Industrial security 2019 in figures

INCIBE-CERT continued working throughout 2019 on early warning services and cybersecurity warnings. Specifically, in the ICS warnings section, different warnings related to Industrial Control Systems and the world of Internet of Things in industrial environments (IIoT) have been published. This specific service was created four years ago with the aim of providing all companies in the industrial sector with a means to look up information about the vulnerabilities that their devices may have.
This information, in addition to being available via the website and via RSS, can be accessed through a newsletter, so users can report all vulnerabilities affecting devices, software and other elements of industrial manufacturers.
In addition to the description of the different vulnerabilities, within each warning there is a section where the solution provided by the device manufacturer is specified. It may be the case that there is no specific solution for this, and as a mitigation measure, information is provided by following good practice documents both regarding device configuration, network segmentation, etc.
Besides this daily publication of the early warning system and of Industrial Control System warnings, INCIBE, through INCIBE-CERT, has continued with the dissemination of cybersecurity about this type of system, publishing specific content on the blog and also through different guides and studies.
Throughout 2019, within the warnings service provided, the different vulnerabilities that have affected the industrial sector have been reported.
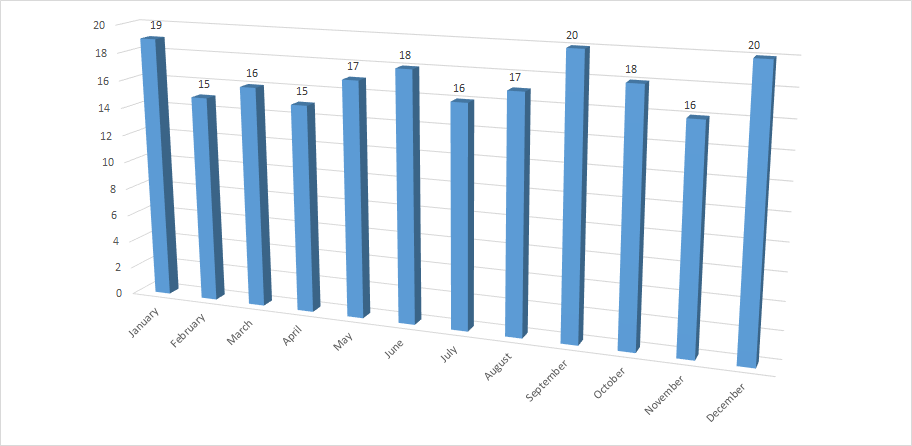
-Number of warnings published per month during 2019-
Taking a look at the work done throughout 2019, we can see that 207 warnings related to the industrial sector have been published, a minimal reduction compared to the 228 in 2018, which range from IIoT devices to others, more traditional ones in the industrial world. It is important to mention that sometimes the same warning has several vulnerabilities, but in this graph only the warnings are counted. This may be one of the reasons why the number of warnings published in 2019 is slightly reduced compared to those published in 2018. On the other hand, warnings related to applications (desktop, web, mobile applications, etc.), communication elements in this environment and other topics have also been published.
As can be seen in the graph, there is a continuous flow when publishing vulnerabilities. This fact may occur due to the continuous reports made by researchers regarding industrial cybersecurity and to increased awareness in this area among industrial companies.
Classification by sectors
Regarding the sectors involved, one may observe that there have been warnings that have affected almost all the strategic sectors defined in the Critical Infrastructure Protection Law (Law 8/2011), as set in the following chart.
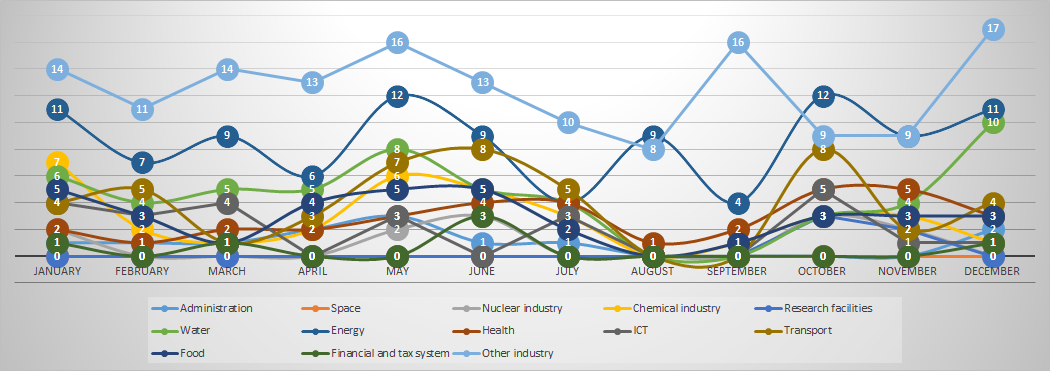
-Development of warnings by sector. The energy sector, as in previous years, is the most-affected (excluding “other industry”, which is not a sector in itself) -
As in previous years, most of the warnings are related to multipurpose devices that are used in different sectors. This means that a single warning, in addition to containing different vulnerabilities, can affect different sectors. Thus, the products (devices and applications) corresponding to the sector called “other industry” have been those most affected by the warnings in practically all the months of the year.
As in previous years, it is important to mention that being the sectors that bring together the most warnings does not mean that they are the most insecure. This fact is due, among other factors, to the number of devices, manufacturers and processes that are used on a daily basis in each sector. For example, the energy sector is the sector most affected by the warnings, since practically all the processes involved in this sector are used constantly, and in many cases, other sectors rely on the energy sector to provide their service.
Nature of the warnings
The cataloguing of the vulnerabilities analysed in each warning is limited to the different types of vulnerabilities described in the CWE (Common Weakness Enumeration) list. This list reflects virtually all vulnerabilities that may affect different assets, including a brief description of each.
The most prominent vulnerabilities that affect devices related to the industrial world in 2019 are:
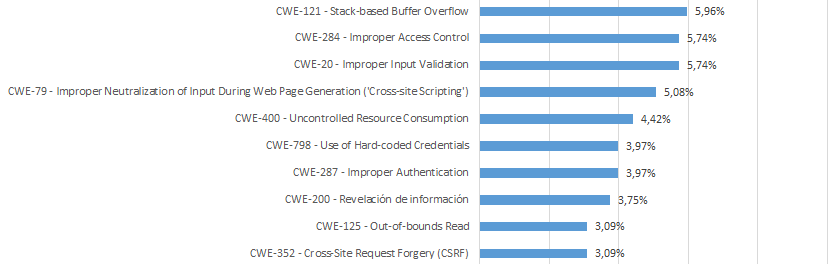
-Nature of vulnerabilities 2019 (top 10). Please note that a warning may be related to several vulnerabilities-
Among the most-reported types of vulnerabilities are buffer overflow, incorrect parameter management, incorrect access control or Cross-Site Scripting (XSS). These vulnerabilities warn of the need in the market to follow good practice guidelines when developing industrial software to avoid malicious access to the buffer or incorrect validation of the input parameters. In addition, many of these vulnerabilities are inherited from the IT world, so it is sometimes possible to review examples of development to avoid making the same mistakes.
As has happened in previous years, it seems that sensitive information and remote accesses are again in this top 10. In addition to availability, as is logical in the industrial world, information is gaining significant weight due to the increasing use of some IIoT devices that use cloud technology.
Another point to consider after reviewing the graph on the nature of vulnerabilities in 2019 is the exploitation of vulnerabilities related to web services. Currently, many of the industrial devices that are deployed in industrial networks already have a web server. Through the use of a more user-friendly web interface, these web servers make it possible to perform actions that may be important for the proper development of the process in which the device is involved.
Manufacturers
The list of manufacturers most related to the warnings changes slightly from the previous year. The major leaders in Industrial Control Systems products continue to be the most-exposed and, therefore, those about which most warnings are published.
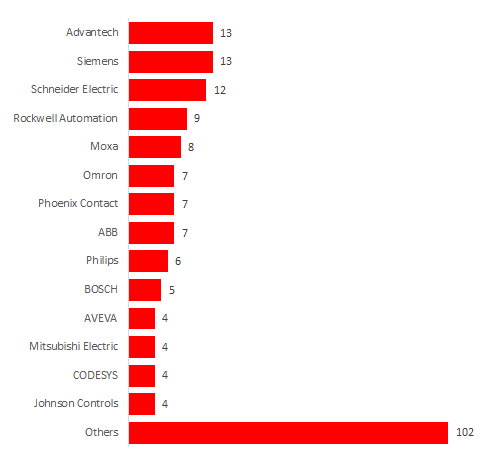
-Number of warnings published by manufacturer-
With regard to the first places, Advantech has entered at second with 13 warnings compared to the 5 reported in 2018. On the other hand, the other manufacturers that continue to publish more warnings have not changed compared to previous years, with Siemens and Schneider Electric remaining in the top 3.
A large number of warnings per manufacturer does not mean that the manufacturer is the most vulnerable, but that they might have a team of researchers hired by the company to conduct research or, as they are the most widespread, many researchers have access to one device of the multiple families they have.
Classification by criticality
The classification of the 2019 warnings according to their criticality is very similar to that presented in the 2018 summary; a large proportion of them are of high or serious criticality. This reminds us again that the protection of control systems must be strengthened, since the vulnerabilities reported in them can entail major disruption for the company and serious consequences in the production process.
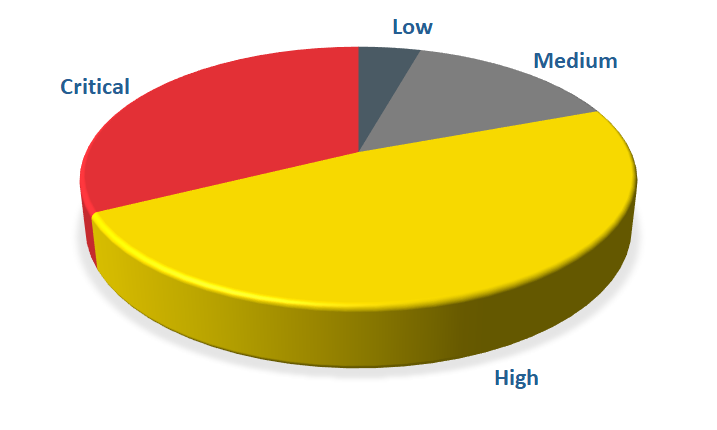
-Classification of warnings-
Conclusion
2020 foretells, among other challenges, the following:
- The management of IIoT devices with platforms that mostly use cloud technology.
- An improvement in industrial communications, either through new specifications or through the use of devices added to the network, and which is beginning to be widely exchanged under encrypted channels.
- The different emerging threats are increasingly complex to detect and analyse. The organisation of response teams in industrial environments or analysts that support these incidents will begin to become very important.
With respect to the warnings, intuition indicates that everything should follow the same path with a growth in the detected vulnerabilities, criticalities that will not vary much and large industrial manufacturers with which the largest number of published warnings will be associated.









