CrashOverride: The malware for ICS is back again
We opened the year 2017 with an article in the INCIBE-CERT blog about a potential new attack to the distribution system of electricity in Ukraine, and today, half a year later, we are again talking about this incident after the publication of several articles on a new malware called CrashOverride. According to reports published by the companies Dragos and ESET, which have published it analysis, this malware would have been the culprit of this incident in Ukraine.
Description of CrashOverride
According analysis published, CrashOverride is a modular malware targeting organisations using IEC101, IEC104, IEC61850 and OPC protocols.
The particular features of this industrial malware are:
- Sends commands directly to the RTU using industrial protocols, including the opening and closing of breakers (substations switches) quickly and continuously, just like BlackEnergy.
- Blocks serial ports of Windows devices, preventing communications between legitimate devices and affected devices.
- Carries out a network discovery through the OPC protocol and a port scanner, considerably improving the probability of success.
- Is able to exploit a recognised vulnerability of Siemens SIPROTEC relays, which can lead to a denial of service.
- Includes a wipe module (deletes data and any other file that could lead to its tracking, or specific files) that renders Windows systems useless and a reconstruction or a backup copy is required to put it back into operation.
Operation
CrashOverride uses functionalities of the three main malware for control systems that have appeared up to now, included in the article on malware families within this field that we published in INCIBE-CERT:
- Imitates STUXNET in the way it understands and represents the knowledge of the industrial process, encoding it to interrupt operations.
- The system architecture is mapped through the OPC protocol, just like HAVEX/ Dragonfly did.
- It also follows the footsteps of BlackEnergy2 when reviewing libraries and HMI setup files to understand the environment and try to connect to the Internet when possible.
This malware is composed of an initial backdoor, a loading module and various adjacent modules, among which we find the modules to take advantage of the industrial protocols. The backdoor provides the main access and allows managing the installation of additional backdoors, as well as communication with the control centre. This backdoor is also in charge of executing the loading module. Said loading module executes modules with payload of industrial protocols and a wipe module.
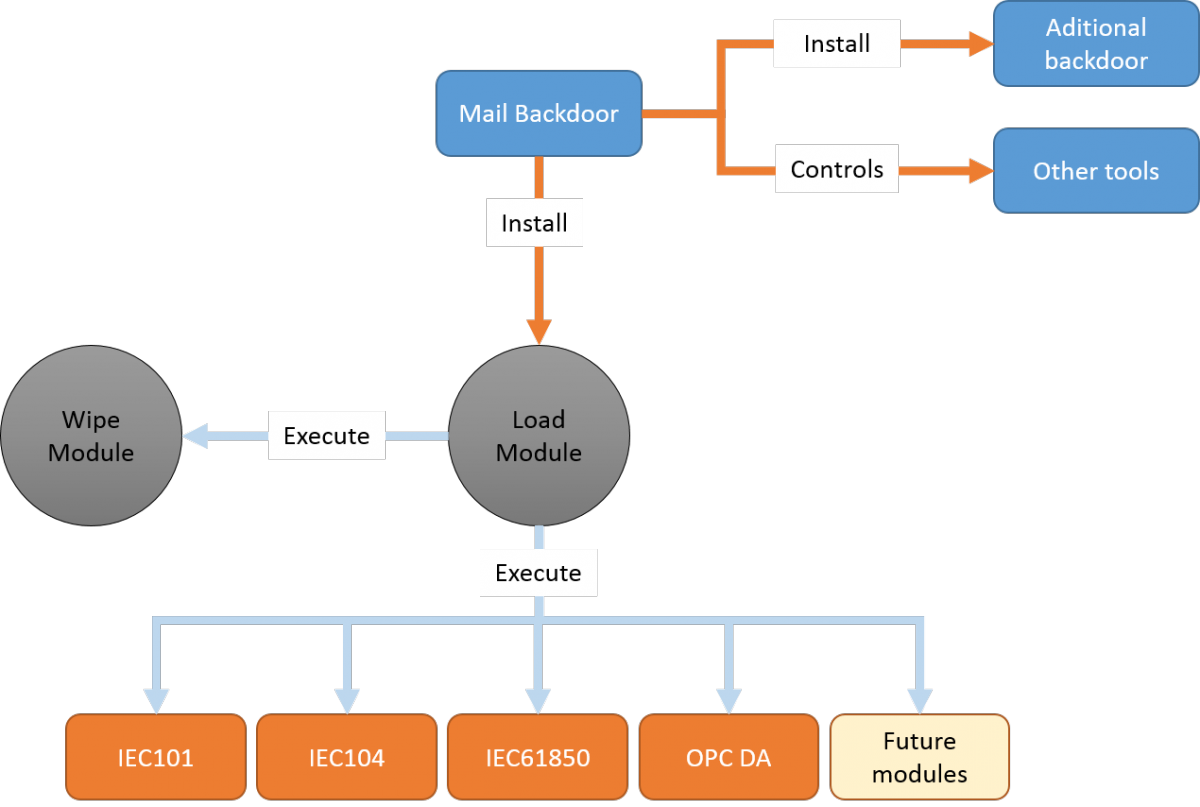
-Operating mode of CrashOverride-
The wipe module deletes all registry keys associated with system services, and also deletes configuration files in the hard drive and those network drives that was able to identify. It is specially parameterised to attack configuration files of the ABB PCM600 device. In addition, it overwrites Windows generic files, rendering the system useless.
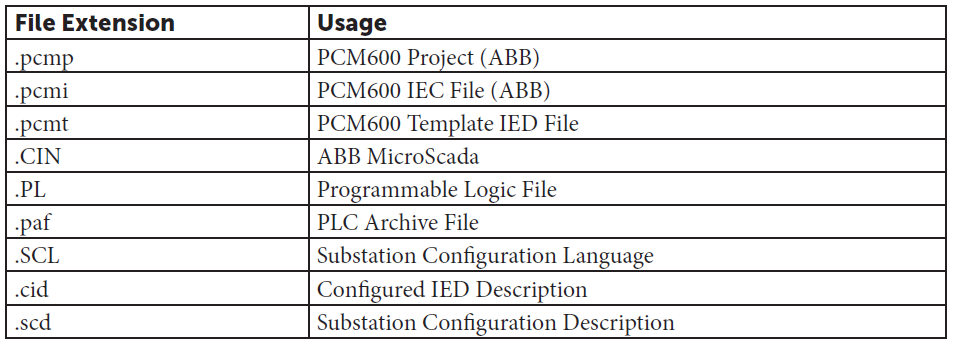
-Main extensions sought by the wipe module-
Up until now, the only modules with payload of protocols localised are related to the European electricity sector (mainly uses IEC101 and IEC104 protocols), but new modules could emerge that allow their use with other protocols, such as the DNP3 protocol used in the USA, or in other sectors (modules for other industrial protocols).
The operation of IEC101 and IEC104 modules consists in terminating communication between the master and the victim's device, impersonating the communication master by sending a series of specific commands, among which we find the continuous opening of breakers or change of status from open to closed and vice versa.
The specific module for Siemens SIPROTEC sends UDP packets to the port 50000 to take advantage of the CVE-2015-5374 vulnerability.
In the case of OPC (Data Access version or OPC DA) and IEC61850, a special module including both protocols has been created, which can be also used as autonomous tool. IEC61850 allows identify configuration files and routes. Module OPC tries to list all OPC servers that are being executed and its items or variables.
The malware analysed until now also included a module capable of performing port scans allowing to choose the range of network and ports to be scanned in order to find relevant devices in the network.
Attack vector and spreading
Reports published up to now do not give indications of how the malware entered the system; nevertheless, given the background of similar malwares, everything suggests that some type of phishing is required to deceive substation operators.
In the samples analysed, it has not been checked whether the malware is able to spread to other devices. The loading module executes the modules corresponding to the protocols so that they perform their actions and it also activates a 2h timer. After that time, the wipe module is executed and renders the system useless.
Implications
The successful use of this malware, as it was the case of power plants in Ukraine last winter, can cause blackouts in certain regions. This is achieved by continuously sending opening commands to a large number of breakers, so that if the operator tries to close them back again from the HMI, all requests are overwritten and the breakers remain open, disobeying the orders of the operator from the HMI.
The other attack option is trying to create isolated electricity distribution areas or islands. To that end, the malware takes advantage of the option of sending opening and closing messages continuously, trying to activate the security mechanisms of the substation to disconnect the network. The aim is to generate instability in the network and spread the effect to other substations.
These two attacks pursue the shutdown of one or more substations, leaving without energy a region that can be more or less extensive.
Through the OPC module, values can be modified by brute force, which would lead to incorrect reports and inaccurate information for the operator.
The Siemens module would try to create a denial of service in the protection relays, neutralising the automatic protection of the substation. This disabling of the protection would allow performing the islanding attack more efficiently.
Protection measures
Ordinary protection measures are always appropriate to increase the security level of a system, but in this specific case the use of data diodes, antivirus solutions or even having AIR-GAP are not valid solutions. It is therefore necessary to perform other series of actions, including:
- Reviewing the use of IEC101 and IEC104 protocols and researching any type of traffic increase. This measure must also be extended to other protocols that could be targeted in the short term, like DNP3.
- Verifying protocols communications and making sure that no new communications are started with devices that did not have same before.
- Monitoring OPC communications, specially focusing on the location of potential network discoveries carried out through this protocol.
- Making sure you have backup copies that cannot be modified or invalidated by this or other malware.
- Preparing a response plan against this attack and performing training exercises in all departments that may be affected, both IT and OT departments.
- Applying a system of detection and prevention of intrusions that allow carrying out a deep inspection of the exchanged traffic, enabling the detection of new functions in the protocols or network discoveries.
- Using the YARA rules and indicators of compromise published to check if our system is infected.
This is neither the first nor the last malware that will affect control systems. Malwares are increasingly targeted and specific, and even if for the moment all of them are aimed towards the electricity sector, the rest of the environments should not economise on their cybersecurity programmes.









