Real-Time Operating Systems, hardening and functioning

Industrial control systems (ICS) carry out very varied processes that are carried out by very diverse teams. Some of these processes, by their nature, involve time requirements and real-time applications, so they use real-time operating systems. Some examples can be the presses of a printing press, which require very precise and determined times to apply the colors at the appropriate moments to each page; or a machine tool destined to the manufacture of a specific piece, that must finalize each piece in a concrete time, for example 2 pieces to the second.
Real-time operating systems vs. General purpose systems
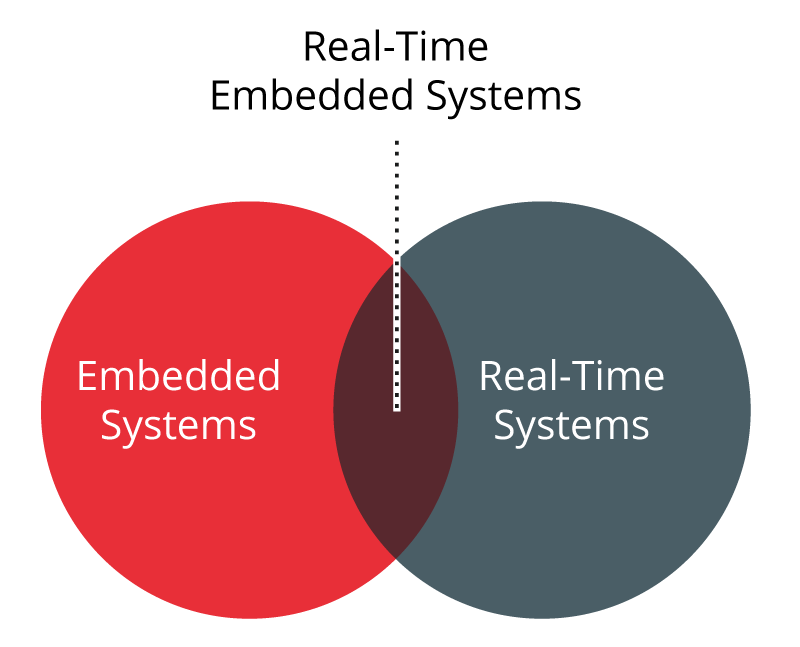
Real-time operating systems are a specific type of system developed to run applications that have some type of time restriction. These applications are characterised by having specific execution requirements and response time, either to execute the actions in less than a predefined time or to execute them at specific intervals.
-Division of operating systems-
Mainly, Real Time Operating Systems, RTOSs, have special requirements, which differentiate them from the rest, in 5 specific areas:
- Determinism: is known as a deterministic operating system that performs the actions within a specific time interval or bounded. A general-purpose operating system cannot guarantee determinism.
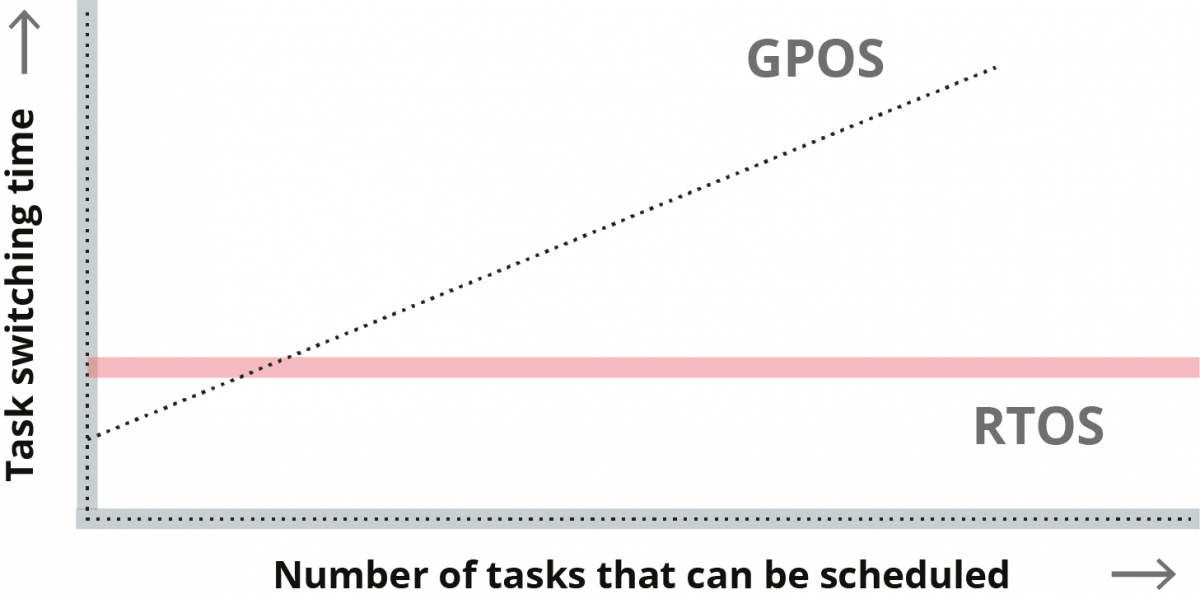
- In-time response of RTOSs and GPOSs -
- Sensitivity: the sensitivity of an operating system is the time it takes to recognise an interruption and start the routine of its treatment (ISR - Interrupt Service Routine). As a general rule, a ROTSs will be more sensitive at the beginning of this routine.
- User control: users have more control over processes.
- Reliability: through watchdogs that are responsible for restarting any process that fails.
- Fault tolerance: are designed to respond adequately to various forms of failure, even concurrent.
In order to meet these requirements, ROTSs implement the following characteristics:
- Support for the process planning: support for the creation, planning and deletion of multiple processes in counterpart of a general OS, in which, it is he who determines the order of execution of the processes.
- Priority Process Planning: higher priority processes are always going to be executed before lower priority processes, even if they have less waiting time in the queue or another lower priority has already begun to run. In general OSs, normally, if a process is running, it must wait until it is finished so that the highest priority can be executed.
- Guaranteed interruption response: they quickly recognise the occurrence of an interruption or an event and take a deterministic action to deal with said event.
- Communication between processes: communications between processes are supported in a precise and stable way, using mechanisms such as the use of traffic lights, the passing of messages and the use of shared memory.
- Acquisition of data at high speed: being able to use data sets at a high acquisition speed, providing the necessary means to optimise disk storage.
- I/O support: because real-time applications usually include a number of input/output interfaces, RTOSs provide the necessary tools to incorporate specific I/O devices. In addition, an ROTS performs the I/ O asynchronously, so that a process can initiate an I/O operation and continue its execution concurrently to the I/O operation.
- Control of the system's resources by the user: users are provided with specific control of system resources, such as CPU, memory and I/O resources.
It is necessary to know well the functioning of these systems and what they can contribute, since only if we consider their particular characteristics will we be able to carry out proper hardening.
Hardening measurements of real-time operating systems
Like any operating system, in RTOSs it is possible to carry out some actions and configurations that allow you to raise and improve the security of the device. However, before applying any of these hardening measures, it will be necessary to study their impact on the operation of the system.
Real-time applications have very specific response time requirements, which cannot be affected by any of these measures, which is why, although these measures a priori seem common to a general-purpose operating system, their impact on the operation of the system is not the same. The security measures to follow are:
- Performing a partitioning of the system: the main components of the system can be separated into different partitions so that in case of compromising a part of the system does not affect the rest of the partitions.
- Enable secure boot: If possible, it is recommended to enable safe boot of the devices so that the boot image is cryptographically signed with an identifier that the hardware contrasts during the boot process of the device.
- Disabling all unnecessary services: it is advisable to carry out a study of all the services enabled on the device and disable those that are not strictly necessary.
- Enable user authentication and privilege levels: accesses to the device must follow an authentication process and different levels of privileges must be enabled for users according to the requirements of their operation.
- Prevent the execution of applications with administrator permissions: whenever possible the applications will be executed with user privileges.
- Secure communications: whenever possible, and does not affect the operation of the devices, enable the encryption of communications. Nowadays, some CPUs have hardware acceleration that allows the use of cryptographic libraries without impact on CPU usage. If it is not possible to enable this encryption it is advisable to consider the use of VPN tunnels to secure communications.
- Enable the operating system firewall: the most modern ROTSs implement an OS-level firewall which further increases their security over older operating systems.
Conclusions
Real-time operating systems are a subset that has specific features within control systems operating systems. Just as we would apply security measures on computers running a general-purpose operating system, we must also ensure that we apply measures to computers running real-time operating systems, always after a previous study of their impact and without forgetting the particular needs of them, thus ensuring a higher level of security in all equipment of our facilities.









