Preventing the leaking of information in ICS

The transfer of sensitive information between the network of a victim organisation and an external location controlled by attackers external to the organisation or by so-called insiders is known as data exfiltration, or information leakage. When an event of these magnitudes occurs, it is common to think that a cybersecurity incident has occurred and that a non-legitimate user has gained access to the company's network.
As some studies carried out by security firms show, most commonly (57% of cases) is that incidents related to exfiltration are carried out by people outside the organisation. Another important fact from the study is that about 20% of exfiltration cases are caused unintentionally by internal employees. One of the most direct measures to avoid these types of situations is to make employees aware of how to handle company information, such as how they should use their social networks so that they do not expose information unintentionally.
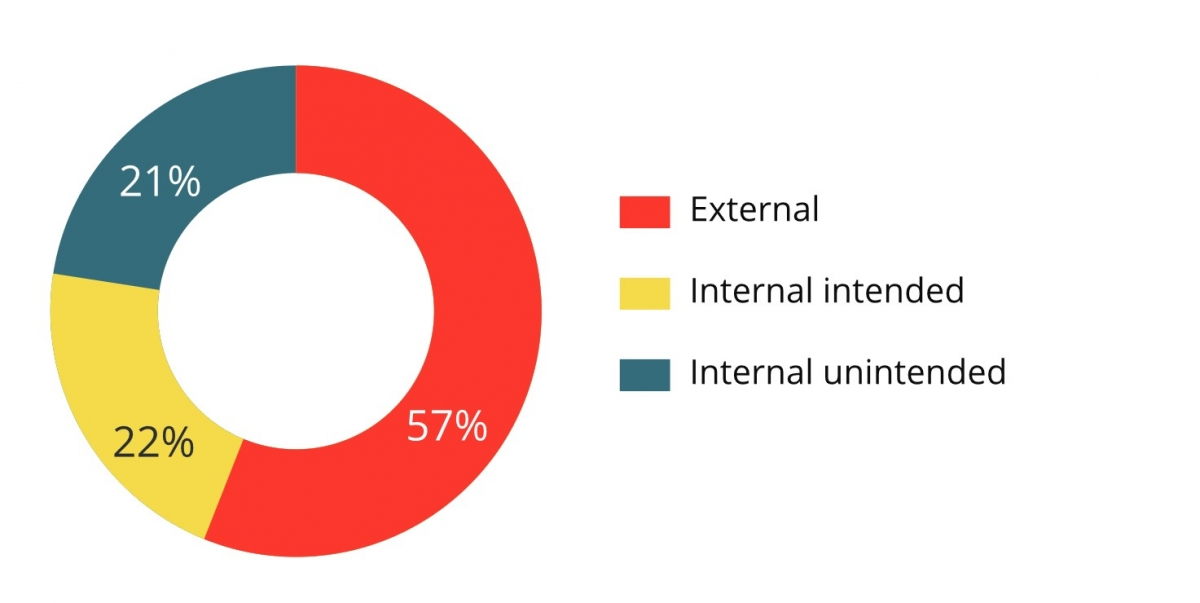
- Actors involved in an information leak (September 2015). Source: McAfee -
The leakage of certain information could affect the availability of the system in use, which is the most important factor in industrial environments. Advanced cyberattacks, such as the one detected in Ukraine at the end of 2015, show the importance of certain information such as: network schemes, memory addresses of industrial devices, behaviour of inputs and outputs, etc. An information leak does not have to directly affect the industrial network, but it could occur in the corporate part and provide the attacker with the necessary information to subsequently carry out a more elaborate attack that could affect the industrial network and stop production.
On the other hand, there are assets within industrial networks that have information of great importance for the proper operation of industrial processes, such as historians, databases storing information about the processes executed in an industrial control system or engineering stations. In the case of historians, there are companies that base their production on the data collected over a day, a week, month, etc. That is why the exfiltration of this data could be advantageous, both for the competition and for other actors interested in performing malicious actions.
For their part, workstations usually have computer support from the manufacturer or developer, who carry out different programming to adjust industrial processes, incorporating new assets in an industrial plant and endless operations that depend, in many cases, on this programming. An exfiltration of the information contained in these programs could, sometimes, be a great advantage for cyberattackers seeking thorough knowledge of the variables and addresses that interact in the process. An attacker could thus obtain complete knowledge of the processes, from the variables that act on the PLCs to the architecture of the industrial network.
Possible data exfiltration routes
Information leakage routes are very numerous:
-
Peer-to-peer (P2P): the use of these networks is usually a means used by cyberattackers to extract data. P2P networks are commonly used for file sharing and their use can be a cyberattack vector. Within the automation pyramid it is sometimes common to see point-to-point networks at level 1 between controllers for cell/area management.
An attacker could take advantage of these channels to exchange information through an organisation's networks to finally send the information to an external server it has control over.
To avoid these situations, it is advisable to properly filter communications with specific firewalls at an industrial level and, more generally, where more corporate communications with other industrialists can coexist, to have good segmentation and make use of different DMZs specific to each environment. -
Removable storage devices: removable storage devices, such as USBs or CDs, are a possible channel of information leakage. In this case, the person executing the information theft must have physical access to the machines where the target information is located. This type of information exfiltration is more trivial for an insider than for an external attacker. To prevent both the exfiltration of data and possible infections, it is advisable to disable the use of these means in the machines, as long as their use is not strictly necessary. In the latter case, it is advisable to control who has physical access to the machines and have a white list of permitted removable media. As an extra measure, it is also advisable to disable their self-execution.
-
Own communications for data exchange: protocols such as FTP (File Transfer Protocol), TFTP (Trivial File Transfer Protocol), SFTP (SSH File Transfer Protocol), etc. They are widely used to transfer files, both in corporate and industrial networks, and could also be a way of leaking sensitive information. To prevent cyberattackers from using these means in order to exfiltrate information, it is advisable to control the data flow of such protocols between internal and external networks to the organisation. Another recommendation is the use of secure protocols such as SFTP or FTPS (FTP Secure), since they use encryption for file transmission.
If these communications are used to exchange information with public servers belonging to the organisation itself, it would be advisable to use traffic monitoring tools. -
Undercover channel with industrial communications: one of the ways to perform data exfiltration between industrial devices was investigated and executed thanks to the use of the Modbus TCP protocol. This research mentions how using headers of the Modbus TCP protocol in communications between master/slave, it is possible to exchange data that is not considered legitimate.
To establish the undercover channel, a “secret” master sends a request to read the object of a “secret” slave from the different registers that Modbus uses (coil, discrete input, holding register or input register). Then, the "secret" slave receives the request, verifying the function code and the object number that it is asked for. The “secret” master always uses the “read-only” frame function, so that any firewalls in the SCADA do not block the exchange of messages.
The mitigation measures for this attack are related to the configuration in the SCADA. If there are security controls such as firewalls or IDS, they must be configured to allow valid Modbus TCP objects, but with the object number used in that network. -
Side-channel attacks: side channel means a non-functional transmission of information about the status of a system. For example, electromagnetic radiation in silicon chips is not a main function, but a feature derived from the electrical operations performed. The radiation emitted by the PLC control chip involves important information about the operations that are carried out, such as the type of actions to be carried out and their frequency. A cyberattacker could put a probe, analyse the signal on an oscilloscope and gather information about the PLC activity.
These are some of the possible information exfiltration routes, although there are many more, some of them more elaborate, such as the use of DNS requests to filter information or even using the RF signals that some PLCs emit to inject the information into these signals, as demonstrated by researchers at the Industrial Control Systems (ICS) Cyber Security Conference.
In addition to these exfiltration routes there are some more traditional ones, such as the use of photographs, theft of equipment or documents or even the use of emails to send information. Therefore, we should also implement rigorous access control, so that anyone, whether external or internal, with access to the facilities, is controlled and cannot exfiltrate the information by following these simpler methods.
What to do when an information leak has occurred?
The different steps to be taken after an information leak were already set out in a guide developed by INCIBE and aimed at entrepreneurs. This guide provides an approach to managing an information leak. The steps to follow, even when talking about industrial environments, closely resemble those already mentioned and are divided into six phases:
- Initial phase: this is the phase in which the incident is discovered. The most important thing in this phase is the early detection of the incident, so that it is identified before the leak is made public to reduce the response time to it.
- Launch phase: once the incident is detected, the crisis committee must meet. At this meeting, the committee must set out all the decisions and steps to be taken to address the incident. It is important not to take action on your own that have not been proposed by the committee.
- Audit phase: in this third phase, an internal audit must be carried out to obtain information about the incident. In this phase, among other things you should obtain at least:
- The amount of information stolen.
- The type of information stolen.
- Origin of the information (internal or external).
- The cause of the leak.
- Determine the scope of publication of the information.
- Determine what information may have been published.
- Possible news about the incident are collected.
- The reactions that are occurring in relation to the incident are known.
- Evaluation phase: the objective of this phase is to determine the scope and possible consequences and impact of the incident. The crisis committee will meet again, the audit report will be submitted and the main actions to be carried out will be planned.
- Mitigation phase: in this phase, an attempt should be made to mitigate as much as possible the impact of the incident in the shortest possible time, communicating with those possibly affected by the information leak and solving the security breach exploited in the leak.
- Follow-up phase: in this last phase the result of the actions carried out in relation to the consequences of the incident and its impact will be evaluated. Taking into account the final assessments, the definitive measures will be designed and implemented to avoid new leaks and restore the normal operation of the affected services and infrastructure.
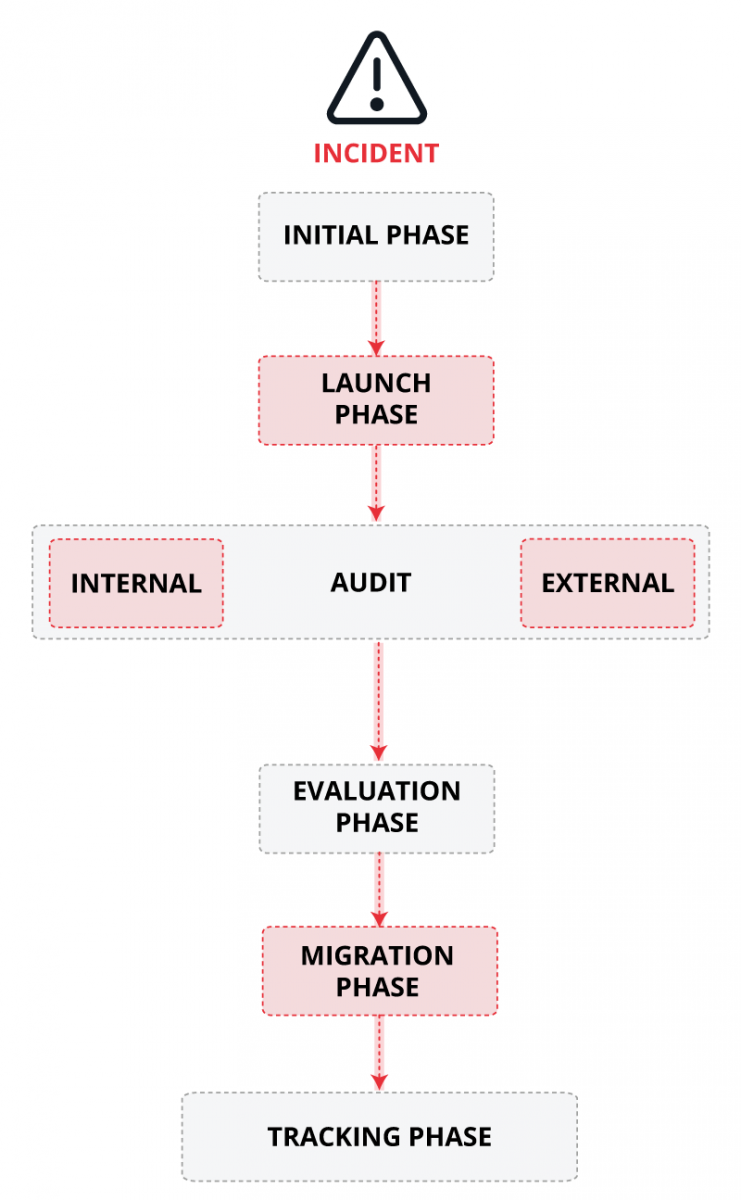
- Phases of action after a cyberattack. Source: AEPD -
Tools to prevent data exfiltration: DLP
It is useful to comment on the technique called DLP (Data Loss Prevention) used to ensure that sensitive information is not lost in an organisation. DLP software classifies the most critical information and identifies any violation of the policies defined by the organisation or those already predetermined by law, such as GDPR in the case of Europe.
There are three types of DLP tools depending on the mobility of the information being protected.
- Information in use (endpoint actions): it protects the data that are being processed constantly.
- Information on the move (network traffic): it ensures that confidential information is not routed outside the organisation when it is transmitted throughout the network.
- Information at rest (data storage): it preserves the integrity of the data even if they are not being used.
This method allows an organisation to keep track of its data and avoid both data loss by mistake and intentional information leakage.
Conclusions
An exfiltration incident can cause a loss of confidentiality in the organisation's sensitive information. This would allow cybercriminals to develop complex attacks with serious consequences for the availability of operations, one of the fundamental cornerstones of all industrial processes. Therefore, it is advisable to use a well-segmented network with comprehensive traffic control that makes it possible to detect anomalous data flows between assets and, if possible, using other mechanisms and security measures at other levels, such as disabling removable media or using DLP tools.
The reduction of the possibility exfiltration incidents happening is achieved with training for employees on the processing of information and through constant control of information transmission means.









