Is it secure to charge your vehicle in publics places?

Due to the current climate change issues, the automotive industry is seeing a shift in the production trend from combustion vehicles to electric vehicles. One of the biggest challenges for electric vehicles is how to charge them, as the needs of drivers require them to be charged quickly, easily and efficiently. Charging stations are currently being used for this purpose.
Charging station architecture and communications
First of all, in order to make it easier to understand the possible cyber-attacks and risks that can be caused, it is advisable to know the architecture and communications of the charging stations. The following images show a visual and schematic example of the network architecture and communications. If you want to learn more about this field, it is advisable to read the following article 'Safety recommendations for electric vehicle charging stations'.
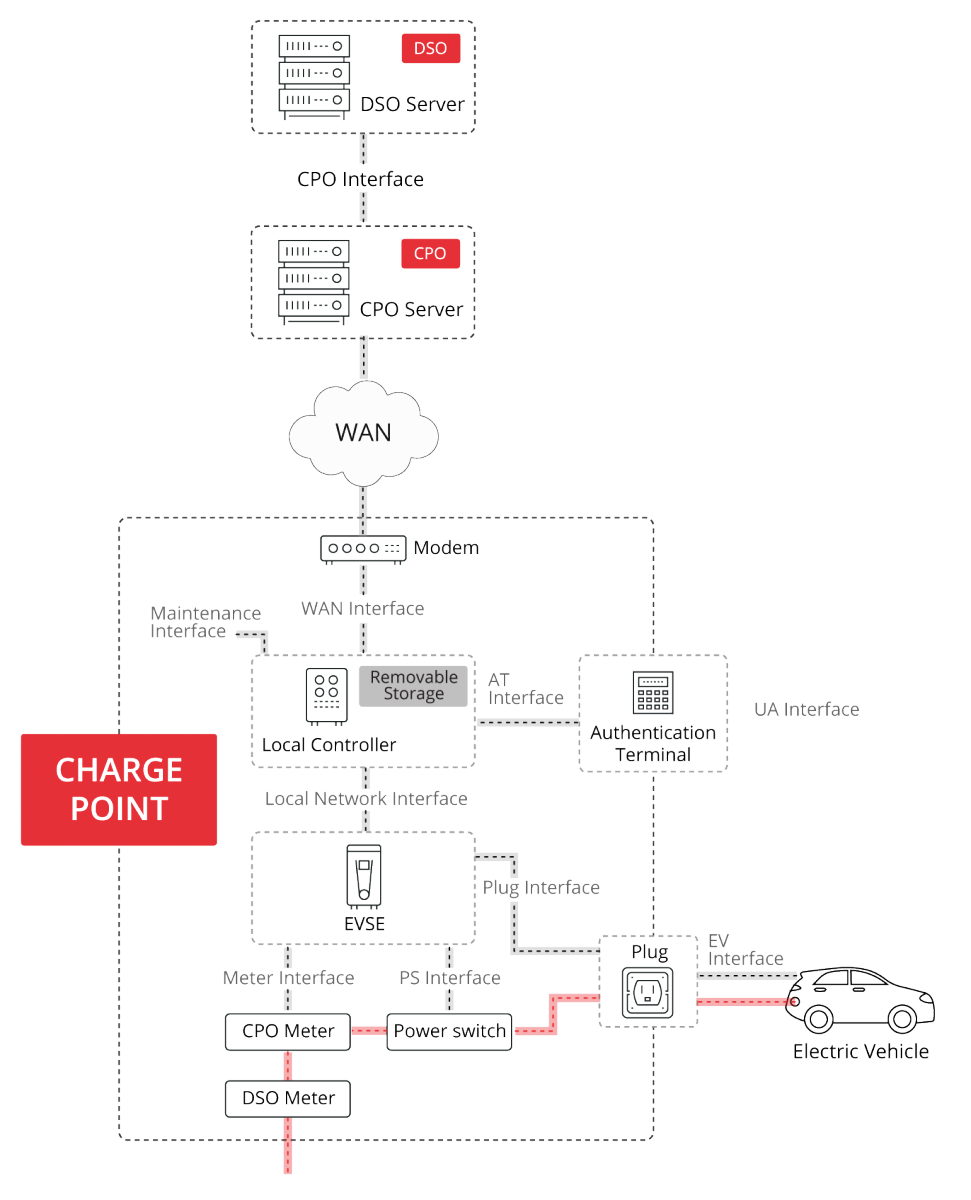
- Architecture of a charging station. Source: European Network for Cyber Security. -
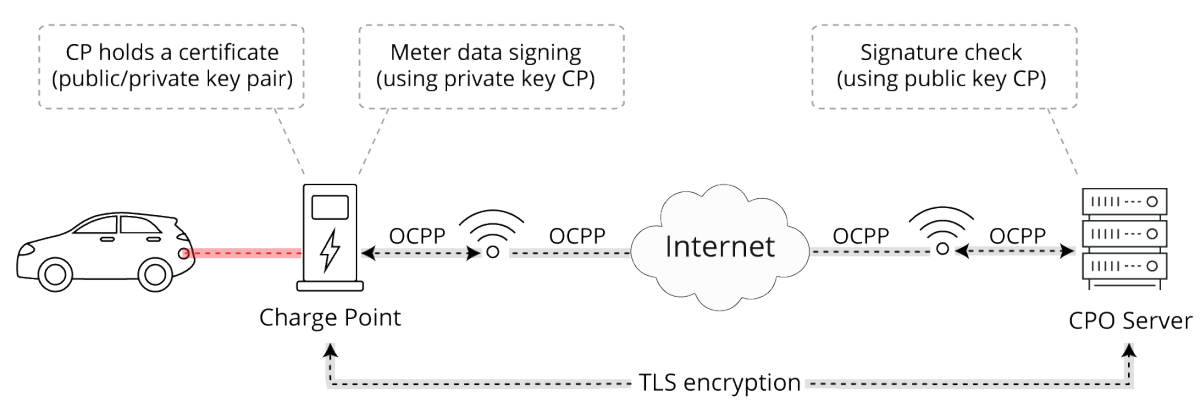
- Communication scheme using certificates and digital signatures. Source: ElaadNL. -
Types of cyber-attacks that the recharching station may be subjected
After some background on the peculiarities of charging stations, we will discuss the different types of cyber-attacks that can be carried out and the problems they can cause. Some examples of possible cyber-attacks will then be explained:
- One of the major problems is the existence of security vulnerabilities in the devices that make up the station, since, due to their location, in most cases, it is only possible to update them by physically going to the place where the station is located. The most common vulnerabilities found in this case are the lack of security in authentication and XSS (Cross-site scripting), which could be used to obtain sensitive information, compromise the browser being used or even hijack user sessions.
- Sometimes charging stations have USB ports, which could lead to various attacks such as inserting a specially designed USB flash drive, which can send a very high voltage discharge destroying the charging station device or even copying the station’s configuration data and registers.
- Another problem is that these stations are connected to the Internet in order to send and receive information, so it is very important to use cybersecure protocols, because if the protocols used are not secure, the information transmitted could be obtained by the attacker.
After knowing the different types of cyber-attacks that can be carried out, it is also very important to be aware of the risks and problems that this can entail, such as, for example.
- The electric cars can be infected through the charging station, this can be a big problem, as it can affect the correct functioning of the car and therefore affect the safety of people, both inside and outside the vehicle.
- Charging stations, especially those in urban areas or in residential car parks, are often connected to the same lines that are used to power buildings, so charging that has not been foreseen can lead to major problems. For example, studies document that if several charging stations are operating at the same time, they can affect the electricity in homes, creating voltage surges and dips, which would affect all electronic devices in the buildings. This is a big problem, as in some instances, you can have a control of all the sockets in the charging station and run them all at the same time.
- Another problem to consider is the data that is used in these stations, as very sensitive information is used, such as user IDs, bank cards, etc. The attacker could obtain this information and be able to impersonate the identity of the user using the charging station.
Possible solutions to cyber-attacks
Some of the possible solutions to prevent such cyber-attacks from taking place, or to minimise the damage they may cause, are:
- Integrate a solution into the devices so that they can detect whether the USB ports of the pen drives used are free of infection.
- Integrate EDR systems, so that if there is a problem within the device, it can be detected as soon as possible and solved.
- Use protocols that are cyber-secure and have encryption mechanisms, e.g. HTTPS protocol, instead of HTTP.
Conclusions
As we have seen throughout this article, charging stations are one of the infrastructures that must be considered, as currently and in the near future these types of facilities will be used to charge electric vehicles.
But like all new technologies, these were not going to be free from cyber-attacks, so it is very important to consider introducing cyber-security in these types of installations. Some ways to improve cybersecurity could be the integration of EDR systems in the devices or the use of secure protocols.









