SIEM deployment in OT environments

What is a SIEM?
A SIEM (Security Information and Event Management) system is a tool used for centralised storage and interpretation of important security data. A SIEM system is the combination of the SEM and SIM systems:
- SEM (Security Event Management) provides a real-time monitoring capability, event correlation, notifications and console views.
- SIM (Security Information Management) includes the set of capabilities for long-term storage, analysis and presentation of registration information.
SIEM is the main tool used in SOC (Security Operations Centers) for incident detection and response. The main capabilities of a SIEM are:
- Data aggregation: capability to manage information received from multiple sources.
- Correlation: processing of the received data to transform such data into information.
- Alert: analysis of correlated events, so that security notices that are sent to an administrator are generated.
- Dashboards: a SIEM has the necessary tools to transform information into tables and graphs.
- Compliance: thanks to a SIEM, the gathering of the information necessary to prepare reports on existing regulations can be automated.
- Retention: a SIEM has capacity for long-term data storage, a feature that is vital for the proper performance of forensic analysis functions.
- Redundancy: to avoid data loss, the database of a SIEM is usually redundant.
- Scalability: a SIEM can be configured hierarchically to increase or decrease, depending on the needs of the moment.
Advantages of deploying a SIEM
Deploying a SIEM will offer us a series of security-level advantages:
- Early detection of an incident: thanks to the real-time analysis, the use of a SIEM makes it possible to detect an incident occurring in our network, and even makes it possible to carry out actions necessary to block such incident before it causes real damages to the production.
- Forensic analysis: another point in favour of a SIEM is that, thanks to its ability to store and consult earlier security events, it makes it easier to carry out a forensic analysis if you want to identify how an incident occurred.
- Centralisation of information: thanks to gathering network machine events and other security elements in a SIEM, it makes centralised management of all that information gathered possible.
- Saving of resources: when information is gathered centrally and automatically, significant savings in resources are achieved.
- Identification of anomalies: thanks to the fact that industrial networks are commonly stable, a point in favour when deploying a SIEM is that it will allow us easily to identify, after a period of learning, anomalies in the behaviour of the machine; we will be able to detect operating problems or even an incident.
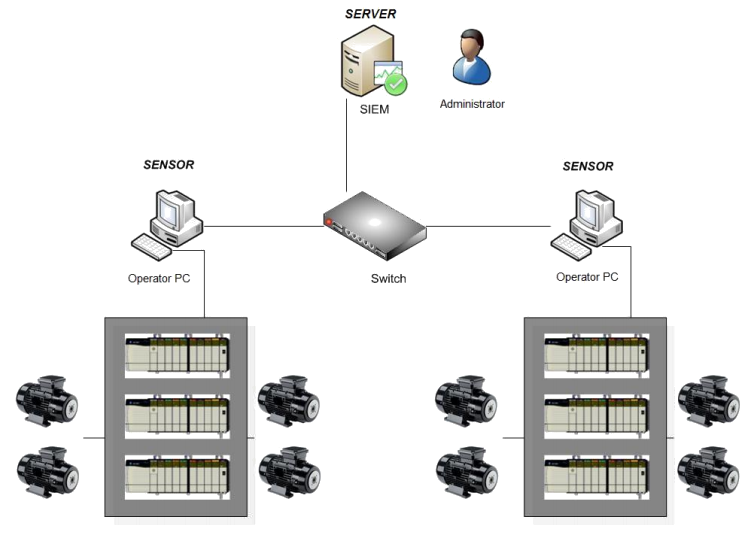
- Example of SIEM in industrial network. -
Peculiarities and problems of SIEM in ICS environments
Due to the peculiarity of OT networks, the deployment of a SIEM is not a trivial task and some characteristic problems of these environments must be overcome:
- Very long device life cycles: something that is very common in industrial environments is that the machines' life cycle is very long, reaching up to 40 years depending on the industry.
- Device performance: another very common quality of industrial devices is that they are very low-performance machines, usually with the right capacity to perform the tasks they have been allocated. Therefore, they often do not have the capacity to generate and send logs. Due to this lack, one of the problems when using a SIEM in ICS is the generation of security events on certain machines.
- Knowledge and skills for their management: in order to use the SIEM properly and correctly to interpret the events generated in it, the staff who will be responsible for this tool must have specific knowledge of the environment. This knowledge involves, at a minimum, understanding the industrial protocols used in the process, as well as the industrial machines.
To deploy a SIEM correctly in industrial environments, several considerations must be made for it to provide value at the cybersecurity level, and to identify any threat that may occur in the network in which it is deployed. Therefore, the consideration to be taken into account before deployment is a study of the machines and communications, as well as of the network topology. It is thus guaranteed that we will understand the impact of SIEM on the network. It is also important to conduct a study of the assets to thus identify those that are most important to the process, in order to integrate the events generated by these machines first into the SIEM. When deploying the SIEM, it must be borne in mind that not all the information is relevant, and that it is necessary to normalise and process that which may be useful to us to detect threats.
Secure integration with IT-SOC
It is common, in many companies, to have an own or outsourced SOC, in which the alerts and events collected by the SIEM deployed in the corporate network are processed. Therefore, many companies also look for the configuration of an OT-SOC that allows them to detect and mitigate any incident that could also occur in the company's industrial network. To reduce costs, instead of creating a specific SOC for the industrial network, the goal is to deploy the SIEM architecture in the industrial network and to process the events in the IT-SOC, thus having a mixed IT-OT-SOC. To do so, we must consider several points when integrating our industrial SIEM with the IT-SOC:
- Corporate network events must not be treated in the same way as those in the industrial network. Specific alerts must be generated, so that specific threats from industrial networks are covered. To this end, during the integration process, the events will be studied, and the necessary use cases will be generated, according to the needs of the industrial networks.
- Staff specialising in OT networks must be available at each level of the SOC. We thus guarantee the correct performance at each of the levels. If staff lack the necessary knowledge about the industrial network, problems could be generated when dealing with alerts and threats typical of industrial environments.
- If the SOC is outsourced, it should be borne in mind that a secure network architecture, has to be implemented such that it guarantees the maximum possible security in these external communications.
Conclusions
One of the main security measures we must bear in mind when securing OT environments is monitoring. Since it is a passive measure, if its implementation is duly studied before it is deployed, it will give us greater knowledge of what is happening in our machine and through the network. One of the most common monitoring and analysis tools are SIEM, which as we have seen in this article, they gather information such as machines' system events to store and process them. As with other tools we find in both IT and OT networks, using a SIEM in OT networks is recommended as long as the peculiarities of these networks are borne in mind. In our guide we explain in more detail the steps to follow for the deployment of IDS, IPS and SIEM in industrial control systems.









