DrDoS: characteristics and operation

Historical development
Denial of Service (DoS) attacks were developed to disable a network, a system, or an application, preventing users from being able to use those systems.
To carry them out, attackers may cause a failure by exploiting some vulnerability in the system, something that is not always feasible, since they are usually corrected by means of updates or the fact it is necessary to be on the same network. Hence, the most affordable option for attackers is to overwhelm the system’s resources, imposing a workload greater than its processing capacity, something that is practicable in most systems present on the Internet.
Carrying out this action with these characteristics from a single machine is difficult, which is why the attack variant Distributed Denial of Service (DDoS) arose; it involves launching the requests from a network of computers made up of many machines over which control has been previously established (botnet).
This kind of network can be monetised as a service of the CaaS (Crime a as Service) type, that is, the network of machines under control is sold or leased to a third party, so that the latter may be the one to use them in its attacks.
Given that some protocols are used that were not designed with security or this type of attack in mind, Reflected Distributed Denial of Service (DrDoS) appeared, which was quickly extrapolated to other environments. Moreover, the increase in the number of IoT devices represents new possibilities, since they may be compromised and behave as just another element of a botnet.
DrDos operation
In this variant, the attackers do not confine themselves to launching a large volume of requests to their targets, but rather seek to ensure that the service request or access packets that are to be used as the basis for the attack begin at a small size to generate the largest possible number of them.
Moreover, they rely upon an intermediate system that increases the size and complexity of the response packets, depending upon the request. These responses are redirected to the system subject to the attack, replacing the real source IP address with that of the system that is to be attacked. Thus, a service request packet launched by the attacker whose size is a few KB or even a few Bytes, through an intermediate system called an ‘amplifier’, becomes a response packet, which is redirected to the target system of attack with a significantly larger size, known as amplification factor or multiplier factor.
In known and documented DrDoS attacks, this amplification factor may vary between 3.8, in DrDoS attacks based on the NetBIOS protocol, and a multiplier of 51,000, in attacks based on the Memcached vulnerability, that is, a packet generated by the attacker of a few KiloBytes reaches the attacked system with a size multiplied by between 3.8 and 51,000, according to the technique and protocol used.
Although the attack has a great impact on the attacked systems, its effectiveness depends upon by the time needed to generate the requests from a single machine, however small the source packet may be, since the target may have the capacity to absorb a sustained increase in requests. Moreover, the administrators of the attacked system may identify the source of the attack and block it.
To avoid this, attackers resort to launching the original requests, not from one machine, but rather from tens or thousands of them, though botnet networks under their control and by using not a single intermediate amplification system, but rather many of them. This combination gives rise to an attack that is much more difficult to counter.
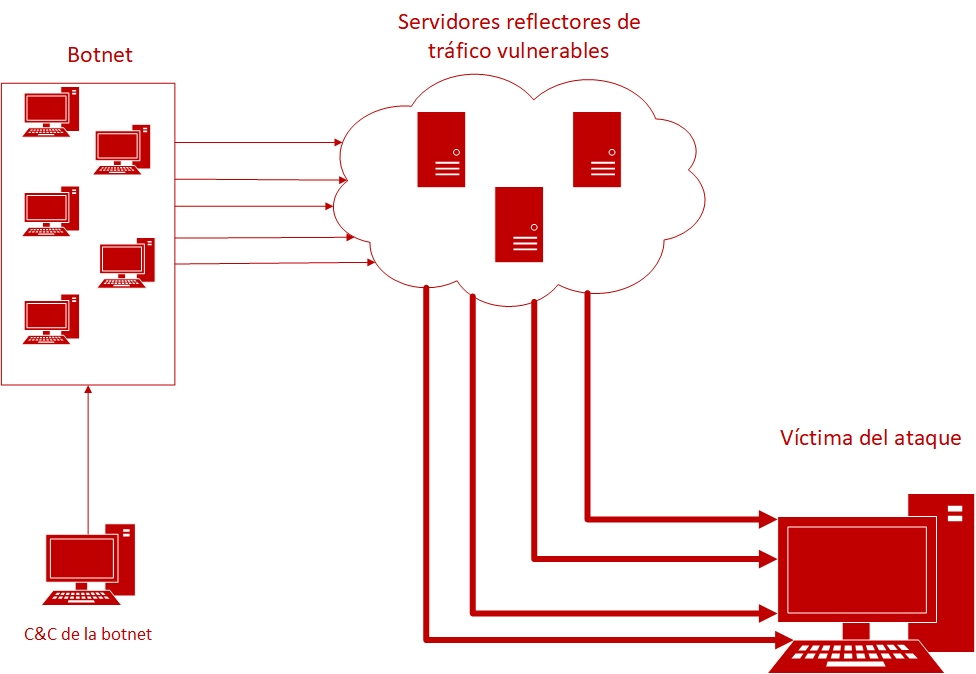
- Figure 1. DrDoS operational diagram. -
The various DrDos attacks are usually based on the different services and protocols that use the UDP (User Data Protocol) protocol. This protocol does not establish an end-to-end connection, that is, communicated is done from the source to the destination, without verifying the availability or the status of the receiver, using the information in the packet headers, such as the source IP address. However, this address may be modified so that the recipient thinks it is from another source, who would thus receive the response. This technique is known as spoofing.
The protocol requires the receiver to return a response to the source IP address, hence if the address has been amended in the UDP packets, the response packets will reach the IP address given by the attacker. Many of these responses would overload the victim.
This circumstance does not arise when the service request is made by TCP, where it is essential to establish a connection channel between a sender and the server so that the server can be provided.
As we have seen, this type of attack can affect us in various ways:
- Our systems may become a possible victim of the attack.
- Our systems act as unwitting participants in an attack perpetrated against a third party.
- Our systems may be rendered usesless because their participation in an attack of this type against a third party generates in them a denial of service.
Consequences and motivation
In any of the foregoing scenarios, the impact of the attack shall be directly proportional to the functions carried out by the affected machines and the time for which they are out of use. It should be borne in mind that, albeit most of the attacks are of a short duration, minutes or hours, there are documented cases in which services are out of use for several days.
The financial consequences of these attacks come on top of the reputational damage, due to the loss of trust and credibility on the part of clients and other stakeholders. Systems being out of use, even if for a brief period, may also entail a loss of business data and serious complications in their operations since they cannot access critical information to carry them out.
Cybercriminals have various motivations for launching these types of attacks. Though it may simply be vandalism, it is normally motivated by revenge, to obtain some kind of financial benefit through extorsion and blackmail, it may cause the victim financial losses, commercial wars, or wars to capture public attention for a given social or political cause.
Defence
Due to the characteristics of this type of attack, any system that is present on the Internet is vulnerable to becoming a potential target. Defending against them will depend upon the combination of their size and thus their ability to absorb the peak processing loads and upon the security measures implemented to counteract the overload of service requests they receive.
On the other hand, to prevent one’s own systems from becoming a reflector, the defence is directly related to the configuration of these systems, the frequency with which updates are applied to correct vulnerabilities, their exposure on the Internet, and the complementary protection measures that have been implemented.
Internet service providers are especially relevant and important when faced with this risk, since they have the mechanisms necessary to detect them, mainly by identifying spoofed packets, blocking malicious traffic or, if not that, diluting it through their infrastructure so that they do not affect their clients’ end systems. Moreover, Internet service providers are a party interested in reducing the likelihood of this threat since, though they are not the ultimate target of denial-of-service attacks, their commitment to their clients in service level agreements directly affect their financial and reputational results.
On the other hand, due to how these attacks are executed, identifying and prosecuting those who instigate them is made difficult in most cases by the fact they act through interposed systems, botnet networks and reflector machines, and from different geographical areas.
Future blogs will set out a detailed description of DrDoS attacks based on different protocols (DNS, NTP, TFTP, mDNS, LDAP, Memcached, CharGEN, PortMapper, NetBIOS, SSDP, QOTD, SNMP and ARD), and offer recommendations on how to prevent and detect them, as well as guidelines for establishing action protocols in the event of being a victim of them.









