LockerGoga: response and recovery actions

LockerGoga is a ransomware-type malware, used by cybercriminals to encrypt files and demand a ransom in cryptocurrencies to regain access to them. Although the vectors of propagation can be diverse, the most common is through phishing techniques and exploitation of vulnerabilities to infect systems, causing serious damage.
It was first discovered on January 24, 2019, during the attack on the Altran company and has since expanded to more than 1800 victims in 71 countries, including Norsk Hydro and Hexicon.
The operators of LockerGoga were arrested in October 2021, during a joint action by more than 30 countries around the world, which allowed law enforcement officers to find the cryptographic keys used to encrypt victims' data. A year later, Bitdefender published the decryption tool.
- LockerGoga distribution campaigns. Source McAFee-
Characteristics
Motivation
Most samples of this malware do not have a network access dependency to function; on the contrary, they try to disable all network interfaces to isolate the system and avoid possible detection mechanisms. In addition, it also closes the session of any user connected to the system, modifying all passwords, which makes it difficult to pay the ransom, since even the ransom note is inaccessible. This led several researchers to think that the goal was rather disruption and denial of service, rather than direct economic gain.
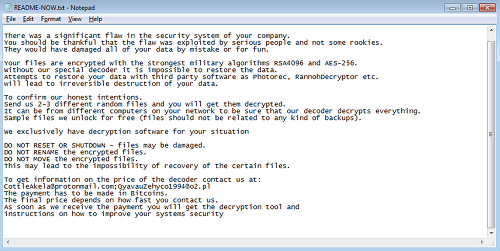
- Ransom Note. -
Detection evasion
Depending on the version of the malware, we can find several mechanisms to detect sandbox or evade AV and EDR solutions, executing a file called "kill.bat".
As mentioned above, the other method used to make it difficult for the security team to be alerted about the infection, and which in turn was implemented on most of its versions, was to try to disable all network interfaces of the device.
Encryption
LockerGoga uses AES with CTR mode to encrypt each file with a new 128-bit key. during the encryption process three items were added to the end of the encrypted file:
- The AES key.
- The initialization vector.
- The size of the original file.
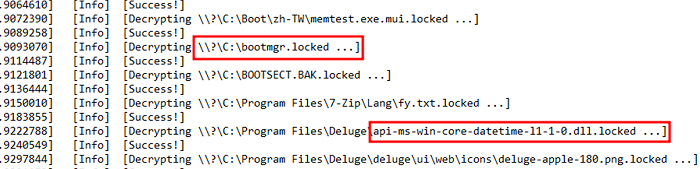
All of this is encrypted with a public key encoded in the main binary. Once encrypted, the file names are added with the ".locked" extension.
Some variants were also found to encrypt the Windows Boot Manager partition, as well as some system DLLs , causing the system to be left in an unstable state or unable to reboot. This could indicate a willingness to disrupt the target environment, but it could also be due to incorrect programming. Some samples analyzed by researchers also encrypted themselves, causing a glitch and stopping the attack. However, during other campaigns, the malware avoided specifically encrypting some system folders. This confirmed that the attackers developed and implemented improvements to fix errors and adopt a more efficient method.
Propagation
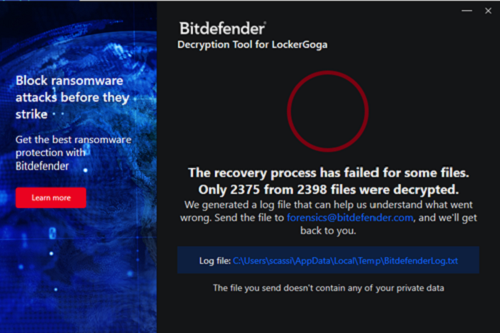
Propagation capabilities are also sample-dependent, some produce no network traffic, while others encrypt all shared files, but all use Remote Desktop Protocol (RDP) to move between systems and, using the SMB protocol, share malware payloads, manually copying them to each of the target systems. In several campaigns, the malware was loaded into the NetLogon directory of the Active Directory, making it accessible to all hosts registered in it, to be launched remotely using psexec.
This method of propagation proved effective and difficult for security teams to detect.
Response and disinfection
In addition to keeping all systems up-to-date and backing up systems, several additional measures can be considered on a regular basis when mitigating or recovering from a LockerGoga attack:
- Exploit the programming error in some samples: some researchers discovered a way to hinder the encryption process carried out by the malware that consists of stopping the execution of the malware by triggering an unhandled exception in the code through a malformed "lnk" file, present in the target folders ("C: " and subdirectories). However, some versions of LockerGoga have fixed this bug.
- Blacklist signing certificates: according to some research, it is possible to download one of the signature certificates and add them to the repository of 'untrusted certificates' (even if the certificates are revoked), so that the execution of the malware produces a file system error, with code 65535, leading to a crash on execution.
- Use the decryption tool published and documented by Bitdefender: The disinfection process would be as follows:
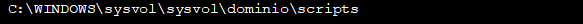
Download and install the program:
- Bitdefender Removal Tool installation screen. Source: own -
Read and accept the terms of use:
- Execution screen of the tool. Source: own -
Select "Scan entire system" to search for all encrypted files or select only the desired path:
Scan screen of the tool. Source: own -
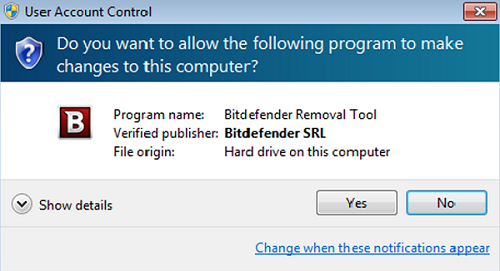
After validating the settings, the scan starts searching for encrypted files:
- Scan completion screen. Source: own -
After the process is complete, a summary of the decryption activity is displayed, indicating if any problems were found. In the case of the example, it appears that it was not possible to recover all files.
A log file is also generated. If you run the decryption tool multiple times, the logs are added to the same file, so no information will be lost. This file is generated to understand which files were not restored.
A contact email address is also provided so that the affected person can ask Bitdefender for help if their undecrypted files were important, and also to request an upgrade over the tool if an error occurred, which would hinder the decryption process.
- Log extracted from the tool. -
It is also possible to run the tool from the command line, which is very useful for automating the process on multiple computers or networks. The most interesting commands are:
• -help: provide information on how to run the tool silently (this information will be written to the log file, not the console).
• -start: allows the tool to run silently (without GUI).
• -scan-path: specifies the path that contains the encrypted files.
• -full-scan: will enable the 'scan' option for the entire system (ignoring the -scan-path argument).
• -disable-backup: disable the file backup option.
• -replace-existing: will enable the 'Replace' previously decrypted files option.
Other resources of interest:
IOCs:
• Github with multiple IOCs for LockerGog. to
Hashes and other resources:
• Abuse.io site with different resources.
Binary names:
• worker
• worker32
• bdf36127817413f625d2625d3133760af724d6ad2410bea7297ddc116abc268f_wQkb8SOVnc.bin
• svch0st.5817.exe
• svch0st.11077.exe
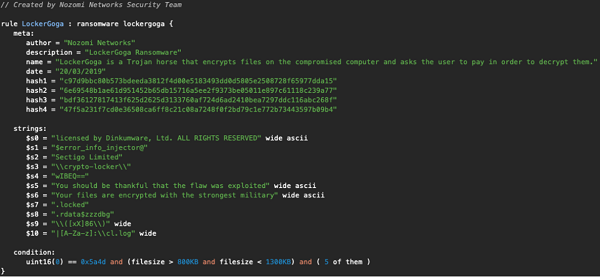
Supported Yara rules:
• https://pastebin.com/2wZWV4EU.
• McAfee.
• The Nozomi Networks Threat Intelligence.
Conclusions
During all known LockerGoga campaigns, no particular entry vector was found, as is usually the case with other similar types of malwares. The main vectors are suspected to have been phishing campaigns and stolen credentials. This is why keeping systems up-to-date limits the attack surface, both external and internal. Backups are the easiest way to recover from a ransomware attack, so they are often targeted by cybercriminals. Keeping them in a segmented and controlled network are highly recommended methods, as well as training and awareness of employees.









