Cybersecurity in Industry 4.0

Towards a new industrial revolution
The term Industry 4.0 was coined and mainly developed in Germany,and describes a new way to organise means of production. Today, industrial processes demand a high level of connectivity between components, whilst still retaining basic requirements such as business continuity and high availability. New, intelligent manufacturing processes are therefore needed, which are better equipped to adapt to production needs and processes, and to a more efficient resource allocation. A new industrial revolution has therefore come about: the fourth industrial revolution.
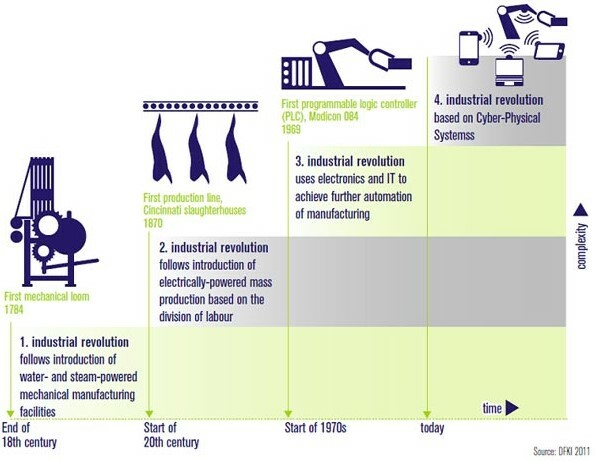
-Industrial revolution (Source: DFKI 2011; Centre of German Research for Artificial Intelligence)-
Against this backdrop, ICT is becoming more and more important in industry. New processes can only develop through the exploration of those opportunities provided by new technologies. Cloud architectures are emerging (the term “the fog” being coined to replace “the cloud”), along with ubiquitous computing, Big data and virtualisation; technologies with a scarce presence in industry.
Traditional operations and support in information technology are starting to blur the boundaries between the real world and the virtual one in what are known as new systems of cyber physical production (CPSS - Cyber Physical Production Systems).
Characteristics of Industry 4.0
Industry 4.0 is defined as one step in a series of differentiating features which aim to integrate other intelligent infrastructures such as mobile or logistic infrastructures and intelligent buildings, and to accelerate technological change.
Under these premises, several characteristics are considered representative of industry 4.0:
- Vertical networks allow for a rapid response to dynamic changes in demand and/or stock and in possible errors. Emphasis is placed on resource efficiency, and particularly on efficiency in materials, energy and human resources.
- Horizontal integration succeeds through new networks of value chains. New networks work in real time, allowing an integrated transparency and offering a more flexible and robust service.
- Intersectoral engineering means different disciplines interact through engineering throughout the entire value chain and throughout the life cycle of the development of products and services, allowing new synergies of different agents, which lead to improvements and add value.
- Acceleration is possible thanks to the exponential growth of technologies, which acts as a catalyst for the creation of individual, flexible and productive solutions.
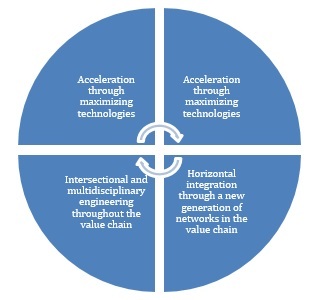
-Characteristics of Industry 4.0. Source: Industry 4.0. Challenges and solutions for the digital transformation and use of exponential technologies-
Industry 4.0 and Security
The high level of connectivity that Industry 4.0 requires has led to the introduction of systems which are more open and serve a general-purpose, like those that have been used in ICT for years. These days, industrial control systems that permanently connect via TCP/IP and Ethernet are a common sight, as is the use of standardised wireless systems. All these protocols have been developed and analysed thoroughly, and they offer the maturity and reliability that the new Industry 4.0 demands.
Introducing well known communication facilities into control systems brings a host of benefits, but this also makes these systems more visible and makes them vulnerable to certain risks, and they have to be managed correctly. For this reason, Industry 4.0 opens up a wide range of possibilities, but also puts systems in a position with a considerably larger number of threats.
Better connectivity, more facilities…but a greater risk
Data published in recent years on attacks to industrial systems indicates that the situation is getting worse, with more attacks being directed at control systems. Symantec illustrates this in its Internet Security Threat Report, dedicating an entire section exclusively to industrial cybersecurity. In 2012, McAfee confirmed that “attackers often choose systems that can be easily compromised, and evidence suggests that SCI is particularly vulnerable” in its reports on Threats Predictions, which is issued annually and describes industrial threats. Similarly, Verizon also publishes a number of reports each year on this topic.
Meanwhile, SMEs tend to struggle to improve their cybersecurity, since they often do not have the specific equipment required. There are ultimately no affordable turnkey solutions (complete development from beginning to end) for protecting systems, and the information available about the threats is limited and unconsolidated. Furthermore, those big businesses forums that do exist for the exchange of information are often beyond their reach.
Cybersecurity challenges in Industry 4.0
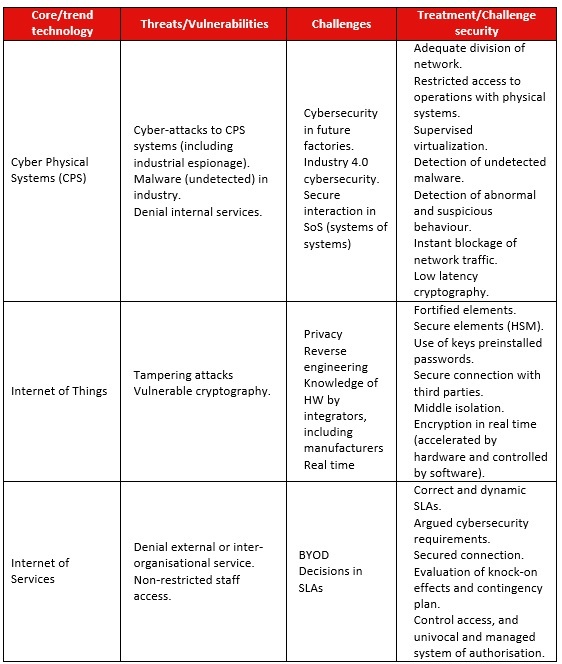
Cybersecurity in Industry 4.0 has an immediate effect on CPS, the Internet of Things (IoT) and the Internet of Services (IoS).
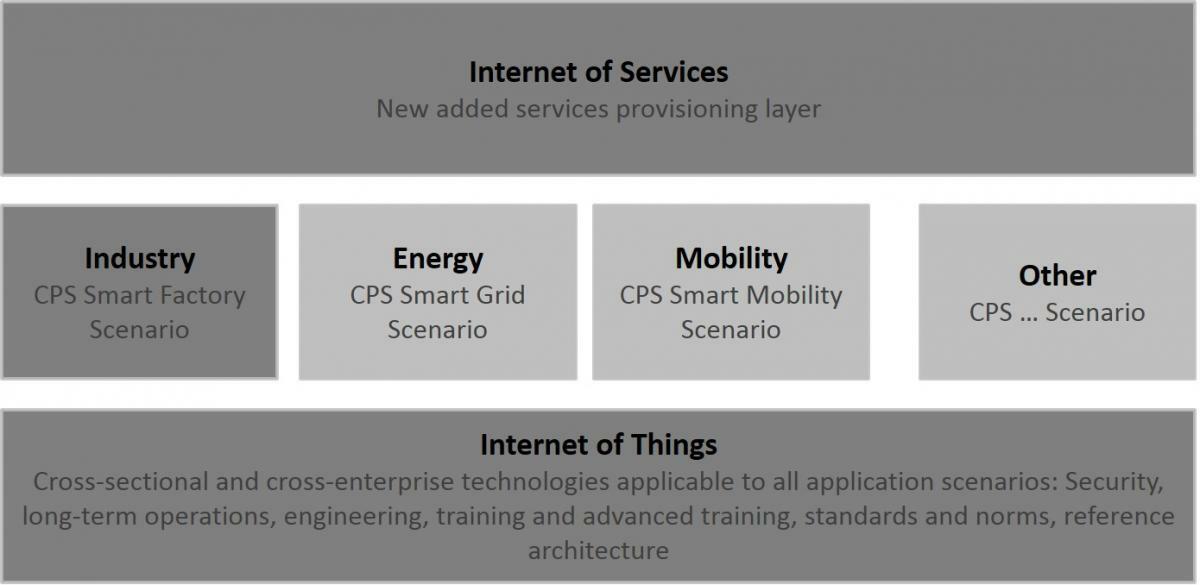
-Industry 4.0 and its connection with Internet and Information and Communication Technologies. (Source: Germany Trade & Invest. 2013)-
- CPSs (Cyber Physical Systems) are systems which monitor physical systems, create a virtual copy and make decentralised decisions. The sensor system and control elements are able to connect the machines and devices with installations, vessels, networks and human beings.
- Internet of Things (IoT): CPSs act on the Internet of Things. This paradigm ensures that devices and elements are connected to Internet-based protocols (TCP/IP).
- Internet of Services (IoS): This paradigm offers many internal factory services horizontally throughout the value chain.
These are the distinguishing features of Industry 4.0, in terms of technology and processes. Each brings its own range of threats, vulnerabilities and possible challenges/safeguards with regard to cybersecurity. Below, a number of these are outlined:
A step forwards: Good practices, work groups and reference architectures
The boom in Industry 4.0 and, in particular, in cyber physical systems (CPS) has attracted the interest of many businesses and institutions. This interest is clear from the development of regulations, frames of reference and institutions and businesses which aim to undertake further research in this field:
- The German government has determined a road map, together with its architecture, in a report explaining its strategic plan for 2020.
- Various European institutions have come together to form a group named EICOSE (European Institute for Complex Safety Critical Systems Engineering), which researches security for critical systems. Their three work groups focus on developing methods, processes and systems which guarantee security in critical embedded environments.
- The Spanish Government has launched the project Connected Industry 4.0. The project, which operates both publicly and privately, aims to encourage a digital transformation in Spanish industry. In particular, it has three core aims:
- Boosting value added industry and qualified employment
- Promoting the Spanish model for future industry
- Driving exportation
- At a regional level, it has the following initiatives:
- Basque Industry 4.0: An initiative that Euskadi hopes will strengthen Basque industry through the use of intelligent factories, significantly increasing productivity and employment
- Competitividade Industrial Galega Industria 4.0: This Xunta de Galicia initiative aims to promote the industrial technological revolution, creating 50,000 new jobs and increasing the weight of industry in GDP to 20% by 2020.
Industry 4.0 is still a developing concept, but it is already having an impact across Europe, and all the evidence suggests that it will prove unstoppable. Cybersecurity is essential in order for Industry 4.0 to work, not only in technological terms, as previously mentioned, but also in terms of the processes in the value chain: the risks and responsibilities need to be defined for each of the agents.
Cybersecurity must therefore be thought of as a protective mechanism, but also, especially, as a basic requirement in order for business to continue.









