Industrial honeypot implementation guide
How can we determine the modus operandi, methods and tools that an attacker will use in order to achieve his goals? This is one of the main problems we encounter when it comes to improving our cybersecurity, given that it is very difficult to fight something we are unfamiliar with. However, as difficult as it sounds, there are always tools that can help us if we use them correctly.
One of them is the honeypot, a system of traps or decoys that, when properly configured in our network and once it has been the target of an attacker, allow us to detect them, obtain information on them and study their behaviour in order to be able to implement sufficient protective measures, thus favouring the improvement of our systems’ security.
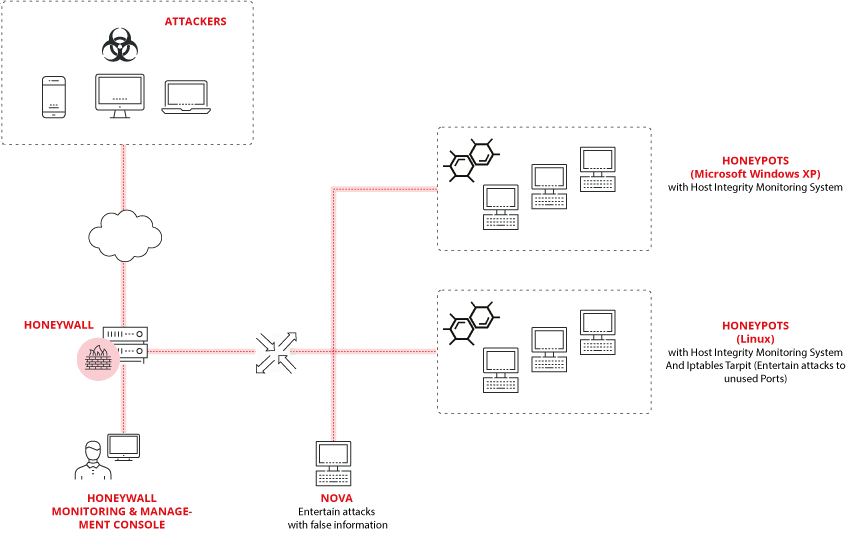
These honeypots are typically jointly integrated within one network, called a honeynet. This makes it possible to recreate a whole scenario as realistically as possible, including production systems, servers, services, etc. This will favour the chances of deceiving attackers and being successful in obtaining useful information. We also cannot forget honeywalls, machines that are exclusively made to act as firewalls, and are vital for monitoring and filtering all generated traffic.
Throughout this guide, we seek to provide basic knowledge that serves as a starting point in order to raise awareness about this defence system, the different options, available tools and projects, offering detailed implementation instructions in order to easily deploy it in an industrial environment from scratch, with illustrations and examples.
The complete guide may be downloaded at the following link:
- English: Industrial honeypot implementation guide.
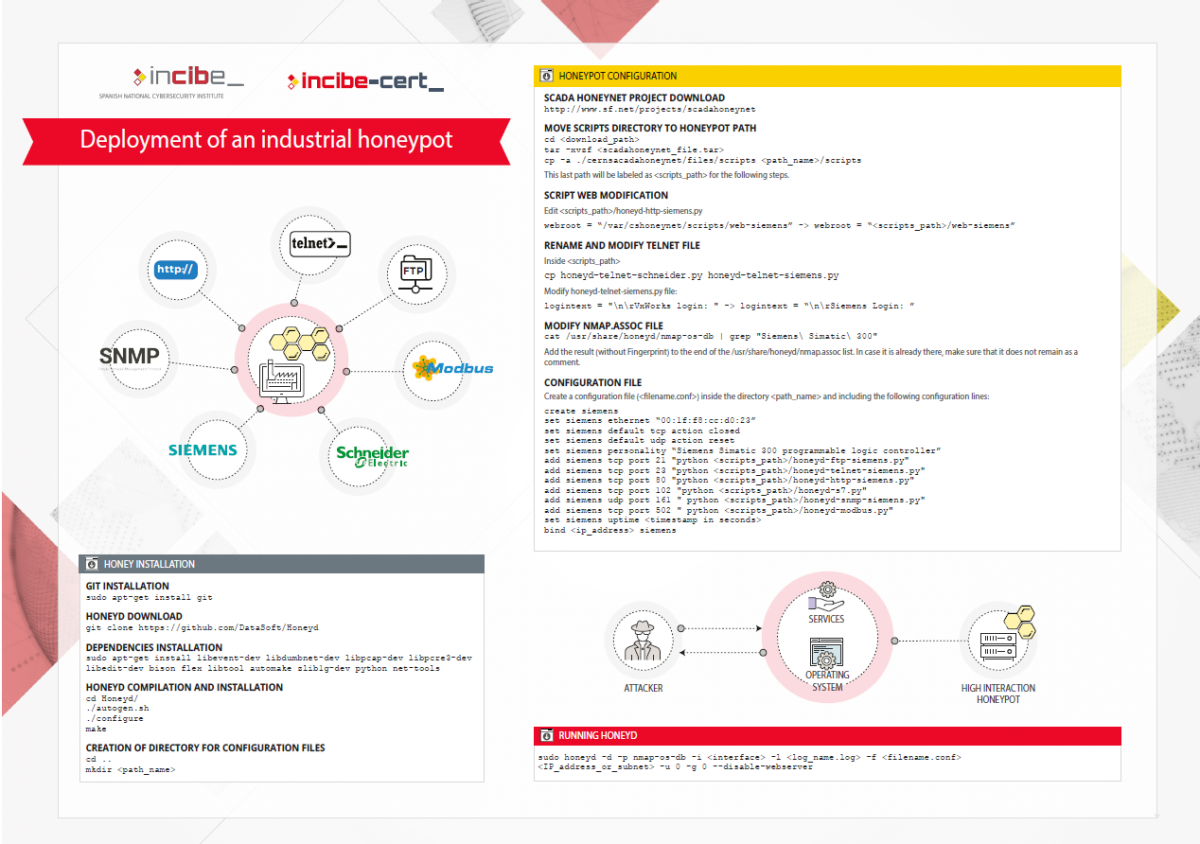
The following document explains the steps required to deploy the honeypot from scratch:
- English: cheatsheet for honeypot deployment.