Shadow IT exposed: risks and best practices

The adoption of technological tools is essential to boost business productivity, improve efficiency and maintain competitiveness in an ever-changing market. However, in this technological context, a new risk appears: the Shadow IT, a term that refers to the practice where employees use applications, devices, and technological services without the approval of the company's IT departments, either due to ignorance or premeditated. This phenomenology has gained traction in the business environment, and its relevance lies in challenging the traditional IT structure and raising crucial questions.
According to The State of Remote Work, published by Lookout, 32% of telecommuting employees use unauthorized software, and 92% use personal, unregistered devices for corporate tasks.
Typically, IT faces budget, resource, and time constraints, which can delay the adoption of new technology solutions, or simply implement restrictions due to security issues. Employees, faced with the need to address milestones and specific urgent problems or for the convenience of avoiding bureaucratic processes, or blockages, implement their own "shortcuts" without the knowledge of the top management of the organization and without being aware of the problems they can cause.
Shadow IT's motivation lies in its ability to quickly meet emerging and specific employee demands, but it poses considerable risks to businesses. One of the main problems lies in the lack of control and visibility by IT management and information security.
When employees use unauthorized applications, the company is exposed to cybersecurity threats, data loss and vulnerabilities, so properly managing this practice has become a critical challenge for system administrators and security managers.
Risk
As we have seen, for convenience, ignorance, or lack of resources, on many occasions employees choose to seek unauthorized technological solutions to meet their specific needs. Next, we will see some of the most outstanding manifestations of this practice in the business context and the associated risks:
- Unauthorized applications: The use of messaging applications, cloud storage, or collaboration tools that have not been approved by the IT department. If these applications are not properly controlled, they can expose your organization to:
- Exposure to advanced malware, including ransomware, spyware, and rootkits, which can spread quickly through the corporate network.
- Leakage of sensitive data, including intellectual property, financial information, and personal data of customers.
- Privacy threats, because these apps could collect personal data from employees and customers without their consent, which raises privacy concerns and can result in non-compliance with regulations such as the GDPR (General Data Protection Regulation).
- Bring Your Own Device (BYOD): The practice of using personal devices, such as smartphones, tablets, or laptops, to access organizational resources poses a great risk, since these devices do not have the hardening or policies necessary to adequately protect the organization's data.
- Security vulnerabilities, unmanaged devices may lack up-to-date security patches and proper configurations, making them vulnerable to exploits and attacks.
- Loss of network control, challenging the integrity of the corporate network, as IT administrators can lose visibility and control over these unmanaged assets.
- Coexistence of personal and professional data, which can cause crossings, leaks, or loss of information between different areas.
- Transparency services and cloud storage and unauthorized collaboration tools: the use of non-corporate or personal file sharing or transfer platforms is another common practice that can involve:
- data leakage in the cloud, as it can result in accidental exposure of sensitive data, sharing improper public links or setting permissions incorrectly;
- threats to data integrity, lack of control over the cloud can open the door to unauthorized manipulation of data, undermining the integrity of stored information;
- inadvertent disclosure of information, through documents displayed in these services;
- exposure to phishing attacks: Cybercriminals can take advantage of security weaknesses in these tools to launch phishing attacks, tricking users, and compromising login credentials.
- Modified software: Some employees with technical skills may choose to create their own custom software solutions , or scripts to address their operational tasks.
- vulnerabilities in modified software, since they do not follow the software life cycle dictated by the organization, will lack mandatory quality and security audits, so they may contain vulnerabilities in the code, undetected, and that could be exploited, putting security at risk;
- lack of maintainability, since the functionalities implemented may become obsolete or require new, more complex needs, which cannot be addressed by the employee, and may no longer be compatible with new versions of the product, harming operations;
- Challenges in documentation and support, in addition to lacking the necessary visibility, the lack of documentation and adequate support for custom software makes it difficult to manage, maintain and monitor and resolve problems, which can affect the operation of the organization and suppose a breach of the possible regulations and certifications that the organization has.
Good practices
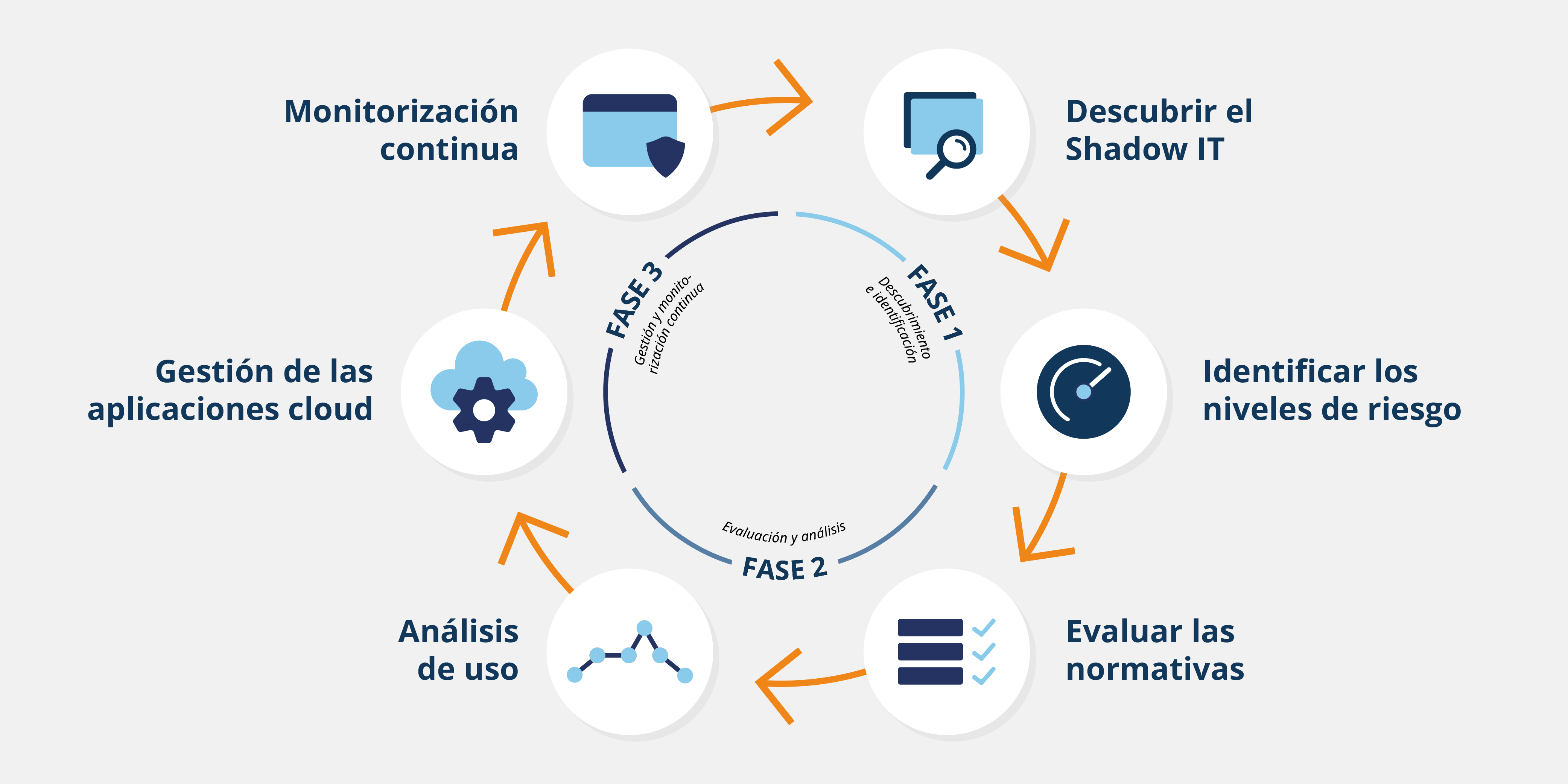
The Shadow IT represents a constant challenge in the field of cybersecurity, given its potential to expose the organization to significant and uncontrolled risks. To address this problem effectively, it is crucial to implement specific strategies and approaches to identify, manage and minimize the associated risks:
- Phases of an effective Shadow IT management -
- Continuous discovery and monitoring: the proactive detection of Shadow IT through the implementation of advanced tools, allows to identify in real time unauthorized applications, devices, and services in the corporate network. Some examples of tools include network discovery systems, such as Snort and Suricata, as well as SaaS discovery services. Microsoft Defender also has Cloud Discovery, as a tool for the detection, evaluation and control of authorized applications.
- Cloud Discovery deployment process -
- Cybersecurity awareness: Digital education and employee awareness are essential to combat Shadow IT. Providing employees with a solid understanding of the associated risks and the organization's security policies will help reduce the likelihood of unauthorized practices. Implementing cybersecurity training and awareness programs can be highly effective in keeping employees informed and alert.
- Clear policies and procedures: Establishing clear policies and procedures regarding the use of technology in the organization is essential. These policies should be specific, detailed, and easily accessible to employees. Some key considerations include:
- The implementation of a formal process for approving applications and services by the IT department.
- Clear policies for personal device management (BYOD).
- Guidelines on using cloud storage services and collaboration tools.
- Identity and Access Control (IAM): Implementing such advanced solutions allows for more granular control over access to resources and applications. Examples of IAM solutions include:
- The implementation of single authentication (SSO) systems through the use of two-factor authentication, which centralize user authentication and authorization, thus reducing the proliferation of unauthorized passwords.
- In addition, establishing role-based access policies ensures that users only have access to authorized systems and data based on their role in the organization.
Conclusion
Shadow IT is a phenomenon that has gained prominence as organizations have sought to strengthen their security controls. Although at first glance it may seem that the stricter the security controls, the more protected a company will be, in practice, over-regulation can have a counterproductive effect.
When security solutions hinder day-to-day operations too much or make employees' jobs difficult, employees are likely to look for unregulated alternatives or "backdoor" solutions to carry out their tasks that may make work easier in the short term, but lack adequate protections, potentially increasing the risk of security breaches.
Therefore, it is critical that organizations seek a balance between the need to protect their assets and the importance of maintaining staff productivity and morale. "Wearable security" is not just an ideal, but a necessity in the modern world.
A well-defined strategy will focus not only on implementing security controls, but also on ensuring that these controls are intuitive and do not unnecessarily hinder the workflow. It is essential that organizations consider the human impact of their security decisions, convey the need and reasons for compliance, and work to continuously improve those controls.









