Differences between OT DMZ and IT DMZ

Introducción a las DMZ
In the field of information technology and networks, a demilitarized zone or perimeter network (DMZ) is a logical or physical subnet that separates an internal local area network (LAN) from other untrusted external networks, usually the Internet, although in the case of industrial control systems it tends to be the corporate network. In this way, while external servers, resources and services remain in the DMZ and can be accessed from outside, the internal network remains unreachable. This provides an additional layer of security, as it restricts the ability to directly access the internal network from the external network.
The main benefit of using a DMZ network is to provide secure access to the services that must be accessed from an external network. DMZ networks are used to isolate assets located in the internal network, as well as to reduce and control access to them from the external network.
The implementation of a DMZ can be done through two network architectures. The simplest is to use a single firewall, which is responsible for managing traffic between the internal network, the external network and the DMZ. If more security is sought, the option is to use two firewalls with the DMZ in the middle as a buffer. This configuration is considered more secure because, if an attacker succeeded in violating the security of the perimeter firewall and access the DMZ server in a non-legitimate way, he would still have to overcome the internal firewall.
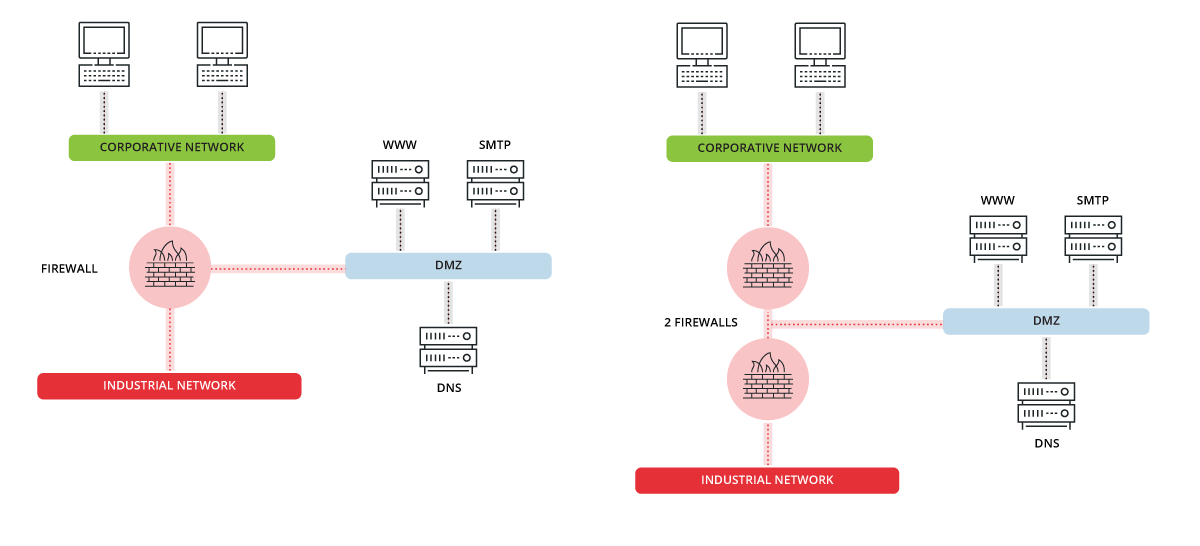
Illustration 1. Possible DMZ architectures.
The DMZ’s servers, being accessible from the external network, require a correct bastion that increases their level of security, since it is necessary to prevent them being used as an entry point for the internal network.
As we saw in the guide to secure access to field devices, DMZs are a vital element within the design of secure network architecture, since proper flow of communications from outside towards the industrial network should go through them, in both corporate and industrial networks. Thus, additional security barriers are achieved thanks to the servers hosted in both DMZs.
For the proper functioning of the DMZs, we must take into account that they must be properly isolated, establishing a specific zone for them and secure communication channels. If the DMZ network is not properly isolated, its operation may be counterproductive, since it could be an entry point to the network.
Differences between OT DMZ and IT DMZ
While the concept of DMZ is the same in IT networks and in OT networks, we find differences in the services they provide each to the networks they protect, as well as the networks that they separate.
Whereas the DMZ located in IT networks is responsible for separating the corporate network from the Internet, the DMZ located in OT networks is responsible for isolating the industrial network from the corporate network.
On the other hand, we can also differentiate the OT DMZ and the IT DMZ by the servers hosted on them and the services they provide. Of course, the OT DMZ will host the necessary servers to service the industrial network. Some of these services located in the OT DMZ, such as active directory (AD) and DNS servers, are not exclusive to the DMZs used in this area but will also be located in the IT DMZ. Many of them work hierarchically so that the DNS server, for example, of the OT network will make requests to the DNS located in the IT DMZ. But we can also locate services that will most typically be located in the IT DMZ and we would rarely see them in an industrial DMZ, such as:
- The proxy server through which Internet browsing would be performed.
- The corporate mail server.
- The company’s web server.
Another type of service that we could locate are honeypots. By placing these devices in this DMZ, we could obtain relevant information about possible attacks on the network, without compromising either of the two networks if we only allow communication from outside to the honeypot and viceversa.
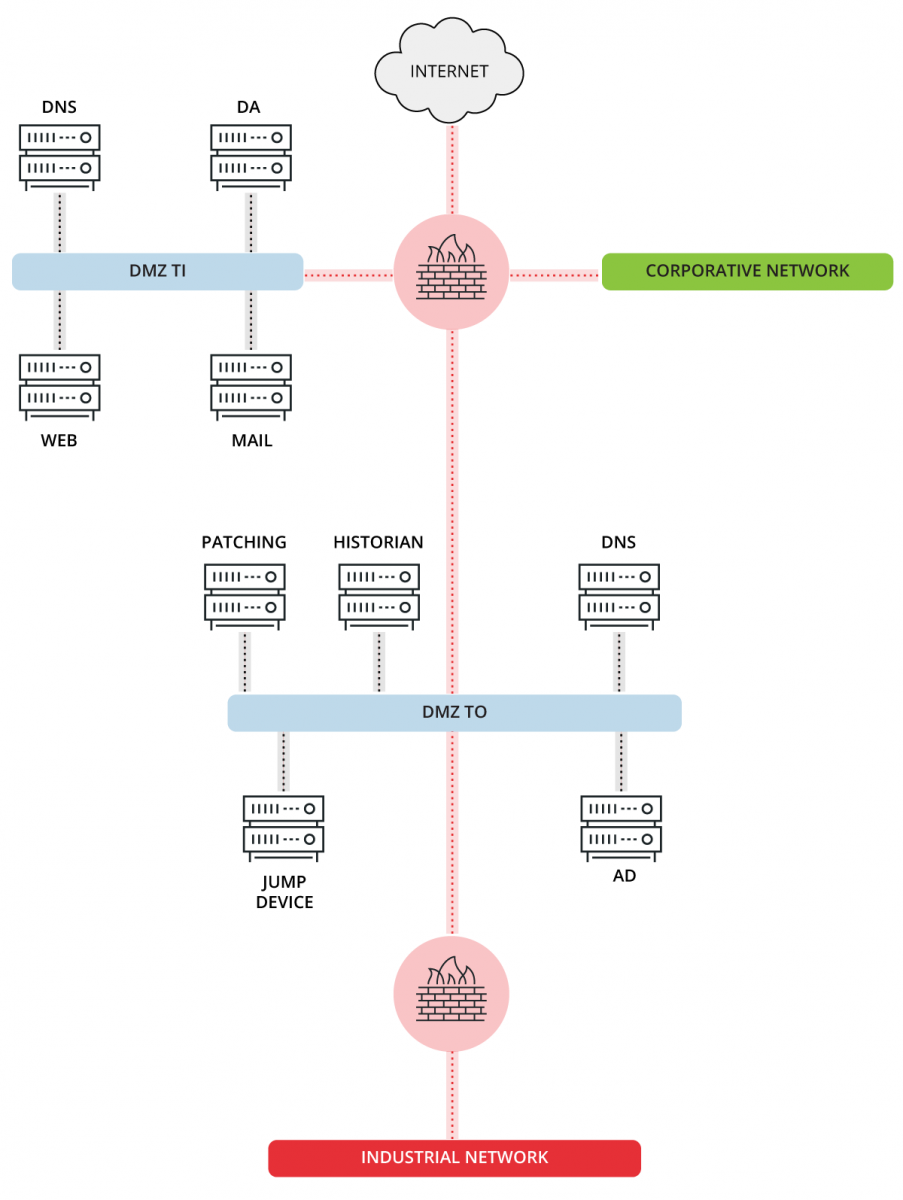
Illustration 2. Provision and servers in IT DMZ and OT DMZ.
Services to be included in the OT DMZ
If we want to use DMZs in industrial environments, we have to know what services, if they are used, should be located in the OT DMZ:
- Patch server: on this computer, the patches that are later downloaded to the computers will be located for updating, thus solving any possible security vulnerability in the computers.
- Jump machine: necessary for remote access to industrial network machines following a secure architecture.
- Historian: team responsible for collecting and storing all the values of the process variables, so that they can be consulted and exploited by corporate applications.
- DNS/NTP Server: equipment to which the NTP and DNS requests from the industrial network will be made.
- Authentication server: device with an exclusive AD, or similar, to validate the users of the control systems. This equipment may be specific to the control system or may be a part of the company’s general authentication server.
Conclusions
Having secure network architecture is a vital measure to ensure the lowest number of entry points for malware or illegitimate users to our network. DMZs are one of the possible elements used in a secure architecture, in both OT and IT networks, where despite their differences they maintain the same operation.









