Tools for carrying out forensic analyses on mobile devices

The article Introduction to forensic analysis for mobile devices considers different aspects related to this subject, such as methodologies, phases of the process and the complications inherent therein. When carrying it out, bearing in mind first and foremost the phases of acquisition and analysis of the evidence, it is necessary to know a wide range of methods, techniques and tools as well as the criteria necessary for being able to evaluate the suitability of using one versus another. In this article we will address these issues.
Broadly speaking there are 3 different methods of extracting evidence: physical acquisition, logical acquisition and file system acquisition.
- Physical acquisition: this is commonly the most used method. It consists of making an identical replica of the original, thereby preserving all potential evidence. This procedure has the advantage of it being possible to search for deleted elements. Its main disadvantage is its complexity compared to the other methods and the time that it takes to carry it out.
- Logical acquisition: this consists in making a copy of the objects stored on the device. This makes use of the mechanisms implemented natively by the manufacturer, that is, those that are normally used to synchronise the terminal with a computer so that the desired information is requested from the mobile device’s operating system. It has the advantage of being a much simpler process than the previous one, although it does not allow a great amount of information to be accessed.
- File system acquisition: this allows all visible files to be obtained through the file system, which does not include deleted files or hidden partitions. Depending on the type of investigation, it may be sufficient to use this method, which is less complex than physical acquisition. To carry it out we employ the mechanisms integrated in the operating system to copy the files, Android Device Bridge (ADB) for Android. Through this method, it is possible to recover certain deleted information since some operating systems such as Android and iOS employ a structure that uses SQLite databases to store much of the information. In this way, when file records are deleted, they are only marked as available to be overwritten and, as such, they temporarily remain available, and it is therefore possible to recover them.
When it comes to selecting the most suitable method, many aspects are taken into account, such as: the level of thoroughness required, the time limit for carrying out the process, which type of information it is necessary to obtain: volatile information, previously deleted information, information from third party applications, etc.
Another more practical method that may be useful when choosing the most suitable/possible way of acquiring evidence is the following diagram, in which account is taken of different aspects such as whether the USB debugging is activated, whether the terminal is locked or if there is access, etc.
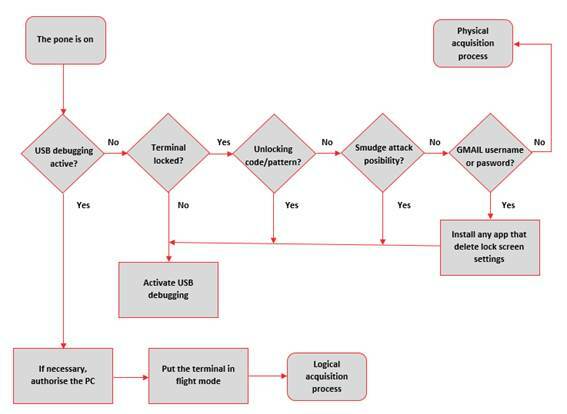
Source: What is your telephone hiding? Forensic acquisition of Android devices
There is a notable number of tools for carrying out the extraction process that must be taken into consideration. Depending on their internal functioning they can be categorised in different ways. As a basis for their classification we can use the pyramid proposed by Sam Brothers at the 2011 U.S. Cybercrime Conference.
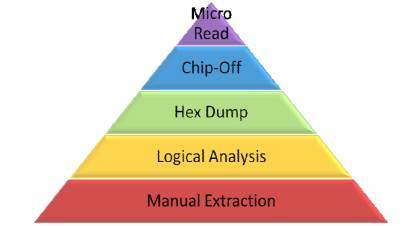
Source: Classification pyramid of forensic analysis tools for mobile devices
The aim of this pyramid is to be a guide for classifying forensic analysis tools in accordance with different criteria, such as complexity, analysis time required, risk of loss or destruction of evidence, the level of invasion and what is known as "forensically sound" which means something similar to level of reliability, although it is only a perception, since all of the tools and techniques used must have proven reliability. The way to read the diagram is from bottom to top so that the upper layers have greater technical complexity, greater time required and are more "forensically sound".
Below, we will present a series of tools that are very useful for extracting information:
Generica free tools
- AFLogical OSE - Open source Android Forensics app and framework is an application in APK format that must be installed beforehand in the Android terminal. Once the process is completed it allows varied information to be extracted to the SD card (call log, contact list and list of applications installed, text messages and multimedia), which must subsequently be recovered either by connecting the card to an external device or through the ADB.
- Open Source Android Forensics is a framework that is distributed via a virtual machine image that brings together various tools which allow the analysis of applications for mobile devices, including both a static and a dynamic analysis or even a forensic analysis.
- Andriller is an application for Windows operating systems that brings together different forensic utilities. It allows a lot of interesting information to be obtained that is related, amongst others, both to social media and to messaging programmes (Skype, Tinder, Viber, WhatsApp, etc.).
- FTK Imager Lite allows us to work with memory dumps of mobile devices to analyse them and obtain evidence.
- NowSecure Forensics Community Edition is distributed as a virtual image that brings together various tools to carry out a forensic analysis, and can carry out different types of evidence extraction or even file carving in its commercial version.
- LIME- Linux Memory Extractor is software that allows a volatile memory dump to be obtained from a Linux-based device, as is the case for Android phones. Likewise, it has the advantage that it can be executed remotely via a network.
Specific free tools
- Android Data Extractor Lite (ADEL) is a tool developed in Python that allows a forensic flowchart to be obtained from the databases of the mobile device. To carry out the process, it is necessary for the mobile device to be rooted or have personalised recovery installed.
- WhatsApp Xtract allows WhatsApp conversations to be viewed on the computer in a simple and user-friendly way. As such, the different databases that store information corresponding to messages should be obtained beforehand.
- Skype Xtractor is an application, supported both on Windows and Linux that allows us to view information of the Skype main.db file, which stores information about contacts, chats, calls, transferred files, deleted messages etc.
Paid tools
- Cellebrite Touch is one of the most well-known and complete evidence extraction devices. It allows us to work with over 6,300 different terminals with the main mobile operating systems. It is also very simple and intuitive.
- Encase Forensics, in addition to Cellebrite, is a worldwide reference in forensic analysis. Its wide range of features includes that which identifies encrypted files and that which attempts to decipher them through Passware Kit Forensic, a tool that incorporates specific algorithms for this purpose.
- Oxygen Forensic Suite is capable of obtaining information from more than 10,000 different mobile device models and even obtaining information from services on the cloud and import backups or images.
- MOBILedit! Forensic allows a lot of information to be received and advanced operations to be carried out such as obtaining a complete memory dump, avoiding terminal-locking measures, and flexibly creating reports.
- Elcomsoft iOS Forensic Toolkit allows for physical acquisition on iOS devices such as iPhone, iPad or iPod. It also includes other utility features such as that of deciphering the keychain that stores user passwords in the terminal analysed or registering each action that is performed during the whole process to keep a record of them.
To carry out the evidence-gathering process in an Android mobile device, many of the tools require enabling of the "USB debugging" option, preferably the "Stay awake" option and disabling of any time-out screen lock option. In the event that the terminal has any screen lock option configured, it is necessary to circumvent it.
Most of the tools described above, mainly paid tools, include mechanisms to bypass these protections so it is only necessary to follow the steps that they indicate, although this is not always possible. If the process is going to be carried out manually, one or more of the following actions have to be performed:
- If the device is rooted we can try to remove the gesture.key or password.key file in accordance with the mode of protection established, which are stored in /data/system/ or copy them and decipher the pattern through a hash dictionary, such as AndroidGestureSHA1, using a tool such as Android Pattern Lock Cracker for this.
- Install a personalised recovery such as ClockWorkMod or Team Win Recovery Project (TWRP)and subsequently deactivate device access locking.
- The problem of fragmentation on mobile platforms causes the vast majority of devices to be affected with vulnerabilities that will not be resolved for these models and, as such, depending on the Android version, it is possible to use some of themto obtain access to the device, such as CVE-2013-6271.
- Using brute force. When a 4-digit pin is used as a security measure it has been demonstrated that it is possible to obtain it in a short period of time, in around a maximum period of 16 hours.
- A more sophisticated technique could even be used, as was demonstrated by various members of the IT department of the University of Pennsylvania in what they called a «Smudge Attack», which consists of obtaining the locking pattern from fingerprints on the screen of the mobile device, using photographs from different angles for this purpose, modifying the properties of light and colour.









