Incontroller, the intelligent menace

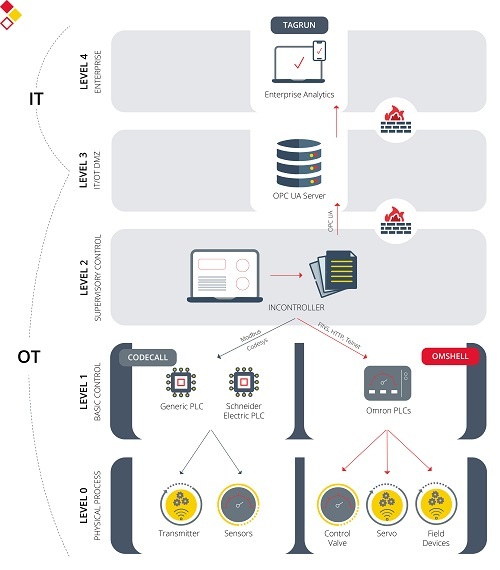
Incontroller (also known as Pipedream) is considered as a set of tools focused on attacking ICS environments which is enabled to carry out network scans in order to search for specific devices, initiate and establish communications with PLC devices, and interact with these devices in order to tamper with or modify their expected function.
Incontroller is similar or comparable to other malware that has impacted the industrial sector in the past, such as Industroyer, which caused energy cuts in Ukraine; Stuxnet, which had the same effect in a nuclear plant, or Triton, which was used to deactivate industrial security systems
This and other malware is further described in our articles ‘Threats to Industrial Control Systems’ or ‘Emerging Threats to Industrial Control Systems’, which include many incidents caused to industrial sectors by malware or targeted attacks.
Tools used
The tool set used by this malware, acting in a coordinated manner, could cause disruption, sabotage or even the physical destruction of industrial devices. This, together with the fact that it impacts systems that are very prevalent in the industrial sector, makes an Incontroller attack an important concern.
Its main three characteristic components are:
- Tagrun
- Its main capabilities are scanning and listing the OPC UA servers used for recognizing an industrial environment.
- It acts as a central server that gradually collects information from the industrial environment, which provides any attackers with accurate and detailed information that allows them to prepare a more sophisticated attack.
- It is also capable of reading and modifying the values in OPC UA.
- Another capability is the identification and adaptation of the tool based on the operative system in which it is installed.
- Codecall
- Capacity to communicate with devices using the industrial protocol Modbius, which is widely used by many manufacturers in their different devices.
- Such characteristic also allows for an interaction with devices using Modbus, which allows to read and write on the devices’ logs.
- It has a specific module to scan and attack Schneider Electric PLC Modicon M251 devices, executing commands through Codesys.
- Omshell
- Omshell is specifically designed to obtain access to Omron PLC devices (including NJ/NX, NX1P2, R88D-1SN10F-ECT and NJ501 series devices) by means of a console.
- The tool uses HTTP as main protocol, although it also has the capacity to carry out scans through UDP and to use the Omron FINS proprietary protocol.
- Omshell is also characterized for being a modular tool, which can use specific modules depending on the environment and devices in order to carry out more precise attacks.
In the following drawing, the architecture of the Incontroller tool is shown, together with their different modules and its main characteristics.
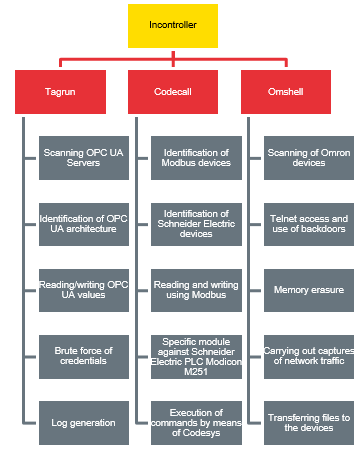
- Incontroller architecture, modules and characteristics. -
Additionally, Incontroller also has two tools oriented to the Windows environment, with the main purpose of being able to exploit those environments during an attack. The two main tools are shown below:
- The tool called ICECORE enables the creation of a backdoor with different recognition, command and control functions.
- The other tool specifically exploits the vulnerability CVE-2020-15368, which impacts the AsrDrv103.sys library in the ASRock RGB Driver base plates.
- Incontroller tools. Source: Mandiant . -
Use cases
With respect to the potential attacks that could happen in an industrial environment, since they are a set of independent tools, they could be used in a modular manner depending on the scenario of the attackers, who could adapt the tools they use to the targets or goals of their attack.
Some potential scenarios are:
- Scenario 1: reprogramming of industrial devices
- Sabotage by means of reprogramming of devices (for example, PLC devices) could cause alterations in the normal functioning of the process.
- Pursuant to the targets and intentions of the attacker, the effects could be diverse: from major modifications in the process to minimum modifications that would impair the company production in the long term, silently and discreetly creating economic losses over time.
- Scenario 2: destroying or disabling PLC devices
- The target would be to carry out attacks based on code modification or by means of denial of service attacks, using tools as the aforementioned Omshell or Codecall.
- Destructing or disabling the devices would cause the relevant organization, it would cause economic damage for the organization, as well as the losses associated to the downtimes required to replace damaged devices by new ones.
- Scenario 3: disabling Safety devices in order to cause physical destruction
- Lastly, another of the potential scenarios would be directly attacking the Safety devices of the industrial environment, which are in charge of protecting, at a physical level, both the people and the components in the plant.
- There are different Omron Safety devices which could be affected by Omshell targeted attacks to the point of being impaired for use or even disabled.
- Attacks against Safety devices could also provoke the shut-down of a part of the industrial process, since some systems and devices do not operate if Safety devices are not operational.
- Besides, it could cause physical damage in the industrial environment, including physical injuries to the plant employees, by disabling protection functions as safety barriers, movement or presence detectors, etc.
Advice and guidelines to prevent attacks
One of the challenges of Incontroller is that, since it is a tool exclusively designed against industrial environments and, specifically, against certain devices and protocols, early detection and intervention can be complicated.
Next, some of the possible recommendations or guidelines to be followed for an early detection or prevention of such attacks are listed:
- Use of tools to detect anomalies, IDS and Yara rules for the identification of abnormal communications within the network and enabling fast intervention.
- Updating of all affected and previously mentioned devices according to the recommendations of each manufacturer; this applies to Schneider Electric, Omron and Windows devices.
- Implementing an appropriate network segmentation, both implementing a separation at IT/OT level and segmenting and protecting the different networks in the OT environment, which would hinder a potential attacker from jumping across devices and networks.
- Node reinforcing in industrial devices, allowing only safe communications if possible and restricting communications by means of firewalls.
- Centralized management and log analysis for the detection of evidence in industrial devices.
Conclusions
The number of malware-related attacks and reports or attacks against industrial environment increases each day, exploiting the fact that such industrial environments have inherited many IT vulnerabilities, to which they add those from the OT devices. All this involves that the techniques used are more sophisticated.
Cybersecurity is a somewhat neglected area and an aspect that companies need to consider as an area of continuous improvement, in order to achieve a more mature level of cybersecurity that will be make the system less vulnerable to attacks and enables early detection and intervention in this type of adverse situations.









