Introduction to Embedded Systems

The number of embedded systems, also known as integrated systems, in the world is approximately 10,000 million, a figure that keeps increasing. Embedded systems are not only used for industrial purposes but they are present in any aspect of our lives, since a large amount of daily equipment are provided with these systems, such as cars, lifts, toys, etc.
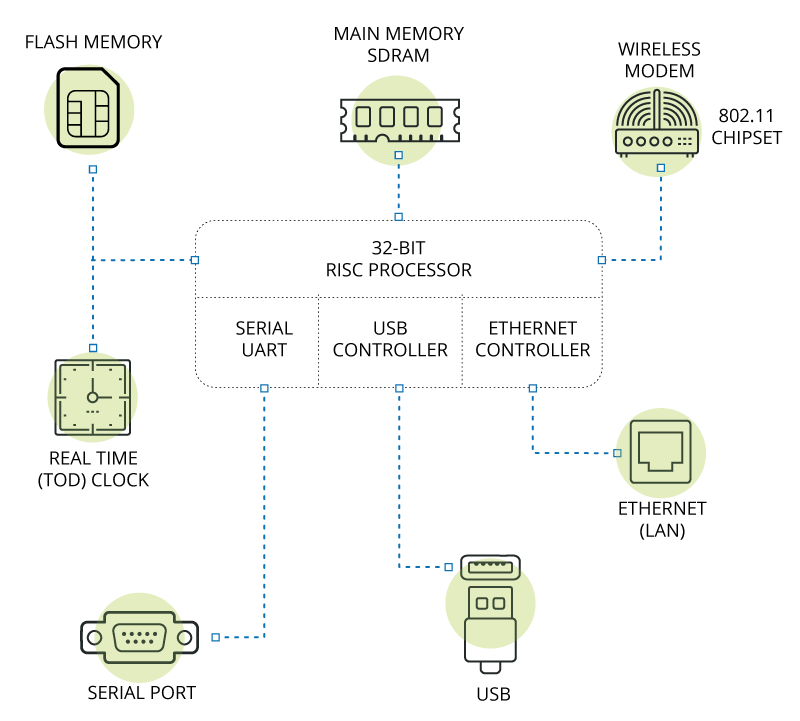
-Description of an embedded system (physical level)-
Embedded systems are thought to be closed systems without interfaces with the user or with other devices. However, they are fully functional systems the purpose of which is to execute control tasks. It is also widely believed that all embedded systems are real-time systems by they do need such characteristic by default. Basically, an embedded system has two main features:
- Reliability: They must be able to operate continuously without supervision.
- Customisation: They must allow the modification of the system based on the needs of the process.
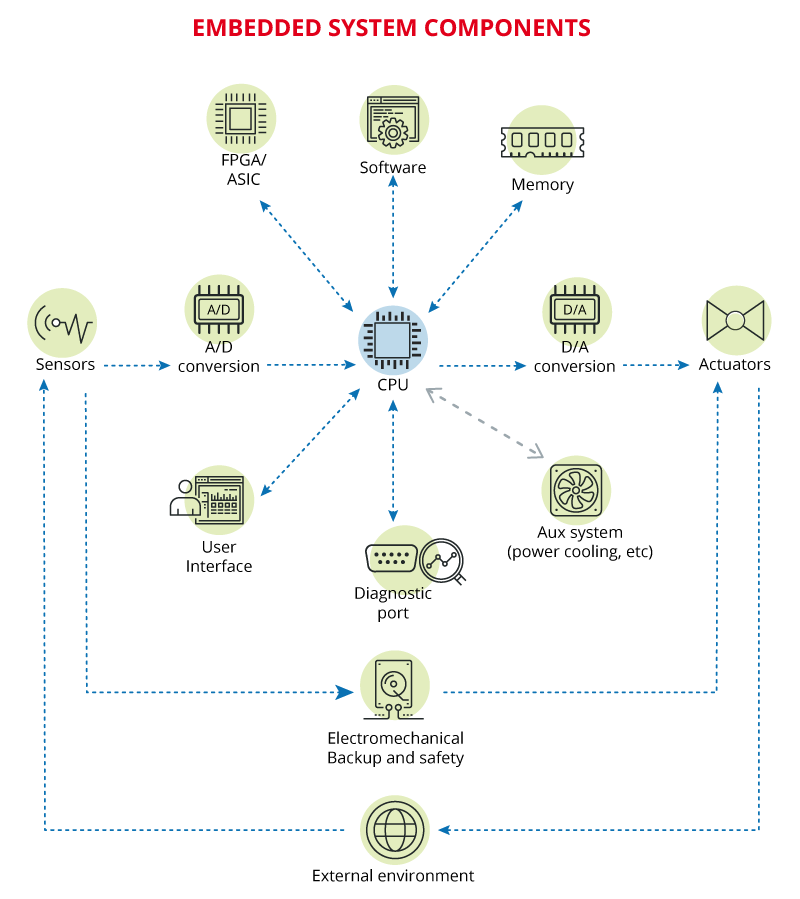
-Components of an embedded system (logic level)-
The main problem of embedded systems is that, in general terms, they are designed without taking into account security, offering limitless connectivity. Besides, the protection measures the market offers are very limited.
Embedded operating systems
The first embedded operating systems were exclusively based in the processor (micro-controller), without an operating system and with instructions directly written on it. When the processor was obsolete, so was the device and thus, the programming.
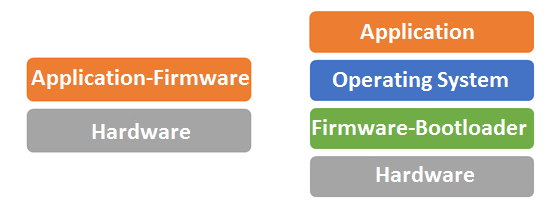
-Traditional embedded system architecture (left) and another one based on an operating system (right)-
In the 80s, the first embedded systems with operating systems were created mainly to cover communication needs, making hardware applications independent and allowing for the reuse of libraries. The characteristics of modern operating systems include (even though not all embedded systems use them):
- Graphical user interface
- Implementation of protocol stacks
- Support for external storage such as USB.
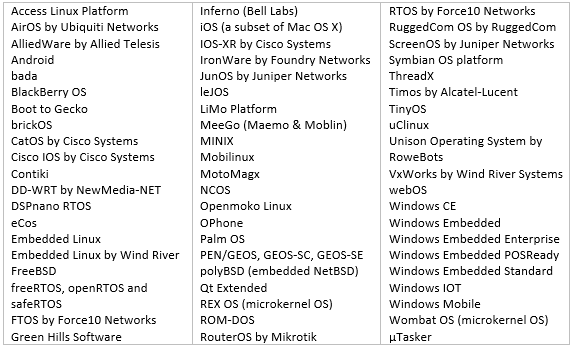
-List of operating systems of embedded systems-
General purpose operating systems have also accessed embedded systems and with them, the weaknesses they involve. Therefore, the weaknesses of external libraries or own libraries of Linux and Windows may cause problems for the devices they control. Can you picture an embedded system blocked by a blue window of Windows? It may happen but it is more common that the display is independent from control so, even though information may not be shown on the screen, the process is still being executed properly.
Main security problems
As in most industrial equipment, embedded systems are designed to be secure at a physical level, having rebooting measures in the event of failure (watchdog), duplicated hardware parts, fail-proof programming, etc. But, what about cybersecurity?

-Failure of the embedded system on an information screen-
Some of the weaknesses of the embedded systems affect cybersecurity at a logic level are the following:
- Secret sharing: Certain sensitive information, such as passwords, are often shared between the applications of the manufacturer so that they can communicate more easily to one another. This shared information may allow a potential attacker access with a same username to different applications.
- Private certificates: many services require self-signed certificates which are not backed-up by trusted entities, lowering the security level of services. An attacker may use these certificates by using other ones which have been generated specifically and allowing them to perform actions in the device or deceive the user.
- Embedded passwords and back doors: These two characteristics are very common. The manufacturer includes embedded passwords preventing their modification over time and making all clients use the same ones. Back doors allow manufacturers to access embedded devices without taking into account any possible changes by the client. Attackers may take advantage of these weaknesses to retrieve information from the device or even to control it.
- Free code failures: Most parts of the code of embedded systems are based on routines or reused processed, many of which are based on free codes. This code is not usually checked and it may cause failures with other parts of the system or due to programming weaknesses. Attackers may use these failures as access points for more advanced attacks.
- Weak or non-existent cryptography: Encryption methods are usually scarce. The use of encrypted communications is only used in the more advanced versions, whereas the simplest versions work with Telnet and HTTP communications, with the corresponding weaknesses. This limitation may allow potential attackers to capture and interpret the traffic exchanged between both devices and they may even retrieve sensitive information from the device.
- Weak or non-existent authentication: Authentication of devices is usually based on a PIN code (such us mobile phones) or has no access control at all. Potential attackers may use brute force methods without much difficulty to gain access to devices or applications.
- Exploitation of the server software (HMI, management, web): Some of the services offered are based on the client-server mode where the embedded device acts as server. These services may be vulnerable to XSS, SQL injection attacks, etc. If attackers can make use of these weaknesses, service to the device may be rejected and remote codes may not be executed, with the corresponding problems for the operator.
- Input/output communications: Outward communication ports are the weakest point of the embedded systems. In general terms, their use may not be disabled so all ports available are always available even though they are not used at all. Ports which are not being used due to the needs of the device may be used by potential attackers as access points to the device to gain control over it.
- Ladder logic exploitation: The programming of the control loop is not properly protected most of the times so it may be modified to perform actions other than the ones developed by the manufacturer. Potential attackers may obtain and modify the programming of the device, forcing it to perform different actions and threatening the whole process, even human lives and the environment.
- DoS and DDoS: They are the most common consequence before any attack. These devices are not usually provided with a network frame control or equivalent system, so a repeated information request may saturate communication channels. However, communications are not the only aspect that may cause disruptions. There are other design failures within applications, such as the lack of normalisation of input user data, that may cause rejections in the service.
Potential physical options must be added to all these logic weaknesses, since the opening of the device for its analysis and subsequent attacks are always present. These embedded systems are not usually provided with opening detection mechanisms nor test port removal used in the design phase of the hardware.
There are many reasons for applying security measures to embedded systems. Manufacturers are responsible for the application of such measures, particularly regarding physical aspects. However, users can also improve security. This chapter is an introduction to a series of articles that will inform on the hardening measures for embedded systems with general purpose operating systems such as Linux or Windows.









