ensure effective encryption:
- Terminates specific services and processes: Identifies and terminates a variety of processes and services that are directly related to security, backup, database management, and other applications that could prevent or disrupt encryption. For example, services associated with antivirus software, backup solutions, and running databases can be interrupted to ensure uninterrupted encryption of important files, as it has anti-scan features, such as the NtTerminateProcess API, which terminates the process to thwart scan attempts.
- Disable and alter security services: Make changes to system settings to neutralize security tools that might detect it. An example is disabling Windows Defender through registry changes, or stopping specific services associated with other security solutions. These actions seek to create an environment in which ransomware can operate without being detected or interrupted by security measures.
- Delete backups: Execute commands that remove shadow copies from the system. These backups are backup versions of files or volumes that Windows creates automatically. By removing them, Hive prevents victims from using these copies to restore their encrypted files. Additionally, Hive can make changes to boot policies to make it more difficult for the machine to recover in the event of an attempt to reboot or restore to a previous state.
Deletes and alters logs: After carrying out its malicious activities, the ransomware seeks to delete or alter system event logs to complicate the forensic investigation process and post-infection analysis. Hive executes specific commands to clean up event logs in Windows, such as:
Encryption
Unlike other variants, in the Rust programming language, the attacker has to provide credentials via the command line, being able to specify encryption options, such as choosing between local and remotely shared files. These variant employs advanced algorithms, such as Elliptic Curve Diffie-Hellmann (ECDH) with Curve25519 and XChaCha20-Poly1305. Finally, the variant has a defined list of file extensions that it excludes from encryption, which could indicate a strategy focused on specific types of data.
These advanced techniques and adaptations demonstrate the constant evolution of threats and the need for equally evolved security solutions.
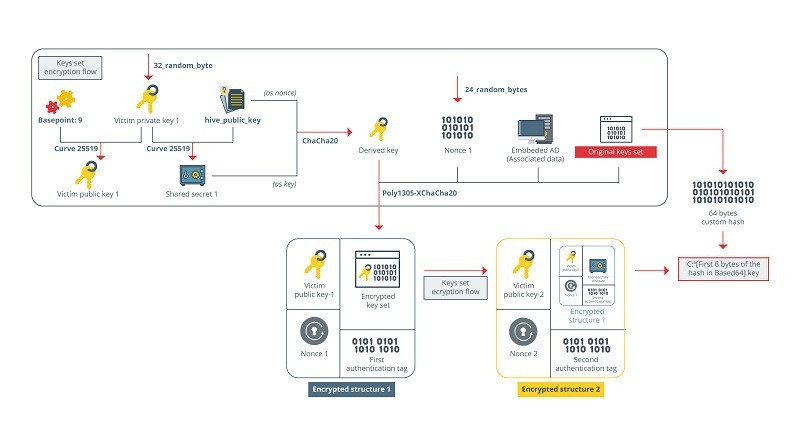
- Hive v5 Encryption Scheme. Source. -
Response & Disinfection
The critical vulnerabilities affecting Microsoft Exchange CVE-2021-34473 and CVE-2021-34523 were patched in April 2021 with the KB5001779 update, while CVE-2021-31207 was fixed in May with patch KB5003435. The CVE-2020-12812 vulnerability in FortiOS was also quickly resolved with an upgrade.
In the case of requiring a system disinfection, a recovery procedure for versions 1 to 4 published by the Korean security agency can be found on the NoMoreRansom platform.
In the case of the v5 version, there is an open-source proof of concept, created by analyst reecdeep, which can help users. The approach that follows is to read the "nonce" (a random one-time seed) of each round of encryption, generating a dictionary of possible keys. Through a specific combination of bytes and comparisons with the keystream, the private key required for file decryption is identified.
Below, we summarize the stages of the process:
- Preparing the Decryption Environment:
- Go to the HiveRansomwareV5-keystream_decryptor folder, download the Visual Studio 2017 project, and compile it.
- Dictionary Generation:
Select option '1' in the program. This option should be chosen first, as it allows you to create a custom byte dictionary for your PC's processor. It's important to perform this step on the encrypted machine to get values that match your keystream.
- Dictionary generation. Source. -
- If the above option doesn't work, generate your own dictionary by running the malware in the debugger (on the infected PC) until the generation of the key in clear text is finished and saves the contents of the memory containing the key. Subsequently, you can validate your dictionary using the "3" option.
- Running the decryption:
- Once you have the correct dictionary, you can run the "2" option even on more powerful computers to reduce the time needed to decipher byte combinations.
- To successfully execute option 2, you need to extract the public key. Since not all Hive examples are identical, extracting this key universally can be challenging. However, a well-known way to do this is by setting a breakpoint after the creation of the nonce and locating where the public key is revealed during the execution of the malware.
- Testing & Validation:
- To test the decryption tool, files have been provided in the dummy_data_PoC folder. Use these files to check how the tool works.
Conclusions
The analysis of Hive v5 leads us to a number of essential conclusions about the current state of the ransomware cyberthreat landscape and the future implications for the cybersecurity community:
- onstant evolution of threats: Hive demonstrates with its advanced techniques, from the development of cross-platform malware to the use of encryption algorithms, such as ECDH with Curve25519 and XChaCha20-Poly1305, the evolution towards more sophisticated cryptomalware.
- Importance of research: File decryption, while a complicated process, is possible with enough research and understanding of ransomware. The cybersecurity community has once again demonstrated its ability to adapt and deal with emerging threats, underscoring the importance of collaborative work and continued investment in research and development.
- Police collaboration: Police collaboration in the prosecution of cybercrime is vital due to the cross-border nature of cybercrimes. This collaboration, as in the case of Hive, facilitates intelligence sharing, the combination of resources and capabilities, and enables rapid and coordinated responses to emerging threats.
- Need for preparedness and education: As threats become more sophisticated, cybersecurity education and training become even more crucial. Organizations and individuals must be equipped with the right tools and knowledge to identify and respond to threats. Preventive and proactive response is critical.









