Sodinokibi: features and operation

In recent years, ransomware has become the most important threat to consumers and companies. Although the number of attacks has decreased compared to last year, there are still many victims that continue to be a major source of income for cybercriminals, causing great damage and significant financial losses.
This type of attack has undergone many changes since its inception, and numerous different families, that target both citizens and public and private entities, can now be identified. However, the trend seems to be focusing on much more specific targets, in pursuit of maximum benefits, in other words, large companies that are able to cope with the demands of larger sums of money in exchange for their data.
This involves more effort for cybercriminals, given that it requires more advanced techniques and greater complexity, which translates to increased sophistication, spread and persistence of malware. An example of this is Sodinokibi, also known as Revil, Bluebackground or Sodin, which, in a very short time, has managed to affect computers all over the world.
Sodinokibi
Sodinokibi is a ransomware for Windows whose propagation follows the RaaS (Ramsonware as a Service) model, in other words, malicious code that is marketed in a personalized way, adjusting to the needs of each subscriber.
Some sources associate its authorship to the same team that developed the GandCrab malware, being an evolution of the latter. This is based on the source code similarities, both in structure and in operation, in addition to presenting the same updating and versioning model, as well as very similar propagation vectors.
It uses different obfuscation techniques to infect systems, mainly cryptography based, to make it difficult for other security programs, such as antivirus or intrusion detection systems (IDS), to analyze and identify its signatures. This feature makes it extremely dangerous since it goes unnoticed by this type of controls.
Operation
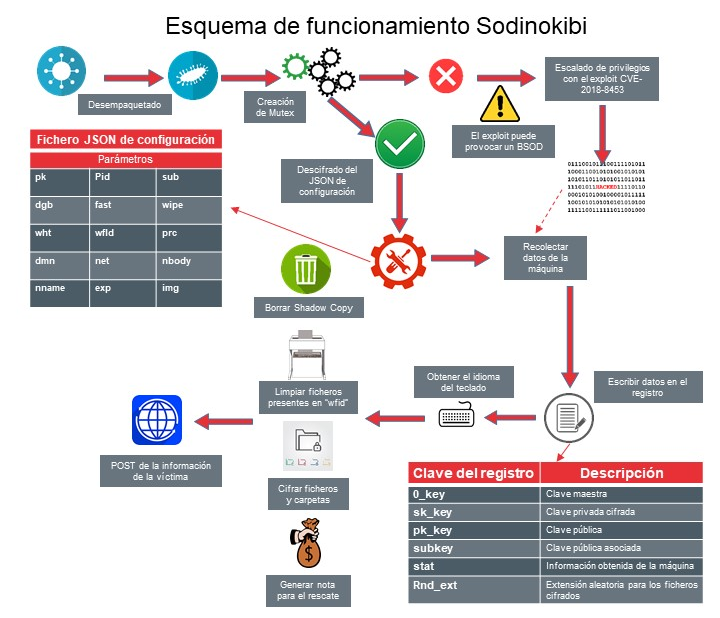
- Sodinokibi Operation. Source McAfee -
Propagation vectors
The propagation of this ransomware has taken place worldwide, with Asia being the most affected region. The main vectors are:
- Sending malicious emails, via spam campaigns.
- Malicious advertising, or malvertising, i.e. malicious code present in advertisements that appear during web browsing, both to be executed directly on the computer, and to be redirected to servers where other executables are downloaded.
- Brute force attacks on the Remote Desktop Protocol (RDP).
-
Exploitation of the CVE-2019-2725 vulnerability that affects Oracle systems (patch available from 26 April 2019).
Execution
The executable file is custom packed, packing all the text strings, library names and DLL files using the RC4 cryptographic algorithm, using a different variable-length random key for each of the encrypted elements. In this way, the text strings, API tables and library references which anti-virus software routinely relies on in order to detect malicious code are ineffective in identifying it.
The information for its load is decoded at runtime, using the hash of the string instead of the string itself, which makes it even harder to detect. Furthermore, its data structure does not recognize key and data size, which makes it very difficult to decipher them by automated means using conventional tools and methods.
Once the malicious code is executed on the victim's system, thanks to one of the different aforementioned attack vectors, its first act is to generate an identifier or mutex, in order to prevent more than one process from entering the critical section at a time. In this way, it prevents malfunctions and makes its detection more difficult.
The next step is to decipher the configuration embedded in its code in JSON format, which will dictate the operations to be carried out according to the parameters selected by the subscriber of the malicious service, so they may vary from one to another.
Privilege escalation
It subsequently tries privilege escalation in the system. By exploiting the CVE-2018-8453, vulnerability, it will run the corresponding exploit after checking if the system is vulnerable, which it usually determines by comparing the creation date of the file %system32%win32k.sys with that of a duly updated system.
If the computer is patched, it tries again using the RunAS function in order to force execution with elevated privileges and bypass the User Account Control (UAC) system of the Windows platforms which prevents the execution of unauthorized changes in the system.
If it doesn’t obtain these privileges, the program terminates and the attack fails. If not, the program collects system and session configuration data, and checks the interface or keyboard language and if it matches any of those excluded in the configuration, the program terminates.
If the language exclusion is not confirmed, running it continues deactivating Windows Shadow Copy system restore options by disabling the vssadmin process and using bcdedit in order to disable backups and delete all stored snapshots and backups.
Before encrypting the files themselves, this malicious code also checks whether it’s running with "SYSTEM" privileges. If so, Sodinokibi will look for the "explorer.exe” process in order to obtain the session token of the user who is using the computer, and, reduce the privileges of the malicious code by means of the ImpersonateLoggedOnUser function, thus preventing the "SYSTEM" user environment from being affected in the file encryption operation.
File encryption
Once that’s done, file encryption, of both the local drives and connected network drives, begins, with the exception of some operating system folders and extensions that enable the minimal operation of the computer, as well as those files that have been indicated in the configuration parameters.
It uses several cryptographic algorithms and locally generates several asymmetric (private-public key pair) and symmetric (single key) keys, using the elliptic curve Diffie-Hellman (ECDH) protocol to generate them.
- Symmetric encryption with AES:
- Used to encrypt the private key of a key pair that is generated locally on the same computer that this ransomware is running on, and whose public key will be used in the file encryption.
- Used to encrypt the data exchanged by the attacked computer with the command and control console, if communication with this component takes place.
- Symmetric encryption with Salsa20:
- Used to encrypt the files targeted by the hijacking, based on the previously generated public key and a private key generated for each file.
Sodinokibi is delivered with two different public keys: one key, as part of the aforementioned JSON configuration, which corresponds to the pk parameter and another key is integrated in the binary, which according to variation can be embedded in different directions of the executable.
These keys are used to encrypt the public-private key pair that is generated locally. The presence of two public keys in the binary is interpreted by analysts as the ability of Sodinokibi authors to decrypt the files seized by their subscribers.
Alerting the victim with extortion payment instructions
The encryption process ends by renaming all modified files, with an extension that will depend on the configuration; for example, if the assigned extension was ".686l0tek69", when Sodinokibi encrypts the file "image.jpg”, and when listed it will appear as "image.jpg.686l0tek69". It will also create a text file "[extension]-how-to-decrypt.txt" in each directory where files have been encrypted, detailing the instructions to follow in order to recover the files. The victim is also alerted by additional screen messages or by modifying the desktop background.
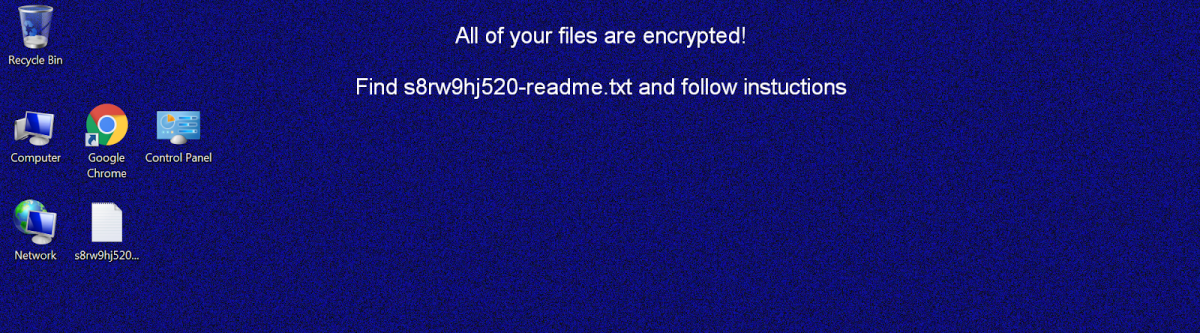
- Details of hijacking warning. Source: Cybereason -
All these messages lead to a website where they provide a test breaker to retrieve up to 3 files as a sample “guarantee" and detailed instructions to buy bitcoins and make the payment using crypto-currencies.
Due to the encryption characteristics, there is currently no available utility or method other than the one offered in the file decryption instructions. Once payment has been confirmed, the website will provide a download link to an ad hoc program that is supposed to be able to decrypt the hijacked files, which is only valid for decrypting a particular Sodinokibi identifier.
Persistence
Sodinokibi is designed to be able to maintain persistence in the attacked system, since it includes code for that. When this option is activated in its configuration, a key, such as those shown below, will be included in the Windows log for this purpose:
- HKLMSOFTWAREMicrosoftWindowsCurrentVersionRun[codigo]
- HKCUSOFTWAREMicrosoftWindowsCurrentVersionRun[codigo]
Where [code] corresponds to an identifier that will depend on the compilation of the ransomware.
Conclusions
Once the attack is successfully carried out, at present, any attempt at alternative decryption must be ruled out as no effective method currently exists. However, following the attackers’ instructions is never advisable, as paying them offers no guarantee that they will do their part and provide a valid recovery option. Furthermore, there is no assurance that the computer will no longer be infected, nor that the information obtained during the attack will not be used for blackmail or other attacks.
It should also be noted that the attacker is not the author of the ransomware, given that it can be obtained through different means and may not even have the recovery keys. One should also consider that the purchase of bitcoins is not something that can be done immediately, which may make it more difficult to comply with the hijackers’ deadlines.
Don't miss our next blog post, where we’ll discuss the prevention, identification and response phases if you are affected by this malware.









