IEC 62443-4-2, the need to secure components

As already discussed in IEC 62443: Evolution of the ISA 99, the International Society of Automation (ISA) drafted the ISA-99 standard that developed into the ISA/IEC 62443 standard. Part 4-2 of this standard was published in 2018, with the title “Technical security requirements for control components and industrial automation”.
The IEC 62443-4-2 section describes the requirements, which were set out in advance, that the components of a control system need to implement in order to achieve a certain security level. Moreover, manufacturers can certify their products in this standard to prove that a component has all the necessary measures at each security level.
This document is aimed at:
- Asset owners: to reassure them that the devices they install on their systems have some minimum security features.
- Product suppliers: they may refer to the standard to see what set of security measures they have to add to adapt to any of the defined security levels.
- System integrators: they can find out the capabilities of the assets, to configure them according to the security level defined by the asset manager.
- Compliance authorities, such as regulators or security agencies: they can make use this regulation when carrying out compliance audits.
The IEC 62443-4-2 standard differentiates between four types of components found in an industrial control system:
- Software applications (SAs) such as SCADA or antivirus software.
- Embedded devices (EDs), such as PLC, DCS, and IEDs (Intelligent Electronic Devices).
- Host devices (HDs), where the engineering stations, the data historian and the operations computer stand out.
- Network devices (NDs), such as firewalls, switches and routers.
The IEC 62443-4-2 document inherits the requirement specifications from another document in the series, IEC 62443-3-3, which is discussed in article Security level according to IEC 62443-3-3 in Industrial Control Systems. Besides the requirements, this document also inherits security levels, albeit it qualifies them and adapts them to each of the defined device types.
The fundamental requirements (FRs) are still the seven set out in section 3-3, but in this one the System Requirements (SRs) become Component Requirements (CRs). Just as with SRs, CRs contain Improvement Requirements (IRs), which, depending on the security level you want to achieve, will have to be met. Most CRs and IRs are the same for each of the four component types and are combined into a generic CR group. However, there are specific requirements for each of the four components: Software application requirements (SARs), Embedded device requirements (EDRs), Host device requirements (HDRs), and Network device requirements (NDRs) which, in turn, may also contain IR and complement the FRs.
Within the document itself, only the generics, the CRs, will appear in the requirements sections. The specific requirements for each type of component are included in individual sections. To find out what are the specific requirements that apply to each device, you must add those specific to the device to the FRs.
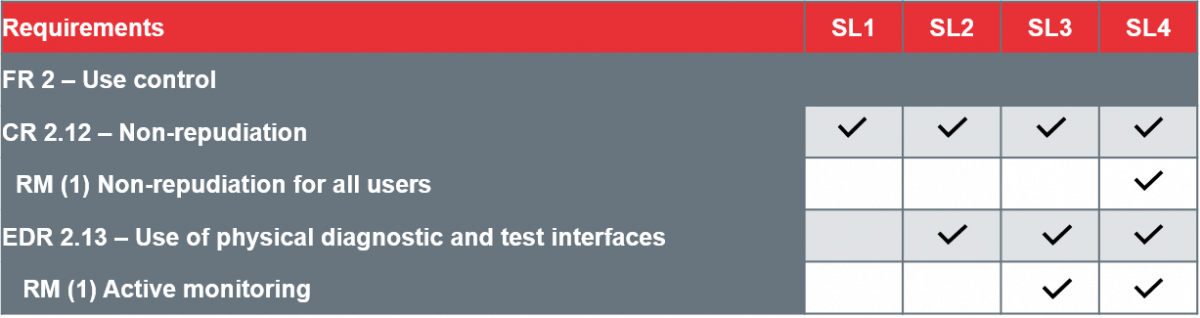
Extract of CRs and IRs necessary with the security level for embedded devices.
If the plant owner has assigned security level two to a zone, using the example in the table, it must fulfil the controls CR 2.12 and EDR 2.13, but the two IRs shown need not be fulfilled.
Certification
The IEC 62443-4-2 part is certifiable within the IEC 62443 standard. This is obtained through ISASecure CSA (Component Security Assurance) certification by manufacturers. To achieve this, the manufacturer must first pass an assessment of the Security Development Lifecycle Process Assessment for Component Development, SDLPA-C based on IEC 62443-4-1. “Requirements for the development of secure products”. An ISASecure SDLA process certification is awarded on the basis of this assessment. ISASecure component certification has three additional elements:
- Security Development Artifacts for Components (SDA-C): Together with the SDLPA-C, they assess the component development process. The SDA-C examines the artifacts that are the results of the supplier’s development life cycle processes, as they are applied to the component to be certified.
- Functional Security Assessment for Components (FSA-C): this examines the security capabilities of each component while acknowledging in accordance with IEC 62443-4-2, that the security functionality requirements differ depending on component type.
- Vulnerability Identification Testing for Components (VIT-C) - the component is scanned for vulnerabilities.
The CSA sets out four levels of certification for a component, which corresponds to the security levels according to capacity. A component that reaches security level SL-4 means that it fulfils the previous security levels (SL-1, SL-2 and SL-3) and that is also includes compliance with IEC 62443-4-1. At the point of certification, the security level is specified according to capacity and the component type. For example: ISASecure CSA security level according to capacity 2 (Software application).
Currently, there are only three laboratories in the world (Exida, Control System Security Center Certification Laboratory and TÜV Rheinland) capable of certifying components in the ISASecure CSA standard. Since 2011, when components began to be certified, devices have only been certified at levels 1 or 2, none at the maximum security levels. All the certified devices have been published on the ISASecure website.
Conclusion
With the current trend towards improved cybersecurity in industrial organisations, compliance with the IEC 62443 standard will become an increasingly common practice. On the other hand, large companies are demanding that their devices have certifications that ensure that they fulfil certain security levels. ISASecure’s IEC 62443-4-2 standard provides a security compliance framework for system components, providing a high level of confidence for asset owners.
It is important to note that the certification can only be done by the manufacturers themselves, but that the application from customers for this certification will make the list of certified products grow and the device options will become longer and longer.









