Dangers of drones in industrial settings

After discussing drones and their relationship with control systems in Robots and drones in the Industry 4.0, in this article we will address the dangers that these unmanned aerial vehicles (UAV) may pose to industries and their control systems.
They are being used more and more and in recent years new utilities for tasks have been researched, such as parcel delivery, or more dangerous ones, such as fire-fighting. In turn, the cost of this technology has decreased and the offer of new models on the market has increased.
On the other hand, attacks such as the one that took place at Aramco highlight the risks that this technology poses to industrial control systems, and the need to have security measures in place to avoid falling victim.
Attack vectors that drones may use
Drones can be used in many ways to attack industrial control systems. When we think about what risks are involved with their use, we almost always think about it from a physical security standpoint, where attacks may result in:
- Violation of privacy: the first attack vector that drones may use is to evade the physical security measures of a facility, such as air space at airports. As it is an unmanned aerial vehicle (UAV), drones can easily avoid a facility’s access controls and, by means of the cameras that some models have, an attacker can carry out reconnaissance of the facilities and violate the privacy of the same.
- Physical attacks: another attack that can be carried out using drones are the physical attacks on systems and people, either through business or military models. For example, an attacker could use a drone to crash it into a turbine and damage it; something that seems difficult but is actually relatively cheap and easy. Another variation of this type of attack would be those aimed at exploiting vulnerabilities in the RPAS elements themselves, such as for example, adulterating electronic components, modifying the firmware of the subsystems, reprogramming elements of the on-board equipment or corrupting data stored in the device.
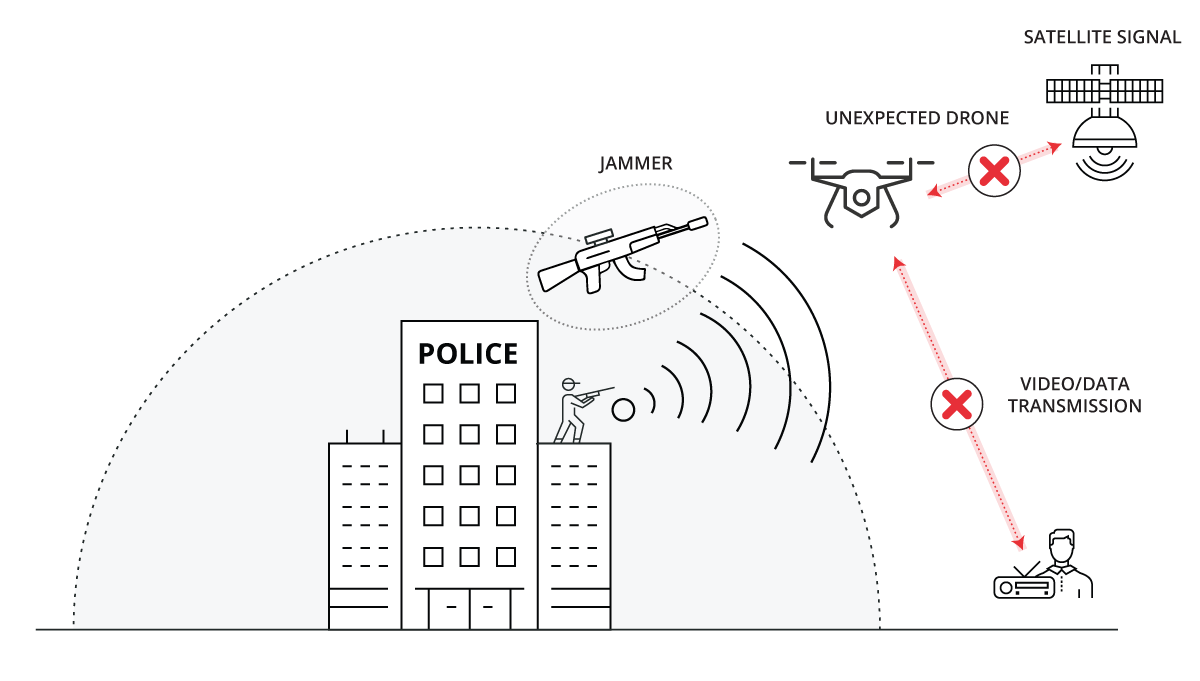
- Jamming: drones can be fitted with inhibitors for frequencies used by a plant’s wireless communications and ensure that the noise emitted does not allow communications, jeopardizing the process. One clear example is GPS jamming, in which the attacker would prevent the GPS sensor on board the RPA obtaining the location of this RPA, jamming the satellite’s radio frequency signal.
However, it can also pose a risk for logical security, by means of other types of attacks, and jeopardize the wireless communications of industrial control systems. As has been shown on many occasions, it’s possible to add a Raspberry Pi, for example, to a drone and equip it with the ability to attack a plant’s wireless communications and exploit its vulnerabilities if they are not properly protected, as noted in the guide of cybersecurity in wireless communications in industrial environments.
- Interception of communications: information capture would be the simplest task, since, as air is the transmission medium, listening can be done simply by being within the range of the signal. In this type of attack on the confidentiality of communications, if it is not encrypted, or if it is but the encryption mechanism is weak and can be broken relatively easily, the information obtained can be very important depending on the use made of the network.
- Packet injection: if it is in the area of influence of a wireless communication, you can try to inject packets into it. Packets can be created ad-hoc, with the intention of attacking the system by exploiting some vulnerability, or simply reinjecting the previously captured network traffic. A remote code injection can also be performed, with the goal of altering the behavior of the RPAS, or to implement it in some way, such as installing a backdoor.
- Inter-network hopping: if the wireless network is not properly protected and does not use encryption, it could be used as an entry point to attempt more sophisticated attacks against the business network. These attacks are classified in 3 types, depending on the feature of the secure communication that may be affected:
- Attacks on availability: unlawful interference or saturation of the communications channel.
- Attacks on confidentiality: any attack aimed at bypassing the encryption mechanism, either because it is too weak, or by illegally obtaining the encryption key.
- Attacks on integrity: ranging from manipulation of legitimate traffic between RPAS elements to traffic injection and replay attacks.
Systems and countermeasures
In Spain, by means of Royal Decree 1036/2017, the civilian use of RPAS (Remote Piloted Aircraft System) is regulated. These regulations were passed by the AESA (Spanish Aviation Safety and Security Agency), and applies to:
- Remote piloted civilian aircraft (RPA) with a maximum take-off mass of less than 150 kg or, regardless of their maximum take-off mass, when excluded from the application of Regulation (CE) 216/2008 of the European Parliament and of the Council of 20 February 2008.
- Remotely piloted civilian aircraft (RPA), irrespective of their maximum take-off mass, or if they’re engaged in customs, police, search and rescue, fire-fighting, coastguard or similar activities.
Article 32 states that the flight performed by such aircraft over installations and infrastructure in different industrial sectors (chemical, transport, energy, water treatment and ICT) shall be at a minimum height of 50 meters, at least 25 meters horizontally from its axis in the case of linear infrastructure and no less than 10 meters from its outer perimeter in other cases.
It also establishes that the flight over installations assigned to national defense or State security, as well as activities within its security zone, and nuclear power plants, may only be carried out with the prior and express permission of those persons responsible for the infrastructure.
This Royal Decree 1036/2017 is not applied in the following cases:
- Unmanned free balloons and tethered balloons.
- Flights that take place entirely in completely enclosed indoor spaces.
- The excluded aircraft as provided in the first bullet, in other words:
- Military RPAS.
- RPAs used exclusively for air shows, sporting, recreational or competitive events, including recreational activities involving toy aircraft.
- RPAs with a maximum take-off mass exceeding 150 kg, unless they carry out customs, police, rescue, fire-fighting or comparable operations.
For this reason we must take existing measures into account in order to prevent a drone attack. Such measures should be in line with aviation security regulations and, in some cases, express authorization may be required to permit their implementation.
As in other matters, the countermeasures should be proportional to the risk analyses carried out and the situations analyzed, taking into account regulatory aspects. Some examples of countermeasures are detailed below:
- Trained eagles: these eagles, once they detect a drone within the perimeter, are in charge of attacking it and hunting it as if it were prey. Although this measure might seem ideal, recent cases, such as the one in Holland, have demonstrated that it is not the best anti-drone measure, although some countries continue studying their use.
- Anti-drone drone: these drones are fitted with a net in order to capture other drones. For example, Japanese police have used these drones to capture any drone flying in restricted airspace.

- Anti-drone drone. Source: United States Department of Defense -
- Rifle jammer: these rifles are able to override the signal between the pilot and the drone, and even to remotely control the drones in order to bring them down to Earth. In Spain, for example, this measure has been used by the police in order to control drones at sporting events.
- Radar to detect drones: the aforementioned measures are useful to stop a drone that’s been detected, but if we don't implement some drone detection measures, we often won't realize it until it's too late. Drone detection radars come into play in this scenario, which are able to detect the radio frequency signals emitted between the drone and the pilot.
- Operation of a Rifle Jammer. Source: Xataka -
- Radiofrequency jammers: another existing measure to combat drones are radiofrequency jammers. These jammers are able to block the drones’ control signal, rending them useless. The problem with these is that they can affect the legitimate communications of the facility, so their use as a countermeasure must be studied beforehand in order to avoid their harmful impact.
Conclusions
The large number of available drone models on the market today means that anyone can own a drone fairly easily at a low cost. But, as discussed in this article, there is a clear legal regulation in RD 1036/2017 that establishes a series of measures and conditions for remotely piloted civilian aircraft (RPA) when Regulation (EC) 216/2008 is not applicable.
Given this situation, it is crucial to know the cybersecurity risks, both at the physical level and for logical security, that drones can pose for industrial control systems. Although prevention and mitigation measures against possible drone attacks are a potentially costly alternative, the risk posed by a drone intrusion and the possible impact it may have on the facility, in terms of both monetary cost and information loss, must be taken into account prior to ruling out the implementation of any measure.









