Best practices in industrial network segmentation
Industrial network architectures are made up of devices designed specifically for industrial environments, which means that they must be highly reliable in their operation, able to withstand extreme conditions, have a long service life and many other characteristics that differentiate them from other more everyday or IT-oriented devices. The most common industrial devices are:
- PLC (Programmable Logic Controllers);
- HMI (Human Machine Interface);
- SCADA (Supervisory Control And Data Acquisition);
- DCS (Distributed Control Systems);
- SIS (Safety Instrumented Systems).
But due to the large number of connected devices in a factor and the worrying growth of cyber-attacks suffered in this sector, it is necessary to take into account the way to connect these devices. Therefore, experts have been researching and creating models and regulations that allow connections to be made in the safest way and without losing efficiency in communications, such as creating the Purdue model, one of the best known and most used models in the industrial world; or the creation of new applications such as Defense in Depth at the Network level.
The Purdue model and the different assets involved
The Purdue model is one of the best-known standards for the correct segmentation and management of ICS networks. It follows the PERA (Purdue Enterprise Reference Architecture) industrial network concept of the ISA-95 standard.
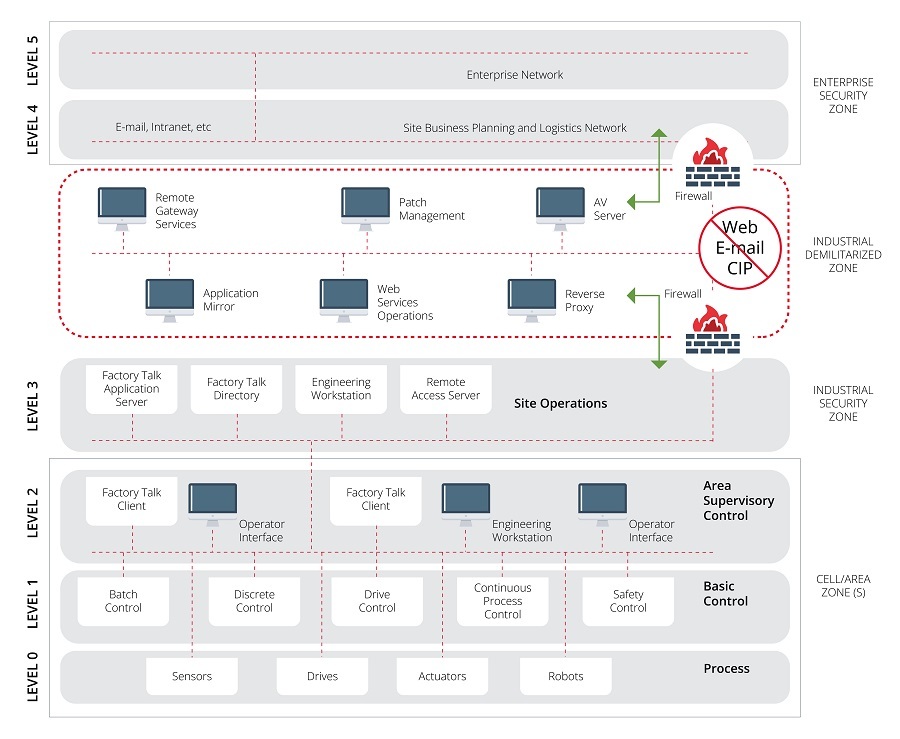
- Purdue model. Source -
In the past, the Purdue model had only six levels, but with the passage of time and the need for a more cybersecure architecture, a new level has been inserted between levels three and four, as shown in the illustration below.
- Level 0: Formed by field devices that allow to obtain data or perform actions for the correct operation of the plant, such as sensors and actuators.
- Level 1: Devices that control actuators and sensors and also send information to other devices located at a higher level. PLCs are usually found at this level.
- Level 2: Assets that control and monitor the activities so that the operation is correct.
- Level 3: This level is very similar to level three, since it is also where plant operation is managed, but this level differs in that there are servers, engineering stations and remote access.
- Level 3.5 (DMZ): This level is located between levels three and four and allows separating the IT and OT part of the company. This zone is very important, as it prevents or at least makes it difficult for cyber-attacks on the IT side to pass into the OT zone or vice versa.
- Level 4: IT systems that support the production processes in a plant.
- Level 5: Usually where a corporate network is located.
Defense in depth at the network level
This cybersecurity strategy is based on a series of layered, redundant, defensive measures to enhance the protection of sensitive data, personally identifiable information and other aspects. This strategy can be used for different assets, such as and endpoint .
In the following image you can get a more representative idea about this application.
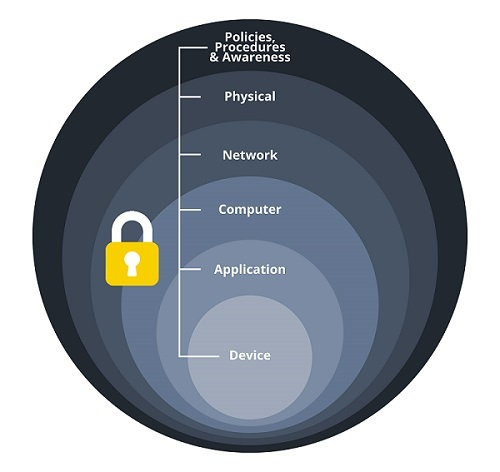
- Layers for defense in depth. Source -
The parts into which this Application is divided are as follows:
- Policies and procedures: Provide a means for management to guide the security program.
- Physical: It is advisable to limit physical access to non-authorized persons.
- Network security: Aimed at defending the network and the devices on it. Different methods can be used for this purpose, such as network segmentation, data diodes or the use of firewalls.
- Equipment: Designed to protect and strengthen computer systems, such as patch management, removal of unnecessary or risky applications, closing of unnecessary logical ports and protection of physical ports.
- Application: This is where end users interact with the system, through APIs, portals or other interfaces.
- Device: This layer includes patching, access restrictions, both logical and physical, or device hardening.
Conclusion
As can be seen, cyberattacks suffered in the industrial world are growing considerably, this is due to the fact that it is one of the sectors where the maturity of cybersecurity is currently low and the problems that can be caused by suffering a cyberattack are very serious.
Therefore, thanks to the creation of the methods discussed above, it is possible that industrial cybersecurity will continue to evolve and improve, so that in the near future the vast majority of industrial plants will increase the maturity of cybersecurity, so that when they suffer a cyberattack they can act as quickly as possible and thus reduce or avoid the damage that may be caused.









