Avaddon: response and recovery actions

The Avaddon ransomware made its first appearance in late 2019, but its evolution into a Ransomware-as-a-Service (RaaS) service did not occur until mid-2020, when the malware's creators partnered with a network of affiliates through forums for distribution and marketing. Luckily for its victims, in mid-2021 the attackers behind the development of the ransomware decided to end their activity and leaked the decryption keys completely free of charge through the BleepingComputer portal.
This operating model distinguishes between malware developers, who focus on the infrastructure and operation of the payment service through the Tor network, and affiliates, who take care of distribution using various techniques, such as spear-phishing or exploit-kits.
Although during its period of activity, Avaddon directed most of its attacks at small and medium-sized businesses in Europe and the United States, it is important to highlight the impact it had in Latin America. Specifically, countries such as Brazil, Colombia, Chile, Costa Rica, Mexico, and Peru, experienced high numbers of casualties, including government agencies and a wide range of industries.
- Countries infected by Avaddon . Source. -
Characteristics
A large part of Avaddon's success was due to its link with the Proerpiex/Trik botnets, dedicated to sending spam campaigns, which favored its expansion, thanks to the high success rate achieved in phishing campaigns.
Since its first version, the ransomware has been modified and improved several times, especially when it comes to its encryption mechanism. Early in its expansion, the developers integrated the ability to launch malicious code via Powershell to address Avaddon's enhanced detection by antiviruses. In early 2021, it gained support for Windows XP 2003, as well as resolving some vulnerabilities related to ransomware's encryption mechanisms.
Motivation and modus operandi
Avaddon's business model was clearly geared towards financial gain, as it allowed its affiliates to use malware in exchange for 15–35% of the profits obtained from the ransom of its victims. However, it should be noted as a curiosity that, like Maze ransomware, one of the conditions that the group imposed on its affiliates was the prohibition of attacking victims who were part of the Commonwealth of Independent States (CIS).
In addition, the malware had an executable script that had the ability to detect the language of the victims, so as not to infect those systems with the Russian or Ukrainian language.
As a rule, some of the stolen data was posted on a website accessible from the DeepWeb, as a means of lending credibility to their claims and inciting their victims to pay the ransom. In addition, in case of need, they also used to threaten their victims with DDoS attacks, as a strategy to pressure and speed up payments.
Infection and spread
Like many other RaaS examples, attackers use different attack vectors. As a means of dissemination, it often employs deceptive emails that aim to convince the recipient that there is a sensitive photo of him in the attachments.
Avaddon spread quickly and stealthily through malicious emails with intriguing subject lines such as "Your new photo?" or "Do you like my photo?".
- Example of an email from Avaddon. Source. -
These emails included a seemingly harmless message accompanied by a smiling emoji and an attached JavaScript file that pretended to be an image, with a JPG extension.
- Avaddon download command. Source. -
There is also evidence of the use of other attack vectors, such as the use of RDP services and VPN networks, through leaked credentials, or vulnerable services:
- Fortinet: By exploiting a vulnerability in the SSL VPN firewall, attackers gained access to the domain administrator's account.
- Microsoft Windows: This security flaw, which was also exploited by other ransomware, such as Ragnarok, allows access to the server and obtaining super-administrator access (NT/SYSTEM).
Once inside the targeted system, the attackers carried out the deployment of beacons through the use of the Cobalt Strike framework. These beacons contained the malicious code that allowed the infected machines to be taken over. Among these scripts, there was the Bitsadmin command that downloaded the real ransomware inside the %Temp% folder.
The malware could spread to other network drives and other connected devices, using the victim's ARP cache to identify and scan new networks, targeting CIFS/SMB volumes to encrypt them.
Properties
Malware presents a number of mechanisms to circumvent security mechanisms:
- Anti-debugging: Actively detected the presence of debuggers, tools that security professionals use to analyze and disable malicious software. If it identified a working debugger, it paused its encryption process. This strategy made it considerably difficult for analysts to analyze and neutralize.
- Persistence: The ability to self-replicate and save a copy of itself to a specific folder within the Windows operating system. This feature ensured that, even after rebooting the system, Avaddon remained active. In addition, by integrating with the task scheduler using Microsoft's COM technology, the malware could constantly reboot and operate, consolidating its presence on the compromised system.
- Process interruption: identified and stopped certain running services or applications. These outages were aimed at those processes that could hinder their malicious activities. Not only did this feature avoid potential pitfalls, but it also ensured a higher success rate in their crypto and extortion operations.
- Access modification: modified certain system logs to access network drives that were originally protected or inaccessible. This ability allowed it to expand more quickly, especially in corporate networking environments, where it could propagate across multiple connected systems.
- Disabling Backups: It had the ability to disable Windows' automatic backup features and delete existing ones. Thus, it not only limited the possibility of recovering encrypted files, but also increased the likelihood that victims would decide to pay the ransom, given the lack of recovery alternatives.
Encryption
Once activated, Avaddon searched for and encrypted files with the .avdn extension. It used the Windows CryptoAPI to generate an AES256 key and then encrypted that key with a 2048-bit RSA public key built into the malware.
- AES encryption with public key. Source. -
At this point, the malicious code would travel through the file system, encrypting the contents with the previous AES key. Each of these encrypted files incorporates some data containing its own AES key at the end, to allow for later decryption.
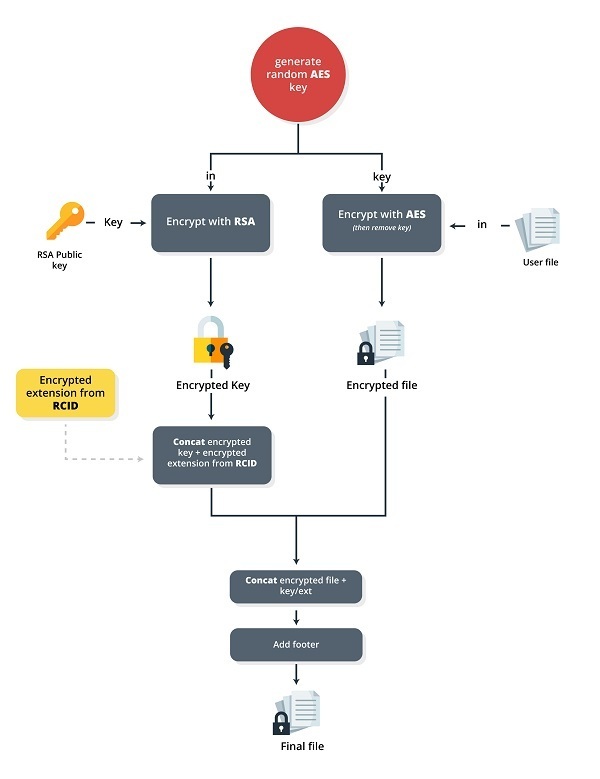
- File encryption. Source. -
Response and disinfection
As a preventive option, it is recommended in any case to patch vulnerable Windows and Fortinet systems, and perform appropriate hardening on our systems.
In the event that you have been infected by ransomware, there are decryption tools from various companies (Emsisoft or Bitdefender) based on the keys published by the developers themselves. Although the decryption process is not foolproof, it has allowed numerous victims, who had not yet paid for the ransom of their data, to recover their encrypted files.
The decryption process using one of these tools, namely Emsisoft's, is described below:
The first thing you have to do is download the corresponding version from the company's website, run the program and accept the terms and conditions. Subsequently, we will select the drives that we want to decrypt.
- Select drives in the Emsisoft tool. Source. -
Within the options tab, you will find different settings and options to select, depending on the malware family.
Using "Decrypt" will start the process. You can see the progress of the tool in the information that will be provided on the screen.
- Final result after the decryption process with the Emsisoft tool. Source. -
In addition to our decrypted data, the tool allows us to keep a record with the summary of the results of the process. All you have to do is click on the "Save log" button.
Conclusion
Avaddon, like many other examples of RaaS, should serve as an example of the advances and facilities that cybercriminals have to contract this type of threat, as well as its constant evolution. Similarly, we cannot ignore or downplay the prevention that organizations must implement to protect themselves from these attacks, especially when it comes to employee awareness and security updates.









