Cyberchallenges to security in industrial robotics

In the context of industrial cybersecurity, there is no single wall that stops all cybercriminal attacks, but there are numerous systems, each with its own security. Therefore, the threat protection system will be as strong as the weakest link.
Industrial robotics is another link in the industrial system that needs concrete measures so that it is not vulnerable to cyberattacks. So far, the industry has been paying attention only to physical safety in the context of robotics. Cyberrisk, on the other hand, is not being taken into account, since no attack on an industrial robot has yet been recorded. Despite this, a simple cyberattack on a robot could cause huge losses due to a stoppage in the production chain and the damage that it may cause by malfunctioning.
Robotics plays a very important role in Industry 4.0, characterised by the trend towards automation and smart factories. The International Robotics Federation (IFR) stated that, in 2018, 1.3 million industrial robots were installed with an upward trend over the subsequent years.
Requirements in industrial robotics
All systems that interact with a robotic device must meet the following requirements:
- Precision: robots need highly precise sensor measurement to optimise their movements and reduce production uncertainties.
- Physical safety: the safety of operations for infrastructure and plant workers must be guaranteed.
- Integrity: the robotic controller must minimise the probability that a logical control causes the robot physical damage.
How to defend automated robotic systems?
When security measures are implemented in robotic systems, an organisation must take into account the mechanical structure, the part related to human management and the software directing the robot. A safe design should include the full cycle, from requirements, selection, architecture and implementation, to operations that are underway.
- Government:
- Establish structures with clearly defined roles and responsibilities.
- Management of the threats identified through a risk management program.
- Security of software and product:
- Conduct periodic security analyses of the solutions implemented in robotic systems to identify possible faults in the connections or in the authorisation of the products connected to the robotic devices.
- Scan the bots created for vulnerability detection, using dynamic testing or fuzzing technology.
- Conduct data flow reviews to check that the safety controls work correctly in terms of authorisation and authentication.
- Identity and digital access:
- Implement the mandatory use of passwords at the start of robotic sessions and centralise the robotic identity and access of management processes.
- Manage user access privileges to obtain a security matrix that authorises bots to perform only the tasks assigned to them.
- Data protection and identification:
- Carry out an assessment of compliance with data regulations to monitor their confidentiality.
- Monitoring of the sensitive data processed by robotics to verify compliance with usage policies.
- Security operations:
- Collect events from the controller’s log to audit the activity trail and thus detect anomalies or access to systems with unauthorised privileges.
- Vulnerability scan of the robotic platform that is used and perform threat modelling exercises to determine technical weaknesses and security breaches.
- Implement a piece of hardware in the automatons, to act as a firewall constantly to analyse the orders that the device receives and, allowing or refusing them after consulting with a third machine that has all the automaton’s rules.
- Vulnerability management:
- Direct communication with the manufacturer to be aware of the vulnerability bulletins they publish to check if there are affected computers in the installation.
- Apply a device patching policy that clearly documents how to update, change configurations and create backups for the machine.
- Security of communications:
- Use protocols with encryption to ensure the integrity of the messages.
- Implement end-points in automatons to detect possible infections.
- Collect the robot’s data and the subsequent network audit, in order to find vulnerabilities in the robotic systems or connections and thus to be able to redefine the industrial network architecture to make it more secure.
Types of cyberattacks
In the area of industry, robots are normally configured through high-level commands by programmers or controllers that connect through remote access. In this process, an attacker could exploit certain vulnerabilities if the user has failed to take certain security measures.
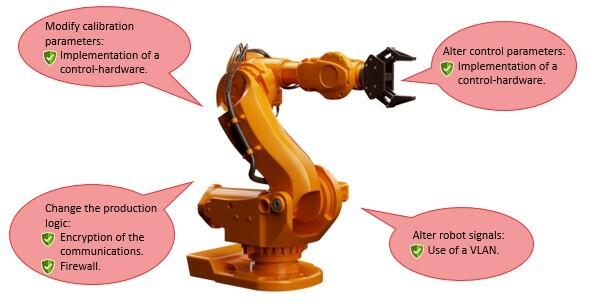
-Attacks and solutions in the robotics industry-
Most of the software used for programming and managing industrial robotics are not up- to-date in terms of encryption or libraries. Other problems identified are weaknesses regarding authentication, reliance on embedded credentials and even the use of public IPs in microcontrollers. Some of the cyberattacks to which a robotic device may be subject are as follows:
- Alteration of the control parameters: in this attack, the values that control the robot are modified, causing it to move unexpectedly or inaccurately.
- Modification of the calibration parameters: the first time one connects to the system or after any modification, the machine’s sensors are calibrated. The calibration data is saved on the device itself and subsequently sent to the controller.
- Change to production logic: if the controller does not ensure end-to-end integrity of the program, an attacker could randomly alter a task.
- Alteration of the robot’s signals: erroneous signals from the automaton would be sent to the management application. This may produce false alerts or stoppages in the production line.
In the summer of 2018, Brown University published an article pointing out more than one hundred open connections between servers and the robotic device control platform, called ROS. It was found that it was possible to obtain the video image of the robot and even to take remote control of the robots by sending movement commands. Working behind a firewall or a VPN is a solution that would solve this problem.
Future trends in industrial robotics
The use of robotics is transforming most industrial systems. This transformation is influenced by various trends:
- Implementation of the Internet of Things: more and more, robots will use smart sensors to gather information, which was hitherto unknown to manufacturers, and to improve the efficiency of processes.
- Use of Big Data analysis: the parameters gathered in robots must be organised in systems to be analysed and to obtain reports about, for example, the status and maintenance of the machine.
- Use of virtual solutions: virtual solutions make it possible to represent robotic systems and proofs of concept without having to interrupt production.
- Use of open automation architectures: in this case, coordination between manufacturers and system integrators is needed to produce standards and documentation that makes it easier to introduce robotics.
All these new trends open up new input and output routes from and to the Internet in industrial systems, thus making possible the leakage of information about our devices and production parameters easier, so new security measures must be introduced when the new services are commissioned.
Conclusions
Since its advent, the development of industrial robotics has not been matched by effective cybersecurity. Greater awareness is needed on the part of all the actors involved in the development of industrial robots, not just plant operators. Currently, there are scarcely any companies specialising in this area, which makes it difficult to tackle it and to raise awareness in a growing number of companies of the importance of OT cybersecurity.
Fortunately, the design and definition of security in the IoT field is an important advance in robotic cybersecurity, given their great similarity. Thanks to this, there already exist defined measures that will entail more straightforward integration in the future.









