IEC 62443: Evolution of the ISA 99

The publication of control system security standards has increased in recent years as indicated in the article “Control Systems Security Guides”. On this occasion, the analysis is focused on just one standard in order to see how it has been altered to reflect the sizeable changes that industrial control systems have undergone.
Development of the ISA99 standards series began at the beginning of the new century, striving to make a push towards industrial control system security, thus creating a series of documents that would help to increase protection of these systems during cyber-attacks. In order to create this standard, the International Society of Automation (ISA) organised different work groups that were each in charge of a different part of the standard. Finally, the documents proposed were:
- ANSI/ISA-99.01.01-2007 “Security for Industrial Automation and Control Systems: Concepts, Terminology and Models”. First document of the series. It strives to build a base that can be referenced throughout the rest of the series.
- ANSI/ISA-TR99.01.02-2007 “Security Technologies for Manufacturing and Control Systems”. Technical report published following the first document. It was created with the intention of being reviewed regularly to reflect any developments in the market. It contains various security tools with descriptions of how to implement and configure them inside industrial control systems.
- ANSI/ISA-99.02.01-2009 “Establishing an Industrial Automation and Control Systems Security Program”. This was the last document to be published in the ISA99 series. The document describes the elements which are necessary for implementing a cybersecurity management system and also provides a guide that includes the requirements for each element making up the system.
- ANSI/ISA-99.02.02 “Operating an industrial automation and control system security program”. This document made it into the developmental stage but no draft was ever published. The objective of the document was focused on operation of the security program following its design and implementation. The operation included features such as the definition of metrics for measuring program effectiveness.
- ANSI/ISA–99.03.xx “Technical security requirements for industrial automation and control systems”. Development on this document never commenced. This part of the standard included theory regarding definitions of industrial automation and control system characteristics that distinguish them from IT systems. From a security point-of-view, they defined the security requirements that are unique to these systems.
Two of the most important features regarding the measures included throughout the ISA 99 are called security zones y conduits:
- Security zone: A group of physical or logical assets that share common security requirements. A zone clearly delineates a unit by defining a physical or logical border which separates the internal components from the external ones.
- Conduit: A conduit is a communication path between two security zones. It provides security functions which allow two areas to safely communicate with each other. All communication between different zones must be carried out via a conduit.
This is important from a security point-of-view: when grouping together assets and communicating them through known paths, the majority of the time it is easier to apply security measures on the conducts rather than ensuring that each individual asset is safe.
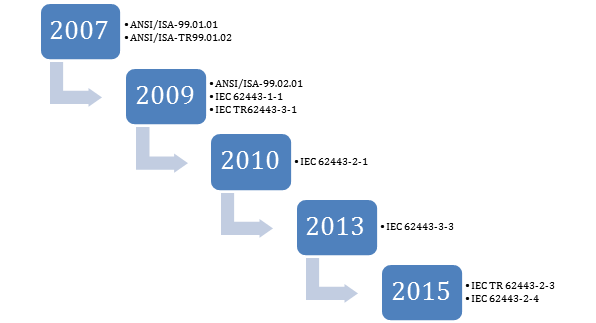
-ISA99 & IEC 62443 Publications-
In 2010, the numbering of ISA 99 changed to ANSI/ISA-62443 in order to be in line with the IEC document nomenclature. At the time, development on ISA99 is paralysed and new strategies for the IEC62443 are thought of, eventually resulting in 8 documents and 5 technical reports compared to the original 4 documents and 1 technical report.
The background and subject matter of the new IEC 62443 reflect all of the aspects proposed by the ISA99. In fact, the first documents to be published under the new nomenclature had previously been published by the ISA. However, when published under the new nomenclature, the documents had already underdone modifications and updates in accordance with a changing control system environment.
The IEC 62443 standard is formed by the following documents:
- IEC 62443-1-1 “Models and Concepts”: This document corresponds to the first document published within the ISA99, although it was reviewed so as to be in line with the rest of the documents that make up the current IEC 62443 series.
- IEC TR 62443-1-2 “Master Glossary of Terms and Abbreviations”: It contains a term glossary as well as the abbreviations that are used throughout the series. The list of concepts can be seen on the standard’s Wiki page, and users can even suggest modifications to the proposed definitions.
- IEC 62443-1-3 “System Security Compliance Metrics”: This document defines compliance metrics for security in industrial automation and control systems. It is currently being drafted and is open to comments.
- IEC TR 62443-1-4 “Security Life Cycle and Use Cases”: This document focuses on the life cycle and also gives use cases of typical applications within control systems. This document has been proposed for approval but has not yet been given final approval.
- IEC 62443-2-1 “Requirements for an IACS Security Management System”: This document contains the information corresponding to the second document published within the ISA99 (ANSI/ISA 99.02.01-2009). Currently the requirement contents are under review in order to ensure alignment with the ISO 27000.
- IEC TR62443-2-2 “Operating a Control Systems Security Program”: This document deals with efficient operation of cybersecurity programs in industrial control systems. This document is still undergoing development.
- IEC TR 62443-2-3 “Patch Management in the IACS Environment”: Practical guide to carrying out an update management program from the point-of-view of both the owner and the solution provider. It is still under development.
- IEC 62443-2-4 “Certification of IACS supplier security policies and practices”: This document focuses on certification for suppliers of industrial automation and control system security products. This document has been adapted from the requirements proposed by the WIB in their document “Process control domain - Security requirements for vendors”. This part of the series is under development.
- IEC TR62443-3-1 “Security Technologies for IACS”: It is an updated version of the “ANSI/ISA-TR99.01.02-2007” from ISA 99. It offers a description of existing industrial system and network protection technologies, presenting both their advantages and limitations. It is currently under review.
- IEC 62443-3-2 “Security Risk Assessment and System Design”: This document describes the concepts of ’security zone’ and ’conduit’ which were introduced in the ISA99. Furthermore, it specifies how to perform segmentation following these principals. Only a theoretical segmentation is presented here, whereas the real segmentation is dealt with in the document IEC 62443-4-2.
- IEC 62443-3-3 “System Security Requirements and Security Levels”: This document describes the technical requisites of the system in order to define the security level of the asset being analysed. In order to do this, the document establishes a relationship with the seven fundamental requisites presented in the IEC 62443-1-1. At the same time, the document stresses that performance and availability should not be affected when attempting to fulfil these requirements.
- IEC 62443-4-1 “Product Development Requirements”: This document defines the development process that should be used to create new devices for control systems, although it can also be applied to already existing devices. To do this, the document references development processes both for software and hardware.
- IEC 62443-4-2 “Technical Security Requirements for IACS Components”: This part of the IEC 62443 series corresponds to the ANSI/ISA-99.03.03 document which was never published. This document groups together the technical requisites for improving the security of components on an individual level within an industrial network. The document also deals with network segmentation to restrict data flow within the network and between networks.
One of the main security objectives of the IEC 62443 is defence in-depth, delving into the concepts proposed by the ISA99 as well as extending security to other settings from manufacturers to operators.
As can be seen in the summary of the different parts that form each standard, the majority are still under development or under review, therefore meaning that now we must wait for the changes in control systems to be reflected. Taking into consideration and bringing together all of the security measures could make IEC 62443 the most relevant security standard for this sector.









