OPC UA, balancing cybersecurity and performance

Today, with the consecration of Industry 4.0 and the emergence of Industry 5.0, big data and IIoT, the industrial networks must process a large amount of information and data. One of the most important aspects is that every industrial environment is made up of many devices from different vendors, therefore, interoperability between devices is a major challenge.
OPC Unified Architecture or also referred as OPC UA, is the most modern standard presented by the OPC Foundation. This new standard was created with the aim of improving security, reliability and interoperability in data exchanges between different systems or equipment in industrial environments.
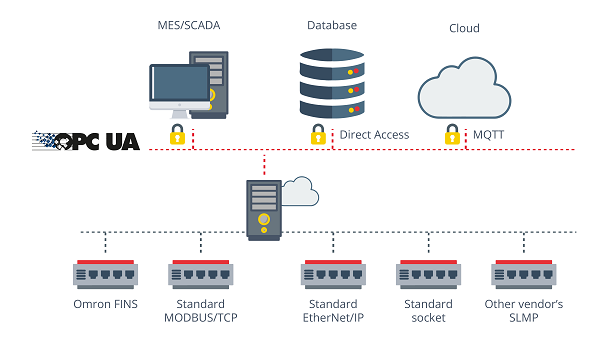
- Network OPC UA. Source -
In summary, the OPC Foundation designed the OPC UA standard to improve connection-oriented service, enabling the creation of new and easy ways to communicate between different operating systems. All this, added to the considerable improvement in the security of connections, marked by the authentication of users in clients and servers, authorization within OPC communication relationships and data integrity, make the OPC UA standard, a protocol with all the specifications and functionalities of OPC Classic, but, greatly simplifying and fixing the known configuration issues of the primary protocol along with the lack of interoperability and security.
Specifications
Client-server architecture
OPC UA, like the classic version of the protocol, has a client-server structure, in which both types of elements interact to exchange information. Therefore, each OPC UA system can have multiple clients and services at once. In addition, each client or server can perform simultaneous interactions with one or more clients or servers.

- Clients and servers OPC UA. Source -
- OPC UA client: The OPC UA client has a structure made up of two divisions: the first, the Client Application, in which the configuration and code of the OPC client are implemented, and the other Communication Stack, in which the data requests are defined. There are two ways to make requests:
- Direct request: The client requests and the server respond.
- Subscription request: The client subscribes to a variable, and the server sends the data if there is a parameter change, when a value is exceeded, or when a rule determined by the client and approved by the server is met.
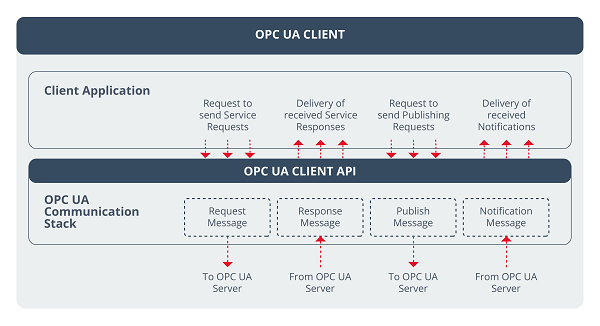
- Structure of an OPC UA client. Source -
- OPC UA server: The OPC UA server is divided into three sections: OPC UA Server Application, OPC UA Server Api and OPC UA Communication Stack. There are different sections within the architecture of an OPC server:
The first one includes the code implemented for the server function, and in addition, there are different real objects, in other words, internal server variables, or other physical devices used by the server.
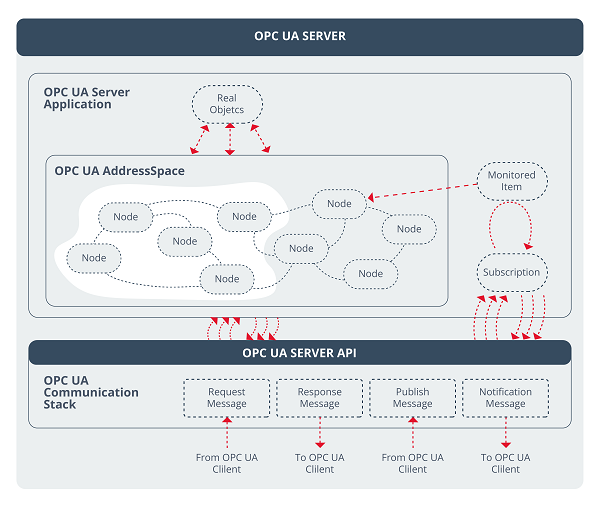
- Structure of an OPC UA server. Source -
- The OPC UA AddressSpace group contains the nodes, which can be defined as objects used by the OPC UA server to represent final objects in the control pyramid. Among them there is the possible to have variables of different types, functions, real objects, etc. In addition, there are the Monitored Items and Subscription groups: the former stores the objects for direct reading and the latter the data of the objects that work on a subscription basis.
- The Communication Stack section is responsible for receiving the request or message from the OPC client and sending it to the OPC UA server application.
Client-server data exchange
Configuration between client and server can be done in multiple ways, allowing for a great deal of customization of communications.
The first way is through the OPC UA client itself, capable of using OPC UA services to directly read and write data from the nodes in the AddressSpace explained above.
The second way is more complex, but it is the one that allows to fully configure the communication, something necessary if you want to maintain high performance, but increase the level of security of the network. Within this modality, the OPC UA client would use the afore mentioned Monitored Items and Subscriptions to obtain the changes of the variables.
Performance-relevant parameters
As mentioned above, the use of Monitored Items allows to configure different parameters that give the ability to adapt requests, as needed, to increase the performance and security of communications.
In the following illustration it is possible to see the different parameters of the OPC UA Monitoring mode:
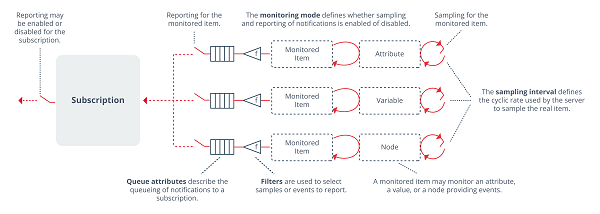
- OPC UA Monitoring Mode parameters. Source-
- Publish Interval: The time interval marked by the client (within the configured ranges of the server) for which the server publishes the data.
- Sampling Interval: Sampling time used by the server to check whether the value of a variable has changed or not.
- Filter:criteria set by the OPC UA customer to determine when a notification is to be generated, that is, when there is a change that meets the parameters defined in the filter.
- Queue Parameter: Client-defined queue size (within server parameters). This parameter indicates the number of values that are stored on the server before being reported to the client.
Security in OPC UA
The OPC UA specification is integrated with a security model superior to the classic OPC specifications, with the possibility of customizing, to a large extent, the security configuration that each user wants to select, but always following the minimums established in the standard for OPC UA servers.
There are different security methods, with certified security being the most widely used and secure.
To use this type of security, the device must have its own certificate installed with minimum requirements established by the OPC Foundation. The use of certificates follows the following structure:
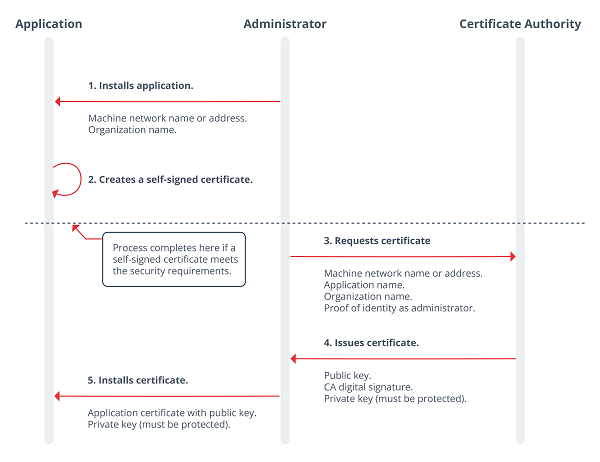
- Security with OPC UA certificate. Source-
In addition, there are other types of authentications, such as:
- Anonymous: Without any user authentication.
- Username and password: Requires the creation of a username and password.
On the other hand, we have security policies, through which OPC UA allows you to define up to three security profiles:
- None: It doesn't require security.
- Sign: Allows you to use the PKI structure using Basic256.
- Sign & Encrypt: it also requires a PKI infrastructure, and you can choose different variants, both Basic256Sha256 and Aes128-Sha256.
Conclusions and safety/performance assessment
Given all the information at both the configuration and security level, it is clear that the OPC UA protocol allows users to configure a large number of parameters to obtain high performance both in terms of data acquisition and interoperability between systems, guaranteeing a high level of security thanks to the different security policies presented in the specification.
Configurable Sampling Interval, Queue and Publish Interval settings allow anyone to adapt the data collection and publishing speed, depending on the requirements of the user and the industrial environment.
On the other hand, the subscription method, allows you to have a secure open connection by means of a certificate or any other method chosen by the user, which reduces the overall reading time, since only a single handshake and exchange of security data is carried out, also managing to maintain security throughout the subscription without affecting performance. Thanks to the possibility of configuring the parameters described above.
In conclusion, OPC UA can allow you to have a high level of security through the configuration of all the security policies and methods contained in the specification and, in addition, obtain a high performance in data acquisition, without forgetting the improvement in interoperability between industrial devices with respect to other protocols.









