The importance of radio frequencies in industry

In today's industrial manufacturing plants, you can find all kinds of devices and machines designed to perform very specific tasks, many of which require the assistance of an operator to issue commands and instructions on how to perform the job. There are several ways of doing this, but one of the most common is the use of remote-control devices that allow interaction with the machine via radio frequency (RF) communications, which provides a higher level of safety for the operator, as getting close to the machine is not needed.
These remote-control devices are very similar to those used in everyday life, such as a garage door opener, although they can also have other formats, with different shapes, sizes and inputs (buttons, joystick, touch screen, etc.) depending on their function. What all devices have in common is that they make use of a transmitter, responsible for sending the commands executed by the inputs via radio waves, which are then interpreted and executed by a receiver.
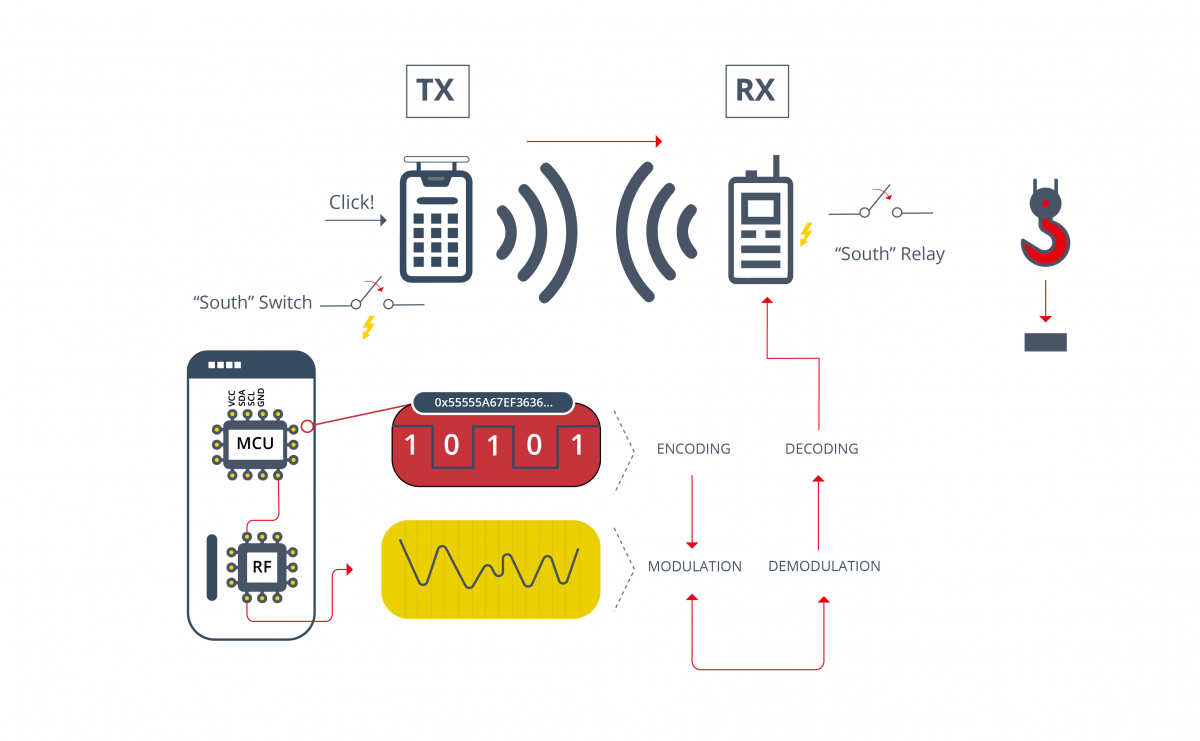
- Example of a connection between a transmitter and a receiver to execute an order -
The frequency of the waves is what determines the range and speed at which the information is transmitted so, depending on the volume of information to be handled and the distance separating the transmitter from the receiver, the frequency best suited to the needs of the task for which it is to be used is chosen. The radio frequency spectrum covers the frequency range between 3kHz and 300MHz and the higher the frequency, the higher the speed of transmission, while the distance over which it can be transmitted decreases.
Applications in the industrial world
In recent years, the use of RF communications in industrial environments has expanded significantly and the devices that make use of it range from tiny sensors to large machinery such as cranes or construction machines. The possibilities that this technology offers are countless, some of its main applications are:
- Remote monitoring. Sensors form part of the vast majority of manufacturing plants and one of the most effective methods of transmitting data and detected anomalies is via RF, with Wi-Fi being one of the most widely used technologies due to its great capacity to transfer large volumes of information. In addition, RF sensors are simpler to install than traditional sensors, as there is less wiring to organize, and it is sufficient to ensure that the signal is strong enough. This, coupled with the advent of 5G technology, which transfers even greater volumes of information at higher speeds, makes RF sensors one of the most viable options when it comes to installing a type of sensor.
- Remote control. Although many of the machines that can be found in the industrial environment implement automated processes and do not require an operator to perform a task, there are still some that are intended for more customized tasks and vary on a project-by-project basis. Examples include cranes or construction machines, which require an operator to run them and send commands to them. These machines can put the operator's life at risk, as the operator is forced to stay close to the construction site where the machine is performing actions. As a remedy to this problem, designs have been developed to make use of RF communications so that, although the machines still require the services of an operator, the operator can control them while maintaining a safe distance, thus avoiding many work-related incidents.
- Communication between team members. As in everyday life, radio frequencies are also important when it comes to communication between people in an industrial environment, as it is common for employees from different areas to communicate with each other to report on different aspects and specific situations.
Attacks on industrial environments
It is evident that RF communications facilitate work in the industrial world and provide a high degree of safety for its employees, but it is not all positive because, from a cybersecurity point of view, most industrial machines that make use of this technology do not implement sufficiently robust security protocols. As a result, an attacker could intercept communications and execute various types of attacks, including the following:
- RF Jamming. Jamming is used to describe a type of intentional interference, known as a Denial of Service (DoS) attack, which can use a brute force method to overwhelm a signal or emit relatively low power signals to overwhelm security communications systems. These attacks are carried out using jamming devices designed to emit radio frequency signals (or noise) in specific bands to overwhelm the intended legitimate signals.
- Replay attack. In this type of attack, using a transceiver, the attacker captures the commands issued by the operator and stores them, and then transmits these commands in an arbitrary manner.
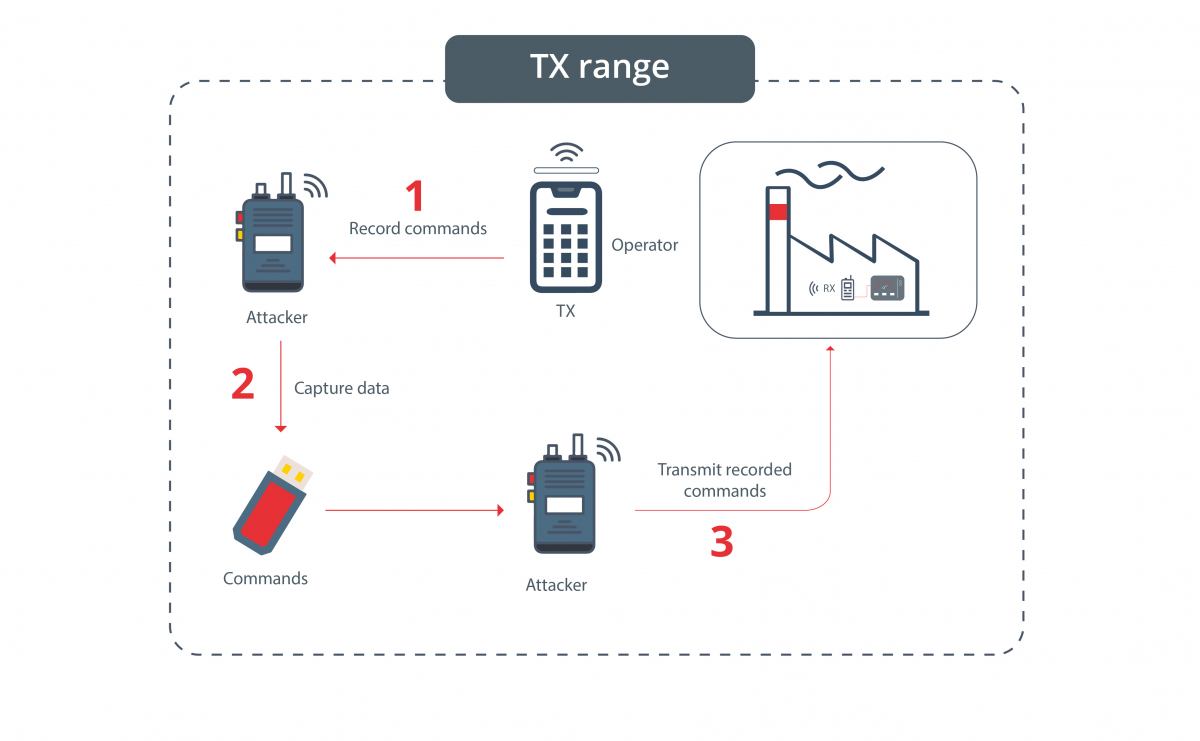
- RF communications replay attack -
- Command injection. To carry out this attack, the commands launched by the operator are captured, but unlike the Replay attack, the RF packets are modified in order to execute different types of commands and gain greater control over the machine. The difficulty of this attack is high, since to modify the packets, it is necessary to know the RF protocol used.
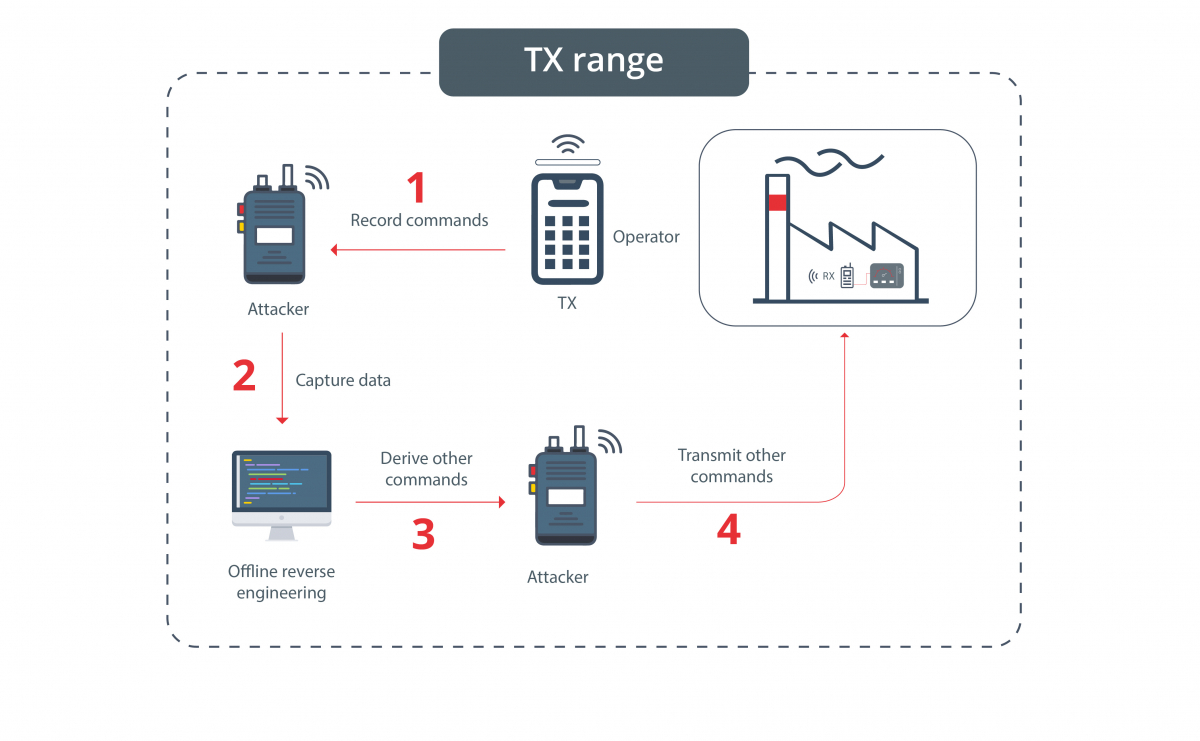
- Radio Frequency Command Injection -
- Malicious pairing. If the attacker manages to capture the pairing sequence, he can clone and impersonate the original remote-control device.
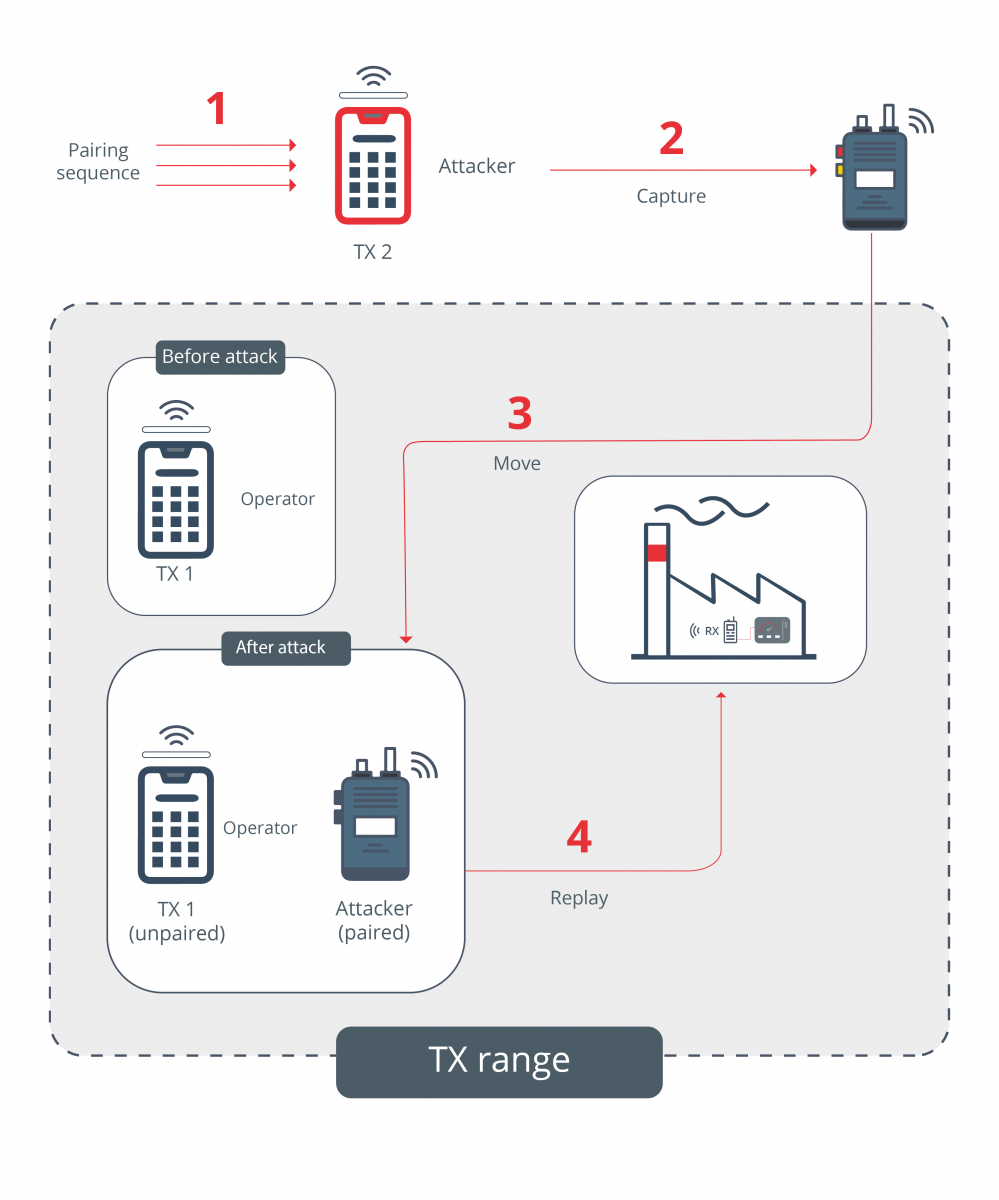 - Malicious pairing of a device by an attacker via RF -
- Malicious pairing of a device by an attacker via RF -
Most of the RF devices used in everyday life make use of standardized protocols that ensure a high level of communications security, making it difficult for the aforementioned attacks to be carried out. In industry, however, fault tolerance is prioritized over communications security, and RF protocols are defined by each vendor. As a result, communications tend to be more insecure and thus become a target for attackers.
One of the examples that demonstrates this comes from Japanese cybersecurity software company Trend Micro. In 2019, its research team managed to breach the security of RF communications from seven major industrial crane suppliers, using a software-defined radio with which the researchers were able to execute a replay attack.

- Remotely controlled crane -
Conclusions and best practices
RF communications offers a multitude of possibilities in the industrial world and is a technology that brings comfort and physical safety to the employees who use it. However, its implementation is still under development and there are certain aspects and practices that can be improved. To avoid putting devices at risk, it is recommended that the following cybersecurity practices be considered:
- Keep software up to date. When a vulnerability is detected in a product, vendors often release security patches that protect the product and should be installed. It is therefore advisable to implement software update policies that allow you to install the latest versions available for your RF devices.
- Make use of standards. Currently, each vendor implements its own communication protocols, but if all vendors used standardized protocols for RF communications, as commercial devices do, the security of RF communications would increase, as these protocols address the different attacks to which devices can be subjected.
- Consider next generation products. When devices need to be replaced, it is advisable to replace them with more modern and, if possible, dual-technology devices (e.g., infrared plus RF communication). It is also recommended to prioritize devices using standardized protocols over those using custom protocols, which are likely to be more insecure and contain more vulnerabilities.
In short, RF communications bring so many positive points and are so useful that they have become indispensable in the industrial world, to the point that it is difficult to find a work environment where this technology is not used. However, its implementation and the way it is used often lacks sufficient cybersecurity, which could have serious consequences that could jeopardize both the health of employees and the company's production.









