DrDoS cyberattacks based on the SNMP protocol

After the preliminary study of denial-of-service (DoS) cyberattacks, together with some of their variants exposed in the article “DrDoS: characteristics and operation”, this new article will address how the NetBIOS protocol is used as a tool to develop a DoS cyberattack in its Reflected Denial-of-Service (DrDoS) variant.
SNMP
The Internet protocol SNMP (Simple Network Management Protocol) has traditionally been used to exchange information about IP network devices to manage and monitor these networks. Devices that typically support SNMP include modems, routers, servers, printers, etc.
There are three different versions of SNMP. Each version offers improvements in the flexibility and security of the protocol, with the third version being the most secure. This latest version offers three levels of security:
- noAuthPriv, which has no authentication and no privacy,
- authNoPriv, which has authentication, but no privacy,
- authPriv, the most restrictive, which has authentication and privacy.
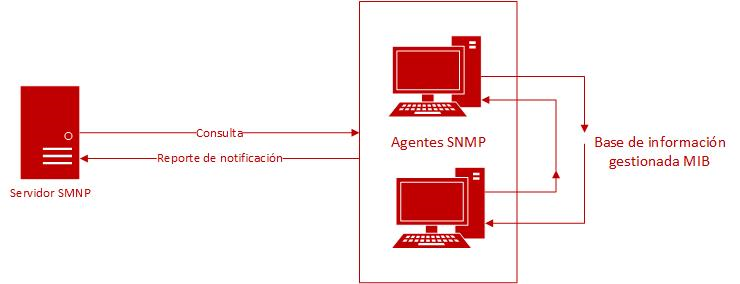
Illustration 1. SNMP architecture diagram.
The operation of this protocol is based on how the administrative computer or computers monitor others in a network. Each administered system runs software, called an “agent”, which is responsible for reporting all relevant information and collection in the form of variables using the SNMP protocol, to the administrator.
The variables, which are organised hierarchically by priority, can be retrieved or modified remotely by applications, which allows management tasks such as configuration changes to be performed. The hierarchy is described as a management information base (MIB) and is organised between SNMP protocol and application prompts.
Attack vector
An attacker with access to a subnetwork or VLAN of servers, monitored and managed via the SNMP service, could trigger a DoS condition on these servers and thereby cause a major impact, since SNMP is a widely-used corporate management protocol.
The attack vector lies in using the UDP protocol for the SNMP transport layer, which by default is through ports 161 and 162.
The mirrored attack feature is due to the fact that source and destination verification is not required when sending packets, which could allow an attacker to change the destination IP address to the victim’s IP, thus performing IP spoofing. This will cause the victim to start receiving packets constantly, saturating the service.
On the other hand, the amplified attack feature lies in the fact that the service offered by the SNMP protocol allows large queries via the “GetBulkRequest” request, which makes it possible to obtain multiple variables and their values, entailing a response of between 423 and 1560 Bytes. This means an increase in the size of the response of up to 102 bytes compared to the request. This results in the victim suffering a denial of service, which is even faster than in other DrDoS attacks.
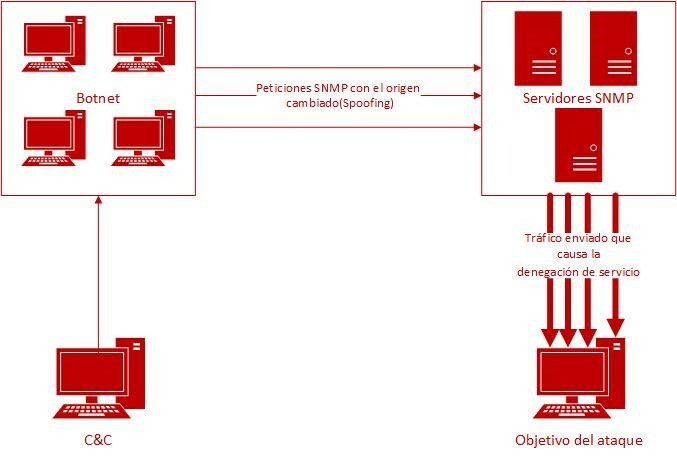
Illustration 2. Schematic diagram of the SNMP attack.
Prevention
The first step is to establish whether or not the SNMP server is vulnerable. One option is to look at which version of SNMP is being used. To do this, you can use the following command, which you will need to execute in the command system of the machine where the SNMP service is installed:
snmpwalk –v
If version 1 or 2 is used, the service is vulnerable.
Another option is to check the availability from outside the SNMP service. To do this, the following nmap command can be used:
nmap -sU -p 161,162 --script=snmp-info [IP to check]
If the command returns information about the SNMP server, it means the protocol is open and therefore vulnerable.
After these checks are done, the following is a list of measures that can be implemented to prevent SNMP server from being used in a DrDoS attack:
- Upgrade the software. It is recommended that you upgrade to version 3, SNMP v3, since this is the only one with more restrictions and security policies, given that it encrypts data and has more robust authentication.
Once this version is available, it is recommended that the maximum-security measures it offers be implemented. The following command can be used to select the desired level of security in terms of authentication and privacy in communications based on this protocol. The most prohibitive, i.e. authPriv, is recommended.
snmpget –l
- Do not expose the SNMP protocol to the Internet. It is recommended that IPsec VPN be used for communication between the different management teams. If exposure is unavoidable, firewalls should be implemented with rules that filter traffic only to recognisable public IPs.
- Use VLAN networks. In corporate environments, it is advisable to use this type of networks and subnetworks and to disable administrator access to the rest of the computers on the network that are not capable of doing so.
- Do not use the default private and public communities. In both SNMP version 1 and version 2, the community’s name is the only way to authenticate access to the SNMP server. Therefore, you are advised to not to use default “private” and “public” communities with customised, but rather administrator-defined communities.
Detection and evidences
One way to detect whether an SNMP server is participating in a DrDoS attack is to monitor it constantly for signs of abnormal usage. Very intensive activity related to traffic over UDP ports 161 or 162 will alert you to a possible attack.
Moreover, analysing the traffic data packets would make it possible to find the source IP addresses and evidence of possible spoofing, thus confirming the attack on third parties.
For early detection, it is advisable to use monitoring tools, such as a SIEM, or to rely on the alerts provided by a well-configured firewall, which will detect traffic spikes caused by the massive flood of packets.
Response and recommendations
If it is confirmed that your own SNMP server is the victim of a DrDoS cyberattack, measures must be taken quickly to minimise the risks, for both the service itself and the victim, following an action protocol drawn up in advance for this type of attack. The protocol should include the following measures:
- Collecting IP addresses and ports. Collect as much information as possible by analysing malicious packets, such as source and destination IP addresses and destination port.
- Contact the Internet Service Provider (ISP). With the information gathered above, the ISP will be contacted and provided with the information so that it can set up filters and block IP addresses, among other measures.
- Block and filter traffic. It is recommended that any illegitimate IP be blocked.
- Contact INCIBE-CERT. They will assist in taking mitigation and recovery measures when handling such attacks.
Once the situation has been restored to normal and it has been verified that all systems are working proper, the causes of the cyberattack must be analysed and measures taken to ensure it does not happen again.
Moreover, such cyberattacks may be reported to the relevant authorities for investigation.









