IDS solutions in industrial environments

Due to the different cyber-attacks suffered by Industrial Control Systems and critical sectors, such as the Wannacry ransomware, which affected approximately 230,000 systems worldwide, the need has arisen to seek greater awareness of the importance of industrial cybersecurity, especially in the case of sectors that handle a large amount of high-value data that make them a target of great interest by well-organized groups of attackers, such as Chermovite or Kamacite, among others.
- Chermovite: This group created the malware known as PIPEDREAM, capable of providing operators with the ability to scan new devices, carry out brute force attacks, connect to servers or even physically break the device. For this purpose, different industrial protocols were used, such as FINS, Modbus and the implementation of Schneider devices.
- Kamacite: this group was the one that used the BlackEnergy malware, which compromised several electricity distributors, causing a Ukrainian region of 1.5 million people to lose power.
For all of the above, in the world of industrial cybersecurity, new methods and technologies are being used that were previously directly related to the IT world. One of these tools is the IDS or Intrusion Detection System.
IDS is an application used to detect unauthorized access to a device or a network, i.e., they are systems that monitor incoming traffic and check against an updated attack signature database for possible intrusion. Over time, this tool has been evolving and adapting to the needs of the OT (Operational Technologies) world, so much so that there are now industrial IDS that can identify devices, such as PLCs and HMIs, or understand industrial protocols S7, Modbus, DNP3, etc.
Moreover, thanks to these IDS enhancements, specific Snort or Yara rules can be introduced for industrial protocols and different alerts can be created so that they can be managed in the shortest and most effective way by the corresponding organization.
As for the types of use of IDSs, there are two types of IDSs, HIDS and NIDS.
- NIDS: focused on monitoring the traffic of the network to which the devices are connected. For this purpose, a TAP (device that replicates the communication that is introduced into a port) or port mirroring of a manageable switch could be used.
HIDS: this type of IDS is based on the monitoring of a specific host, for example, in the TO world it could be installed on a device where you have a SCADA.
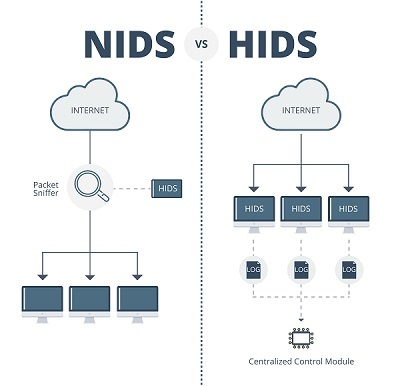
- NIDS vs HIDS. Source -
But this technology is not perfect, as it has some limitations, such as:
- They do not block attacks on networks or devices, as they only monitor traffic and generate alerts.
- Sometimes, if the volume of traffic is very large or if the alert management is not well done, it can cause false positives, which would be detrimental to the detection of real threats.
- Due to the trend of protocol encryption, it is not possible to properly observe the communications of our devices, which prevents us from knowing what data is being sent.
In reference to this last limitation, it is true that, in most cases, encrypted communications provide a certain level of security against possible sniffers on the network, but what if we were the ones who wanted to know what communications are reaching us?
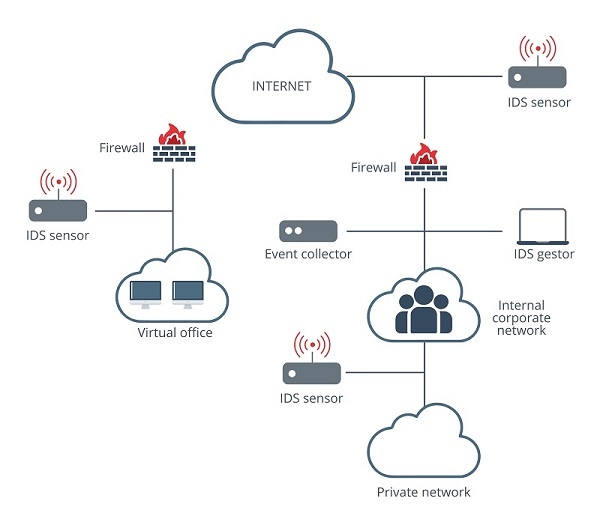
- IDS in network architecture -
In this case, an IDS could be placed on the network and perform a port mirror to send it the information that arrives and thus not slow down communications, since in the TO world what is most important is business continuity and real time communications. The problem we can find in this system is that the warning will take a long time to arrive, since it will have to analyze a high number of packets.
Another option would be to use proxy servers to connect our IDS securely and install or update the signature base. If you want to know more about the use and installation of a proxy server, you can consult our article 'What is a proxy and how to configure it".
For all these reasons, it is advisable to use other technologies or tools to complement IDSs in order to increase the company's cybersecurity.
Complementary methods
Since all technologies have limitations, it is advisable to use different methods to improve industrial cybersecurity. Some of these methods are:
- Network segmentation: it is advisable that the company's networks are well segmented to avoid the possibility of lateral attacks. One of the best examples is to have the IT network correctly segmented with the OT network.
- Honeypots: this technology is based on performing a simulation, as real as possible, so that the cybercriminal believes he is attacking a real target, thus being able to monitor and study all his movements and actions, in order to learn and deploy defensive solutions on real devices.
- Deception: is an evolution of Honeypots, this method stands out for not being a static simulation, but rather, depending on the attacker's actions, different tests are created to find out how far he can go and the methods he uses. All these actions will provide very valuable information for later implementation in the necessary devices. Some of the techniques derived from this method are shown below:
- Lures and honeytokens.
- Fake net traffic.
- Medium interaction lures.
- High interaction lures.
- IPS: It is a technology very similar to that of IDS, but the big difference is that it allows you to block unwanted communications.
Conclusions
As we have seen throughout this article, industrial cybersecurity is a very important aspect, as it allows us to be prepared to respond to possible cyberattacks more quickly, minimizing damage to the industrial environment.
That is why it is advisable to use IDS technology in the TO world, since, unlike other technologies, such as IPS, SIEM, Honeypots, this will allow us to detect cyber-attacks suffered by the company or organization in a faster and more accurate way, avoiding serious or even critical damages.









