Security in Protocols for Building Automation

A while ago, a post in this blog reviewed several aspects related to smart buildings. See BMS: Intelligent buildings – are they secure? This post already mentioned certain characteristics of used protocols, but did not describe in detail the architecture of protocol messages and security measures and their implementation. This article is focused in BACnet and LonWorks protocols, which are analysed in the same way as in other protocols analysis, such as those regarding zigbee or Bluetooth.
The most important difference between these two building automation protocols lies in the fact that LonWorks is more focused in processing incoming information from sensors and actuators, while BACnet is more management and data display oriented.
BACnet
BACnet's architecture is formed by four layers based on the OSI model: Physical layer, Data link layer, Network layer and Application layer, although only Network layer and Application layer are purely BACnet.
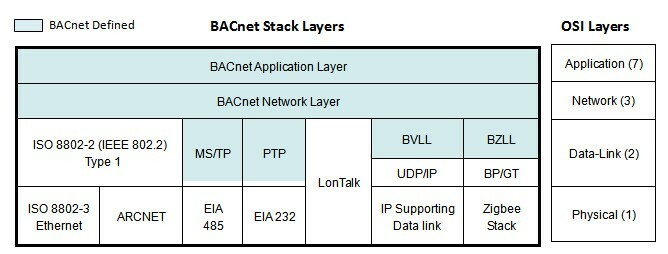
-BACnet layer architecture-
At a data link and physical layers level, BACnet uses different protocols such as Ethernet, BACnet/IP, ARCNET, MS/TP, LonTalk or PTP; which sets different BACnet variants:
- BACnet/IP: This specification is defined in Annex J of BACnet standard in order to be able to work with IP addresses and ports, which allows it to run over the available Ethernet architecture, as well as to use of VLAN networks. This annex defines the use of 16 UDP ports. It is different from BACnet/Ethernet in the fact that it uses IP addresses instead of MAC addresses.
- BACnet/Ethernet: Variant used directly with Ethernet 8802-3 networks. It may run on different physical supports, such as cable or optic fibre. It is limited to physical infrastructure that only uses MAC addresses to establish communications.
- BACnet MS/TP: BACnet based in the master-slave model or the token passing model in the data link layer. This BACnet variant uses a serial channel, typically RS-485, for communications.
- BACnet PTP (point-to-point): This type of media access control is only used over telephone networks. The EIA-232 type of direct connection is less and less used, and Ethernet is usually preferred in its place.
- BACnet over ARCNET: This variant allows using BACnet over a coaxial cable or a RS-484 serial cable. It improves slightly the BACnet MS/TP features but few manufacturers support it.
We shall focus on the security of BACnet protocol security, including security keys, encryption models or authentication systems.
Keys
BACnet defines 6 different types of security keys to be used depending on the task to be carried out. Keys are distributed to all devices from the network security key server, some of which are even distributed jointly. It is not necessary to assign the security key server function to a specific device, but there must be a server containing all keys and a list of all devices to be managed. The relevant standard does not describe how this server must be deployed. The types of security key are:
- General-Network-Access: Used for linking devices and objects, in order to create encrypted tunnels and a user interface for those devices that lack user authentication capabilities.
- User-Authenticated: Security key distributed to client devices with user authentication capabilities or those who lack a user interface.
- Application-Specific: Provides security limits between application areas. It is only distributed to devices that share certain specific applications.
- Installation: This security key is only distributed to a small number of devices, typically to the configuration application and to those devices that require configuration.
- Distribution: This key is used to distribute the General-Network-Access, User-Authenticated and Application-Specific keys in a secure manner.
- Device-Master: It is only used to distribute the Distribution key. This key is unique to each device and must be kept as secure as possible.
Network security policies
BACnet applies message security at the network layer. BACnet non-encrypted messages are placed in the data section of a new secure message. This encryption is subject to 4 network security policies depending on whether hardware security, protocol security or no security is applied:
- Plain-trusted: requires physical security; no protocol security applied
- Signed-trusted: physical security not required; secured with signatures
- Encrypted-trusted: Security is ensured by means of encryption, implemented by AES and thus physical security is not required.
- Plain-non-trusted: not physically secure; no signature or encryption applied. Plain text message.
BACnet security messages use the same security frame consisting of a fixed header, an optional body and a required signature.
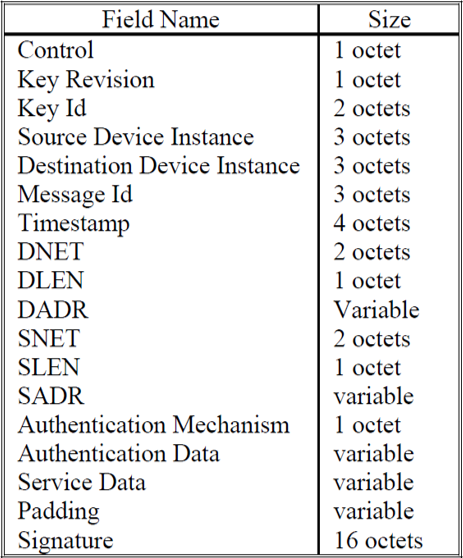
-BACnet security message fields-
Basic security level implemented to each message to make it secure is adding a HMAC signature.
Secure BACnet devices are set to a basic device security policy which establishes the minimum security level for sending or receiving messages in the relevant device.
Authentication
In all cases where a message is deprived of security measures, either in the target device or because the target device has a different security policy, messages must be authenticated. Such authentication consists on validation of source MAC address, an unique message ID, a time stamp, and the message signature.
Regarding user authentication, BACnet security architecture allows several authentication methods, but only one is defined: proxy user authentication. It is foreseen that, in the future, more authentication methods may be defined.
Main threats
The features described above, proposed in “Addendum g to BACnet Standard 135-2008”, allow to prevent a series of attacks on BACnet networks. Among them, the following are especially noteworthy:
- BACnet spoofing: This attack is similar to ARP spoofing or IP spoofing, which occur in the IT environment. Compromised devices generate fake messages that force other devices to send their own messages through the attacking device.
- Denial of Service Attacks: This attack is carried out by flooding the BACnet network. The attacker sends broadcast messages to an unspecified list of target devices, to which all devices must answer, creating unnecessary traffic in the network.
- Attack on writing capabilities: This changes the current value of the BACnet object properties. The result of this attack depends on the object and property affected.
- Disabling network connections: This may be done by means of several BACnet services. BACnet network routing tables may be corrupted by a compromised device which shares faulty routing information. It is also possible to disable network connection by sending specific false messages.
Lonworks
Unlike BACnet, LonWorks is a proprietary technology which requires a specific Echelon chip called Neuron. Despite this, LonWorks is used by millions of devices for building automation thanks to its low cost and its flexibility for integrating components from other manufacturers.
LonWorks is the name of the technology. The protocol used is called LonTalk and is based on the open standard ISO/IEC 14908. This technology operates similarly to a LAN network, hence its name. LON (Local Operating Network).
At a physical level, LonWorks may operate over twisted pair cable, Ethernet, electrical conduction cable (PLC), fibre, radio, etc., which makes it a highly versatile technology.
This technology architecture is designed to operate in couples, so that any device can talk to any other without any restriction whatsoever. This allows for bus, ring, star or hybrid topologies.
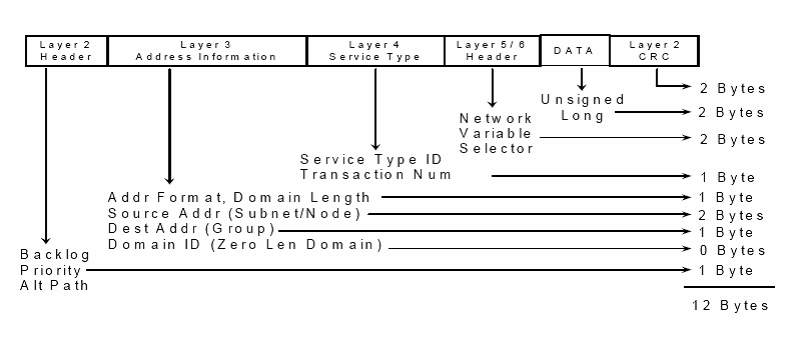
-LonTalk protocol frame format-
Security
The LonTalk protocol does not implement data encryption. It only features sender authentication as a protection measure. Data encryption is usually used to hide data while sender authentication is used to verify that the sender of a message is an authorised sender.
This verification is based on a unique 48 bits security key for each device, which must be placed before or during installation. This key is called authentication key, cannot be read outside the Neuron chip and cannot be modified without previously knowing it. Each device must be aware of the key for each network member. This device shall authenticate its identity in all messages, so that the receiver shall respond to each message which a challenge in the format of random 64 bit number. The challenge receiver shall carry out an authentication transformation based in its private security key and shall send back the response to the calculations to the receiver of the original messages, which shall have carried out the same calculations using the sending device known key. If both results match, the original message shall be processed.
The authentication key is not transmitted at any time. If traffic was to be intercepted, only the message would be shown, followed by the random number and a transformation. Mathematically, even having the random number and the transformation, is virtually impossible to find out the security key.
Although at a security level this mechanism is appropriate for sender authentication, it must be considered that the text is still transmitted in clear text, which allows interception of network traffic although new messages cannot be inserted.
At a data traffic level, it must be considered that exchange of information is considerably increased, due to the transmission of challenge-response packages.
In April 2015 a report on cryptanalysis stated that the algorithm used by standard ISO/IEC 14908, on which LonTalk and many other protocols are based, was insecure by default. The solution is to use authentication encryption such as in AES-CCM or AES-GCM
Since 2014, it is permitted to use BACnet over LonTalk, joining technologies of two long-time rivals in building automation. This allows to use BACnet along all automation processes, from management to sensor and actuator control, applying the security characteristics provided by BACnet and which improve the features of LonWorks.









