Honeypot, a tool to know your enemy

Several honeypots projects -hardware systems or software tools which simulate vulnerabilities so they can be exposed with no risks and allow monitoring of the attacks launched against them- have been created over recent years. Most of these projects are developed for IT environments, but several honeypot projects have also been created for OT environments, such as Conpot or GasPot, among others.
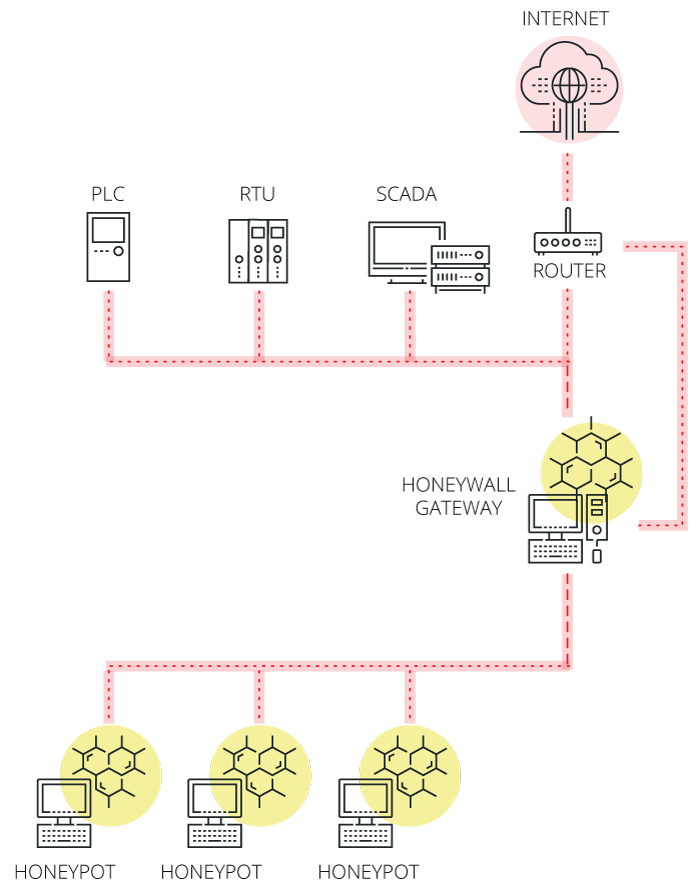
These honeypots have evolved and are currently being implemented in the form of honeynets; networks consisting of honeypots which simulate complete systems, thus allowing the collection of much more information on the attacks.
Honeypots can be classified based on the degree of complexity required for their implementation and the level of interaction with the attacker allowed. This way, a honeypot is classified as low-interaction honeypot when it only simulates services and operating systems; these can be easily used and kept, and the risk involved is almost nil. Unfortunately, they are usually easily identifiable by the attacker, so they are normally only targeted by automatic or automated attacks, and the information registered by them is rather limited. Moreover, honeypots classified as high-interaction honeypots are usually real applications running in real systems. For this reason, they can collect much more information about the attackers than low-interaction honeypots. However, attackers could use these honeypots as an access point for other systems and, therefore, they require additional security measures to ensure that no systems are compromised.
Honeypots in SCI
The large amount of elements of OT systems to be found on the Internet, which are easily traceable by means of meta-search engines such as Shodan and Censys, proves the lack of sufficient security mechanisms (example: encrypted communications, two-factor authentication, etc.). For this reason, it is useful to obtain as much information as possible regarding the attackers, their methodology, potential targets and systems so we can anticipate eventual attacks and improve our level of response to any incident that arises.
Implementing a honeypot can be a good way to obtain said information, provided we make sure that it meets our needs and we take into account certain requirements:
- It must be as complete as possible in order to prevent the attacker from detecting it and avoiding the trap. Some automated tools have honeypot detectors, such as Shodan's honeyscore, which is able to identify if an IP address belongs to a honeypot and rate it based on a probability.
- It must be as appealing as possible to malicious users so that they are more likely to attack it. The level of difficulty in attacking a system must be somewhere between being something too easy, which can be identified as clearly not real, and something too complex, which makes the attacker lose interest. This way, attackers will let us collect more information about their methodology.
- It must simulate the whole network, which implies doing so in each element forming the network to display a honeynet and to obtain as much information as possible.
Examples of Honeypots for industrial control systems
Are you convinced that a honeypot is a useful tool to improve your control systems' security? You do not need to start over: there are several options which enable a quick and easy display of the solution in a control system.
Some of them are the following:
- Conpot it is an industrial control system low-interaction honeypot which can be easily implemented, modified and expanded. It enables creation of basic elements so almost any system can be built thanks to a broad variety of common industrial protocols. It is currently integrated into the Honeynet Project.
- Gridpot is an open-source honeypot which simulates a realistic electric network SCADA. Gridpot combines the Conpot honeypot and the power distribution system simulator GridLAB-D. This combination gives this honeypot those advantages relating to the data acquisition by Conpot and a simulation environment with different concepts which make it more realistic thanks to GridLAB-D.
- GasPot is a honeypot designed to simulate a Guardian AST tank monitoring system by Veeder Root. These monitoring systems are commonly used in the oil industry to measure fuel level. GasPot has been developed to be as unpredictable as possible so that two bodies are not alike. It is an open-source tool which can be downloaded from its repository on github.
- iHoney is a research project created in 2017 by what was then the Ministry of Industry, Energy and Tourism of Spain together with the S2 Group. In this project, a waste water treatment plant was completely simulated, including every possible element which could be present in a real plant in order to obtain as much information as possible about real attacks which this kind of facilities can suffer.
Advantages and disadvantages
Each industrial control system is different, so it should be taken into account that implementing a honeypot simulating each system correctly is a difficult task, but it leads to numerous benefits:
- Distraction for the attackers, since they believe that they are attacking a real system.
- Collection of information about who wants to attack your industrial control system, and the methods and tools used to do so.
- Serves as a tool to test the security of the system. If the honeypot simulates accurately the current level of security of the system, it can be used in pentesting in order to analyse the security so that it does not affect the real industrial process.
- It can be used to frustrate the attackers and prevent them from attacking more systems.
However, the disadvantages resulting from the implementation of the honeypots should also be taken into account:
- The first contraindication is to know if we are sure about attracting attacks on our network, since the honeypot can be used as an access point if it is not properly set (it makes it easier for attackers to get into the system instead of hindering it).
- The second problem is that implementing a honeypot requires extra equipment, which leads to an additional cost, whether real or simulated software and hardware.
- The difficulty to have a realistic simulation of OT devices is also a disadvantage, since we must appear real if we want to receive an attack and trick the enemy.
- Finally, it would also be necessary to recruit additional employees to monitor the honeypot and the analysis of the collected information if we really want to collect information and use it to improve security.
Conclusions
Honeypots are a powerful tool for monitoring and defence purposes, as well as in the field of industrial control systems, as long as they have the proper security measures in place to prevent them from being used an access point for threats and the related advantages and disadvantages are considered. As shown in this article, several industrial honeypots are currently available, so what are you waiting for?









