Industrial security 2022 in numbers

INCIBE-CERT has continued to work throughout 2022 on early warning services and cybersecurity alerts. Specifically, in the ICS alerts, where different warnings related to Industrial Control Systems and the world of the Industrial Internet of Things (IIoT) have been published. This specific service was created seven years ago with the aim of providing all companies in the industrial sector with a means of consulting information on the most recent vulnerabilities that their devices may have, in order to be able to apply the appropriate mitigation measures, provided by the manufacturers of the affected products or from documentation on good practices in the configuration of devices, network segmentation, etc., as quickly as possible.
This information, in addition to being available via the web and social media, can also be consulted through a bulletin, with which users can be informed of all vulnerabilities affecting devices, software and other items from industrial manufacturers.
In addition to this daily publication of the early warning and alert system for Industrial Control Systems, INCIBE, through INCIBE-CERT, has continued with the dissemination of cybersecurity on this type of systems, publishing specific content on the and also through different guides and studies.
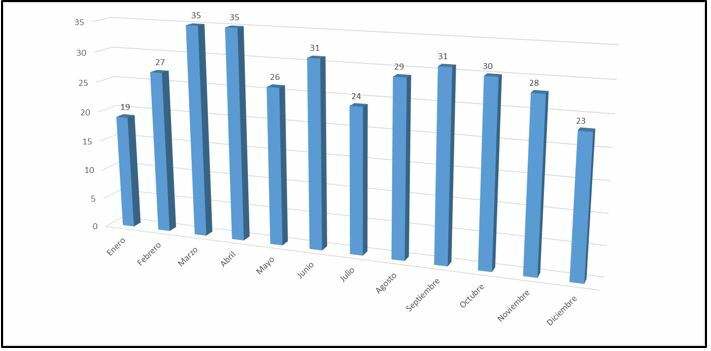
- Numbers of notices published per month during 2022. -
A look at the work carried out throughout 2022 shows the publication of 338 warnings related to the industrial sector, ranging from IoT devices to more traditional industrial devices, as well as warnings related to applications (desktop, web, mobile applications, etc.), communication elements in this environment and other topics. It is important to note that the same advisory can have several vulnerabilities, as we will see below, but only the advisories are counted in this graph.
The constant rate at which vulnerabilities are published could be due to the continuous reporting by industrial cybersecurity researchers and the increased awareness in this area on the part of industrial companies.
Classification by sector
With regard to the sectors involved, it can be observed that there have been warnings that have affected almost all the strategic sectors defined in the Critical Infrastructure Protection Act (Act 8/2011), as shown in the following graph.
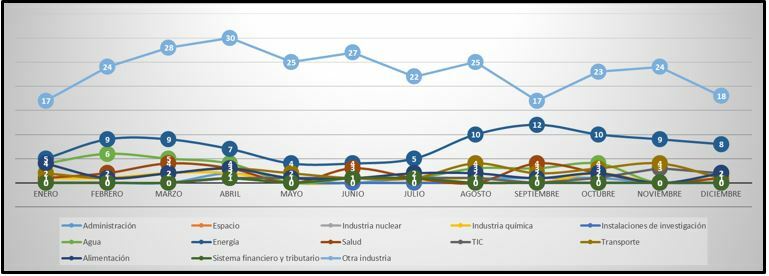
- Evolution of notices by sector. The energy sector, as in previous years, is the most affected (excluding "other industry", which is not a sector per se). -
As in previous years, most of the published advisories relate to multi-purpose devices. This means that a single advisory, as well as containing different vulnerabilities, can affect different sectors, with the so-called "other industry" sector being the most numerous.
Similarly, it is important to note that the sectors with the most warnings are not necessarily the most insecure, as there are other factors, such as the number of devices, manufacturers and processes that are used daily in each sector. For example, the energy sector is the sector most affected by warnings, as practically all the processes involved in this sector are used constantly, and on many occasions, other sectors rely on the energy sector to provide service.
Nature of alerts
The cataloguing of the vulnerabilities analysed in each alert follows the different types of vulnerabilities described in the CWE (Common Weakness Enumeration) list. This list reflects practically all the vulnerabilities that can affect different assets, including a brief description of each one.
The most prominent vulnerabilities affecting devices related to the industrial world in 2022 are:
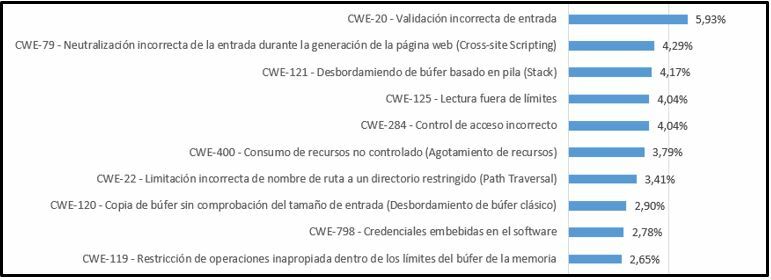
- Nature of vulnerabilities 2022 (top 10). Note that a warning can be related to several vulnerabilities. -
The most common vulnerabilities include incorrect validation of input parameters, Cross-Site Scripting (XSS) and stack-based buffer overflows, which highlights the need to follow good practices during industrial software development. In addition, many of these vulnerabilities have been passed on from the IT world, so it is possible to follow development examples to avoid making the same mistakes.
In addition, as in previous years, vulnerabilities related to out-of-limit reads and improper access control are still very much present, which can allow an attacker to remotely gain confidential information or control of the device.
Another aspect to consider when examining the graph on the nature of vulnerabilities in 2022 is the exploitation of vulnerabilities related to web services. Today, many industrial devices that are integrated in industrial networks have a web server through which they provide a more intuitive interface for the operator and allow performing actions that may be important for the proper functioning of the process in which the device is involved.
Manufacturers
The list of the manufacturers most frequently advertised has changed slightly from previous years. The major leaders in Industrial Control Systems products continue to be the most exposed and, therefore, the ones about which the most advertisements are published.
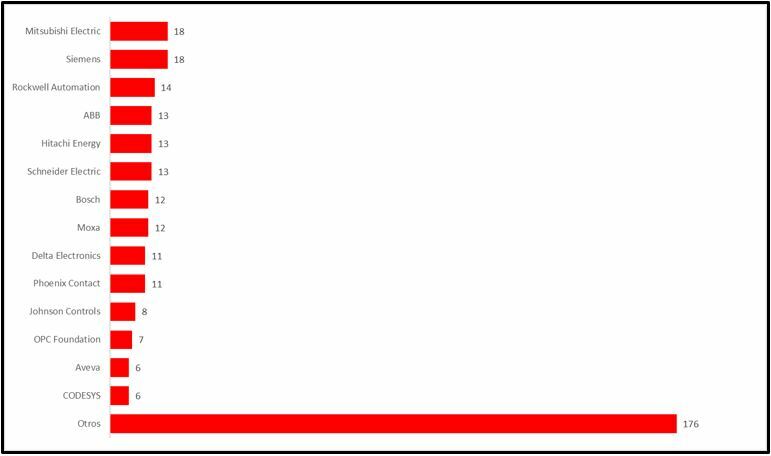
- Number of warnings published by manufacturer. -
As far as the top positions are concerned, Mitsubishi Electric and Siemens share the first position with 18 warnings each, with Rockwell Automation in third position with 14, closely followed by several manufacturers, with a total of 10 manufacturers with more than ten warnings. In addition, many of the INCIBE-CERT alerts group together multiple alerts issued by individual manufacturers, so these figures include more vulnerabilities than might at first appear to be the case.
It should also be noted that many alerts on a manufacturer does not mean that the manufacturer is more vulnerable, but that they may invest more effort in security research or that many independent researchers have access to a device from their multiple families, as they are the most widespread.
Criticality rating
The classification of the 2022 alerts, according to their criticality, is very similar to that presented in previous years' summaries, with the difference that INCIBE-CERT has focused exclusively on medium, high and criticality alerts, mainly due to the fact that high criticality alerts are more damaging for organisations. This reminds us once again that it is necessary to reinforce the protection of control systems, as the vulnerabilities reported in them can be a major disruption for the company and have serious consequences for the production process.
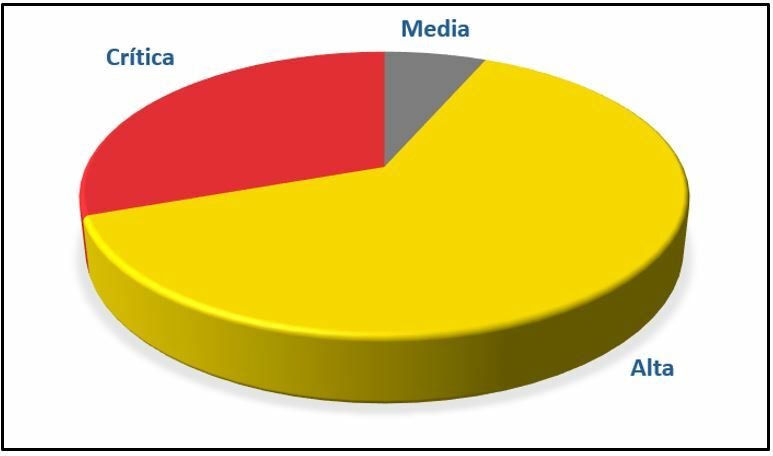
- Classification of warnings. -
INCIBE as CNA
A new feature this year is INCIBE's role as CNA in the assignment and publication of CVE identifiers, where in 2022, a total of 23 CVEs have been coordinated and published, from a total of 11 manufacturers.
In turn, the reported vulnerabilities are of 15 different types or CWEs, the two most common of which are as follows:
- CWE-79: inappropriate input neutralisation during web page generation (Cross-Site Scripting).
- CWE-89: incorrect neutralisation of special elements used in a SQL command (SQL injection).
With regard to coordinated CVEs, together with the CNAs adhered to INCIBE Root (ZGR, Artica PFMS, Alias Robotics and KrakenD), a total of 20 CVEs were published during the year between the 4 CNAs.
Conclusion
In summary, 2022 has continued the trend of previous years as the number of vulnerabilities detected and advisories issued has grown considerably. Likewise, the criticality of the vulnerabilities found has not changed much and the large industrial manufacturers continue to lead the way in terms of the number of warnings issued.
In any case, 2022 has left us with certain aspects to consider that could be relevant in the future, such as the fact that, although large industrial manufacturers lead in the publication of warnings, smaller manufacturers are beginning to follow in their footsteps, with more and more of these types of publications.
The future is uncertain and it is difficult to know what 2023 will bring but, in next week's article, we will look at 10 industrial security predictions that could help you to get an idea of how industrial security will develop in the coming year.









