Asset inventory and security management in ICS

The asset inventory makes up the first part of a chain in the system security management system. An assets inventory is defined as a list of all those resources (hardware, software, documents, services, people, facilities, etc.) of value to the organisation and therefore need to be protected from potential risks.
In order to adequately protect industrial control systems, organisations can no longer rely solely on traditional focuses based on IT or the physical system for cybersecurity asset management. Threats continue to evolve and attacks on critical infrastructure and industrial control systems are increasingly more sophisticated and frequent.

-Special functions to improve security-
It is common to find an incomplete or non-existent assets inventory in security control systems, which are one of the biggest inconveniences when tackling other security measures in these systems. You cannot protect what you are not aware of; therefore it is very important to make an assets inventory available, up to date and adequately revised.
Classification of assets in the inventory
The information compiled in an asset inventory varies depending on its scope. It is recommended to have a security team in charge of its management and updates, as well as its annual revision and after each inclusion or removal of assets. This team will be responsible for tasks such as defining, inventing and categorising the different assets within the control systems, as well as the internal and external networks, according to the scope of the inventory.
The inventory must have a global focus that includes all the systems within its scope and must also include PLC, DCS, SCADA, as well as the supervision elements such as HMI and other devices and auxiliary systems.
In order to make management and maintenance of the inventory easier, it is convenient to classify the assets into categories, according to their nature:
- Data: All data (regardless of format) that is generated, collected, managed, transmitted or destroyed. Databases, documentation (user manuals, contracts, standards, etc.).
- Applications: The software that is used for managing the process. SCADA systems, HMI development tools, developed applications, operative systems, firmware devices, etc.
- Industrial Hardware: Physical equipment necessary to develop industrial labour (remote terminals, PLC, IED, PC, servers, mobile or hand-held devices, etc.)
- Network: Devices connected to networks (routers, switches, hubs, gateways, etc.).
- Technology: Other equipment necessary for managing people and negotiating the business (servers, user equipment, phones, printers, routers, cables, etc.).
- Staff: In this category you can find staff from the organisation as well as subcontracted staff, maintenance staff and in general, all those that have access in one way or another to the industry.
- Facilities: Places where the relevant systems of the system are kept (offices, buildings, electrical facilities, vehicles, etc.).
- Auxiliary equipment: This category consists of all those assets that support information systems and are not detected in any of the previously defined types (data destruction equipment, conditioning equipment, UPS, etc.).
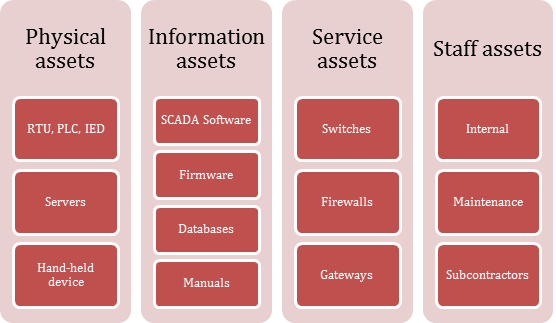
-Example of classification of assets-
Information on each asset
In order to provide value in the evaluation of security and risk management, an asset inventory must provide sufficient information for future projects or incidents, as well as provide a precise vision of the values of same in a way that makes it possible to establish criteria when carrying out a risk analysis.
In order to do this the relevant information must be collected from each system, such as:
- Name: Can include model, brand, descriptive name, etc.
- Description: It does not need to be too extensive, but it must contain information about the use of the asset.
- Identification: Unique code for the asset. It must follow a pattern chosen by the business
- Type: To collect the group that belongs to the asset.
- Owner: Every asset must have an owner. This will be in charge of making decisions such as asset replacement.
- Responsible: The person responsible is the person in charge of making sure that the asset works, as well as managing the assets at the same time. On many occasions this will be able to correspond with the owner.
- Location: Place where the asset is physically found. If it involves a physical asset the location will be a place, if it is a logical asset then the location will be a physical asset.
- Value of the asset: The value assigned to an asset that enables its impact on the system to be evaluated. To do this several guidelines must be taken into account, for example:
- Availability: Qualitative or quantitative value that determines the importance of the absence of the asset.
- Integrity: Qualitative or quantitative value that determines the repercussions for a business in the event of unauthorised modification of the asset.
- Confidentiality: Qualitative or quantitative value that determines the level of confidentiality that the asset requires.
- Criticality: Value that determines the link between the dependency process and the asset. The greater the criticality value, the greater consequences for the business that loses the asset.
- Cost: Economic value of the asset.
Efficient management of the inventory of assets
Keeping the inventory of assets up to date is a costly task that is carried out manually in several ways:
- Time invested in its elaboration
- Ignorance of components or facilities
- Lack of appropriate permissions to access the assets included in the inventory.
Furthermore, it is a task prone to human error. The compiled data is often incomplete and this will worsen the quality of the inventory over time.
In the market there are tools from the IT world dedicated to the inventory of assets that make it easier to identify and document all the hardware and software resident in a network. However, to use these types of tools it is necessary to correctly know its function and the impact that it may have on the control equipment connected to the network. It is recommended to carry out a prior evaluation of the tool in an environment outside production in order to guarantee that its function does not alter the system inventory. The impact on the system of using these tools could be due to the nature of the information or the volume of network traffic that could be acceptable in IT systems but there is no reason for it in the TO systems.
Automated management allows the inventory of assets to be made available in a more precise and efficient way and is, without a doubt, a tool to keep in mind for security reasons as well as for its capacity to return investment, which allows a substantial saving in costs relating to managing incidents.









