New generation antivirus applied to OT environments

Attacks aimed at companies, that is, those that are less massive but focused on specific users or organisations, are becoming more frequent. Antiviruses (AVs) are always useful when it comes to improving our security, although in Industrial Control Systems it is usually more common to use white lists for levels 0, 1 and 2 of the Purdue model, leaving antiviruses only at level 3. For this reason, new generations (NG AVs), which, instead of being signature-based, use machine learning algorithms and other types of improvements, may make the difference for the better compared to what is already known in the OT world.
According to some companies focused on industrial cybersecurity, malware in ICS environments could be classified into three types:
- Malware without an objective. This type is not designed to infect industrial environments. As an example, the Sality or Ramnit family of malware are viruses that spread on Windows-based systems and ended up gaining access to industrial systems.
- ICS theme malware. Those that propagate by specific means to penetrate ICS environments. Cases of phishing through emails to manufacturers or operators are examples of this type.
- ICS-adapted malware. This type includes specific components and development efforts by authors of malware to target specific industrial environments. They represent the minority of cases and involve substantial resources, so they are usually developed by states or large organisations. The clearest examples of this type of malware are Stuxnet or BlackEnergy 2.
Conventional antiviruses work in the range of the first two types, but their effectiveness is almost nil against ICS-adapted malware. Moreover, due to the ease of intrusion achieved with ICS theme malware, most industrial antivirus solutions do not focus on identifying the most complex malware, because they are too specific and concrete (not valid for most clients).
One of the main objectives of NG antiviruses is to be able to detect ICS-adapted malware.
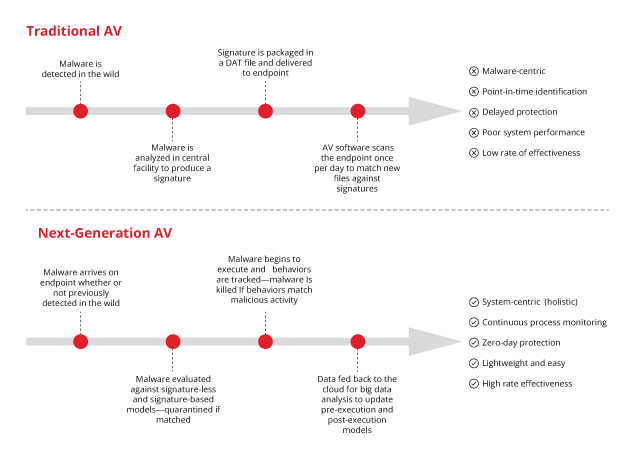
- Comparison between traditional and NG AVs -
Features of NG antiviruses
The reason why these endpoint detection and response (EDR) tools are needed is that files, programs or activities, which may be suspicious or have a malicious intention, should be detected as early as possible, alerting the person in charge so that he/she can take the necessary measures in time. NG antivirus enhancements are intended to make OT environments more secure and, thus, to prevent any possible infection. The most important characteristics are:
- NG antiviruses use artificial intelligence to block possible variants of unknown malware and thus to offer better protection than traditional antivirus solutions. They, thereby, attempt to predict possible future attacks.
- They do not overload the systems and are transparent to the user, offering them a user experience that is not slow, noisy or full of pop-ups associated with traditional consumer security products.
- NG antiviruses, unlike traditional antiviruses, are not dependent upon signature updates.
- Easy to manage and configure. They protect the devices to give maximum security.
- This type of antivirus gives the technicians responsible for managing them a simple way to view and know the security status in industrial devices through dashboards.
- Use of improved algorithms so that the security of NG antiviruses provides systems with an efficient defensive approach against any cyberattack.
- Application of predictive and prevention security, in addition to specialist security services.
Advantages and disadvantages of NG antiviruses in OT environments
Within Industrial Control Systems (ICS), the use of antiviruses provides another layer of security against possible cyberattacks, but in turn, deploying them is quite delicate, since software that has an objective such as NG antiviruses (to detect and deter threats) could erase files resulting from a false positive and affect the availability of industrial processes, so caution must be exercised and it is necessary to ensure that it is configured correctly. Even if the complexity of its deployment is high, there are a number of advantages to be considered:
- Thanks to the prevention of AI-based malware, application control, memory protection, control of policies that devices possess, and other security measures are greatly improved by being able to apply the knowledge learnt for each new investigation.
- This type of antivirus protects end devices without increasing workload or staff costs.
- The use of predictive and preventive techniques used by artificial intelligence are applicable through platforms, OOSS, file types or devices.
- It is possible to integrate artificial intelligence into SIEM platforms that are already deployed, besides providing more flexible solutions for security, through intelligence that makes it possible to determine whether a given traffic is valid whether it comes from a specific location, since that same traffic could be considered malicious if the origin is different.
- The use of traditional antiviruses could cause a huge number of difficult-to-handle alerts, but the use of the new algorithms at the endpoints reduces the memory and CPU usage needed.
- Improvement due to the change in antivirus by not having to update the endpoints, using signature-based updates and without the need to connect to cloud services that could be dangerous.
Although it seems that NG antiviruses may be a breakthrough for the OT environment, it is possible that there are also some drawbacks. These could be:
- Lack of need when it is updated. As they are not signature-based, it can be a problem due to the change in methodology, since today all the antiviruses used in Industrial Control Systems have a specific way of acting and, above all, of updating.
- Changing from traditional to new generation antiviruses will cost the company, on top of a possible architecture redesign or changes when it comes to seeing where to install these AVs.
Conclusions
The evolution of conventional AV to NG antiviruses may mean a change for the better in how the OT security is assessed, thanks to the use of new algorithms, machine learning or the introduction of artificial intelligence. However, even if these new antiviruses are implemented, it must not be forgotten that there will always have to be a person in charge of them, almost certainly an operator, who will be responsible for the revision and the set-up, as well as for continuing to use good practices.









