Industrial Security 2016 in Numbers

Throughout 2016 INCIBE-CERT continued to work on the early-warning services and advisories in cybersecurity. Specifically, the ICS Advisories section includes all advisories for industrial control systems, services which commenced in 2015.
In mid-2016, the INCIBE-CERT site went live, giving greater visibility to content related to the industrial sector and a newsletter was also incorporated so as to inform about all vulnerabilities affecting devices, software and other elements from industrial manufacturers.
As well as this daily publication of the early advisory system and advisories for industrial control systems, INCIBE, through INCIBE-CERT, has continued to disseminate security on the industrial control systems by publishing specific content on the blog.
The advisory service provided in 2016 reflects the main vulnerabilities affecting the industrial sector. The following are the results regarding the work developed throughout 2016:
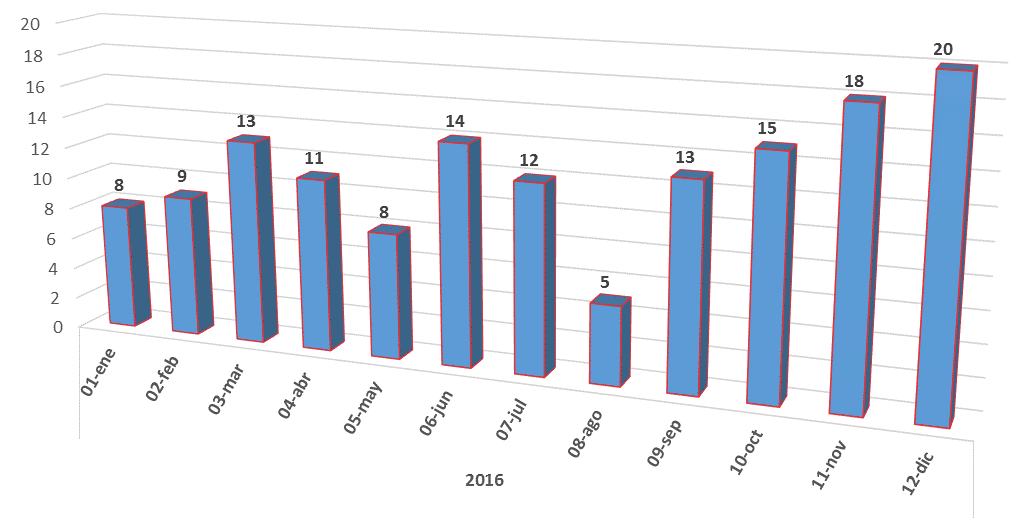
-Number of advisories issued each month-
146 vulnerability advisories have been posted in relation to the industrial sector, including devices, applications or communication elements within such environment.
Summer is not a time in which many advisories are published; due to summer holidays, the activity during those months is usually lower. However, June and July were months with an unusual activity volume. August was relatively calm but the last quarter of the year saw an increase in the number of advisories published, the record being reached in December.
Sector Rankings
Regarding the sectors involved, advisories published concerned almost all strategic sectors defined in the Act on Critical Infrastructure Protection (Law 8/2011), as shown in the following chart:
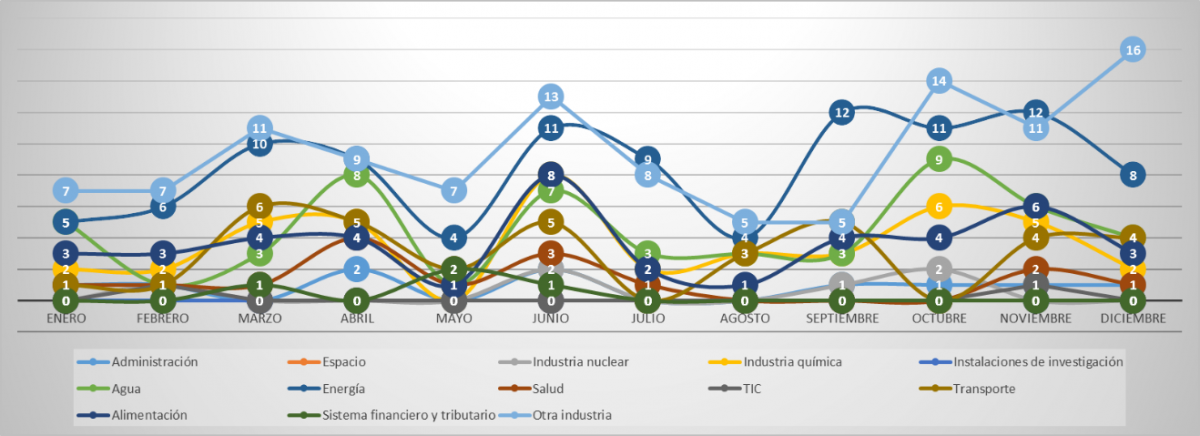
-Evolution of advisories by sector. The energy sector, just as in 2015, was the most affected sector-
Most advisories issued are related to devices used in several sectors since they serve a more general purpose, which means that a single advisory can affect different sectors. Therefore, products (devices and applications) corresponding to the "Other Industry" category are those most frequently affected by advisories; practically every month.
As explained in the Overview of 2015, these data do not mean that the level of security in said sector, or in those other sectors more heavily affected such as the Energy sector, is lower, but are a consequence of them being large sectors including many different processes in which there are millions of devices in place.
Nature of the Advisories
The following chart shows the evolution of data between 2015 (left) and 2016 (right). Data have been collected in the same way as in 2015 (so a single advisory may include information on more than one vulnerability).
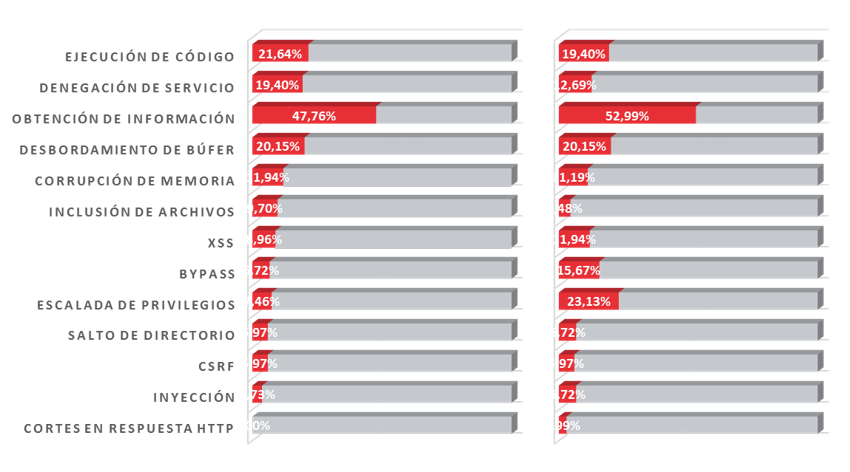
-Nature of Vulnerabilities. It must be taken into account that a single alert may be related to several vulnerabilities-
Vulnerabilities related to the obtaining of information are once again the most prevalent ones, but it must be noted that there has been an increase in the number of advisories caused by vulnerabilities related to the escalation of privileges, which ranked second in this overview of 2016 from a lower position in 2015.
The number of advisories related to the authentication bypass, doubling its incident rate as compared to the previous year.
According to the types of vulnerabilities with the highest increases, it is obvious that in 2016 researchers focused on the authentication of devices and applications comprising control systems so as to increasing the security of the main access point.
Buffer overflows maintained a high incident rate, since it is a common vulnerability; the other types maintained approximately the same levels reached in 2015.
As was the case during 2015, many advisories referred to vulnerabilities exploitable remotely. Therefore, and once again, it is necessary to raise awareness among companies so that they protect their network perimeters and locate their network devices behind firewalls and/or in isolated networks whenever possible.
Manufacturers
The list of manufacturers more closely related to advisories has slightly changed as compared to the previous year. The main leaders in industrial control system products are still those which are most exposed and, therefore, those that see the highest numbers of advisories.
Although the top four names are the same ones than a year ago, the number of advisories related to MOXA is worth noting. It is also worth highlighting that there were six advisories in relation to ABB, a manufacturer not on the 2015 list, which shows the security efforts of the sector.
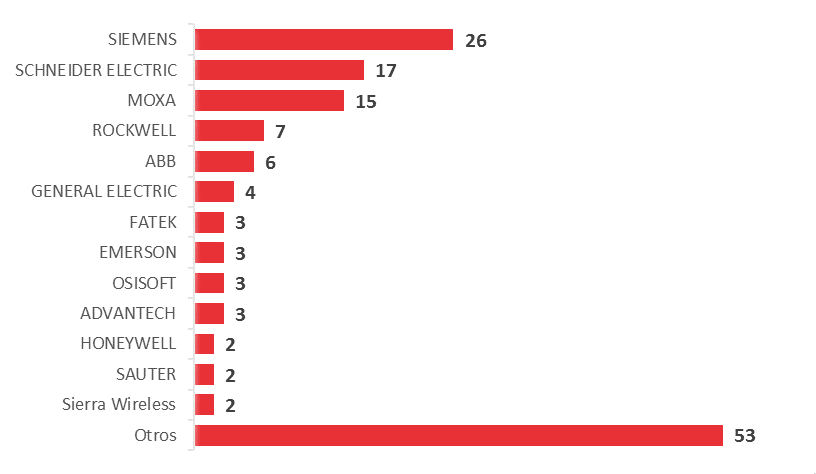
-Number of advisories issued by manufacturer-
Criticality Rankings
Classification by criticality in 2016 is similar to that shown in the overview of 2015; with the majority high or critical. This reminds us that the protection of control systems must be reinforced, since vulnerabilities reported may involve major disruptions for the company as well as major consequences for the production process.
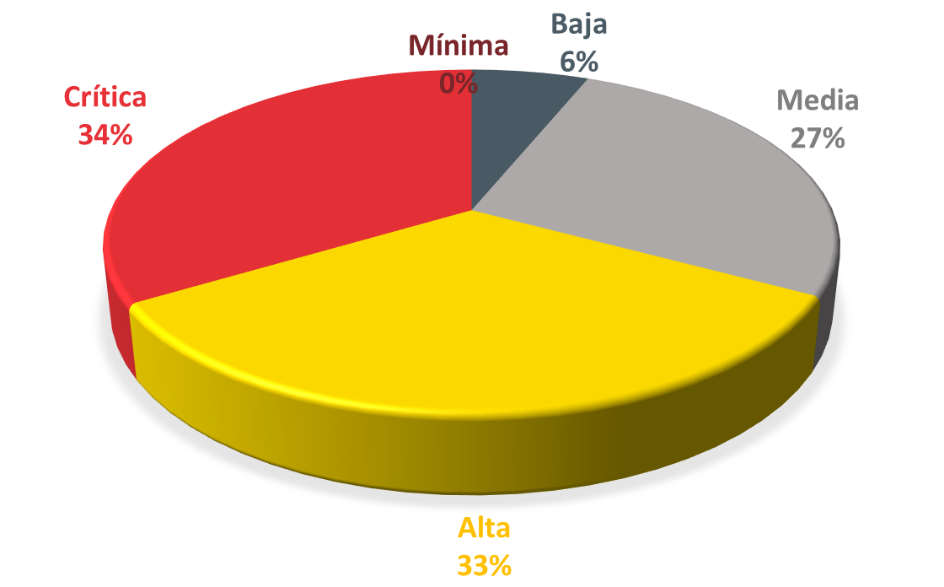
-Advisories Classification-
Evolution in 2017
In the overview of 2015 we made some forecasts for 2016 and we were not far off the mark. Among other things, we foresaw that the number of advisories would continue to increase, as they have; that the list of manufacturers would not change much and that major manufacturers would remain top of the list. Regarding sectors, we stated that all had to improve in order to match the efforts applied by the Energy sector so as to obtain a flat chart and while it has flattened somewhat, there are sectors in need of further improvements.
For 2017, experience suggests that everything must follow the same path. The publication of advisories may not increase much in terms of numbers, but the distribution of criticalities must be balanced and the general level of criticality must be reduced since efforts applied for the improvement of security are higher with each passing year.
Regarding manufacturers, the same approach will continue to be taken, although we hope that other major manufacturers such as ABB and GE make greater efforts to publish more information on their problems and solutions.









