Secure remote access in ICS

Introduction to remote accesses to ICS
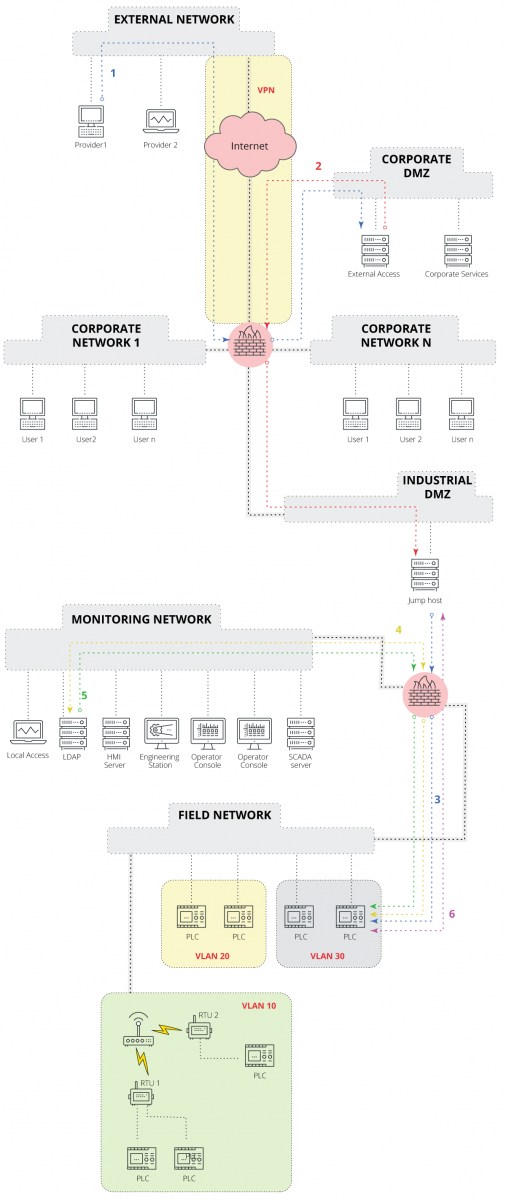
Remote access to OT systems is now commonplace, especially driven by industry 4.0 applications, although it is not unique to these cases. Increasingly more companies are contracting out the development, assembly and commissioning of new machines that require remote access, so that the supplier can provide the technical support agreed upon in the contract. For clients, these accesses are an entry point to their network, so they should seek to make them as secure as possible and only use them when strictly necessary.
With the constant increase of attacks on critical infrastructure, it is of the utmost importance to secure the networks and systems they are made up of. To avoid this situations, the method established in the good practice guides defines a direct isolation between the IT and OT networks. Therefore, in order to access one network from the other, or from one outside the company, it would be necessary to strictly control these communications. This was discussed in the “Guide to secure access to field devices”.
Over the years, this practice has been insecure and uncontrolled. Some of the most common configuration errors and bad practices found in any industrial company are:
- To configure a flat network, that includes all company devices, without any type of segregation in VLAN that separates the devices by levels of criticality or function. This makes it possible for any malicious access to spread to all devices.
- Not configuring isolation between IT and OT networks, which would mean that if an IT computer is infected with malware, it can spread to OT systems unimpeded.
- Direct connection of ICS's own devices to the Internet, which exposes them to unwelcome access and attacks.
- Default passwords for remote access to devices.
- Using third-party remote access solutions because, despite their ease of use and practicality, control over who accesses what and how is completely lost.
Remote access methods to OT
There are several methods for remotely accessing the systems located in a plant. Some examples are as follows:
- Direct access to the industrial network: the easiest way to provide access from outside an industrial network is through a shortcut. For industrial companies that lack security awareness, this is often the most widespread practice. In these cases, the industrial network is part of the corporate network, with unlimited communications. If they are more aware, then the networks will be separated and access will be managed through firewall rules. To be able to say that the connection is secure, these rules must be end-to-end, i.e. no IP ranges should be used for the communications’ source and destination equipment. Therefore, even if an attacker manages to infiltrate the IT network, they won’t be able to access the control systems because there is no specific rule in the firewall that allows such access. On the other hand, outsiders would be provided access to the organization's corporate network via a VPN, which would assign them an IP within the business range. Examples of specific end-to-end rules would be:
- Operator 1 ➔ industrial network ➔ permitted;
- Mirror historian ➔ historian ➔ permitted;
- Corporate network ➔ industrial network ➔ denied;
- Internet ➔ corporate network ➔ permitted;
- Internet ➔ industrial network ➔ denied.
- Use of a jump client: in this solution, corporate users who wish to access the control systems must first access a jump client located in the OT DMZ, which has direct access to the ICS systems and which will contain all the necessary work tools and programs for the work of the employee who establishes the communication. Outsiders must first enter the business network by using the VPN through a specific remote access device, located in the IT DMZ. Once inside the corporate network, they will access the jump client located in the OT DMZ, just as an employee of the organization would. There are several business solutions that provide and enable controlling this type of access. The most widespread are Citrix's Virtual Desktop or VMware's Horizon solutions.
- Diagram of a jump client access from an external network. Source: INCIBE-CERT. -
- Specific remote access solution: there are specific devices and solutions that provide secure remote access to OT. These are solutions that include hardware and/or software elements to control which ports and applications are exposed to the external network and which users can access them. Among all the solutions there are two extended methods of operation: the first is based on a hardware device, offered by manufacturers such as Ixon or Secomea. On the other hand, there is the software-based method, such as Bayshore's OTAccess solution. Furthermore, they all have the establishment of a tunnel in common, either TLS or encapsulating traffic via HTTPS, between the client to be connected and the solution’s remote device. Said tunnel would be created in the client-solution direction, so it wouldn’t be necessary to allow incoming connections in order to control these communications in the firewall, but rather only one outgoing connection through a port, usually 443.
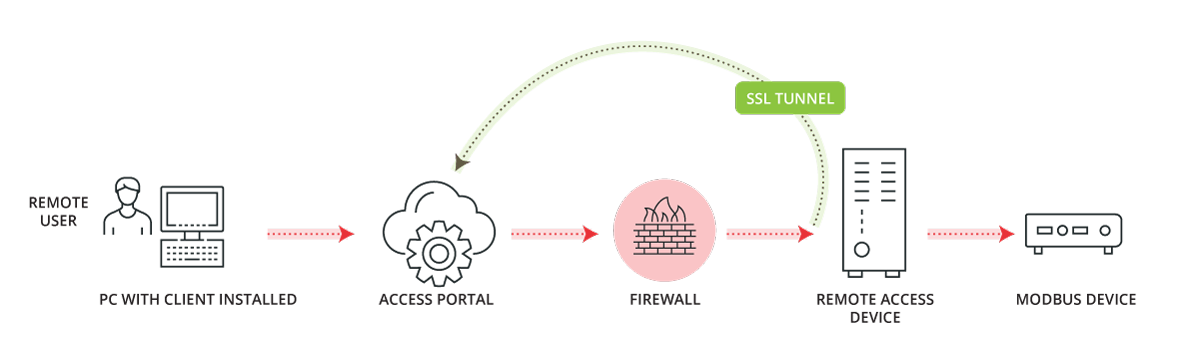
- Web portal based remote access solutions. Source: Bayshore. -
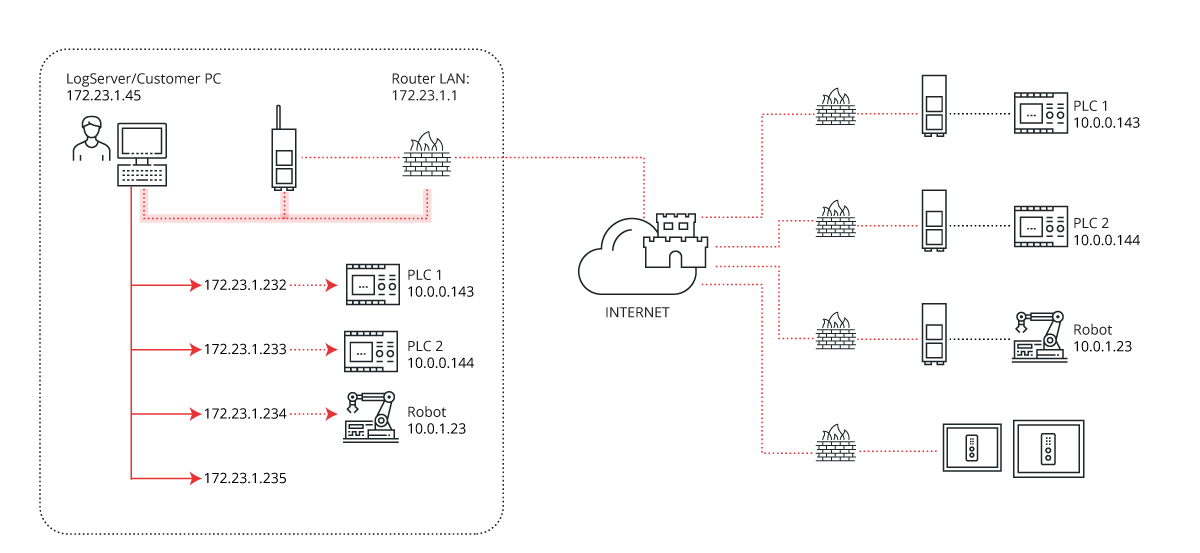
- Remote access solution based on hardware-to-hardware communications. Source: Secomea. -
Comparing the different methods
As discussed above, there are various ways to remotely access control systems. Some are more secure than others, but, at the same time, they are more difficult to implement and deploy. We must always start from the premise that direct remote access to control systems is not recommended in all good practice guides and regulations, since external networks are considered insecure environments. Therefore, any measure taken will be beneficial to the security of the organization.
Using a firewall improves the situation, but it is still not a scalable solution, since specific rules would have to be established for each use and for each connection. At the deployment level, it is the least complex, the most immediate and the most inexpensive method, since only one firewall is needed to separate the IT and OT networks.
On the other hand, the use of a jumper client provides more access control and granularity (low level parameterization, i.e., ability to differentiate accesses and operations depending on the user and role), which are increased when combined with the use of a RADIUS or LDAP for user authentication and role segregation. However, its implementation is complex and maintenance costly, especially from a solution licensing perspective, since it is done depending on users and systems accessed, which can be considerably high.
Finally, commercial remote access solutions allow virtually the same granularity and control as using jump clients, all without requiring advanced networking skills. Furthermore, it would not be necessary to open incoming connections to the OT network at the firewall, since the tunneling is established outbound and through a single port to a known destination. However, in some cases there are limitations on the number of connections and active users that can be established and configured, given that these parameters are usually limited in terms of licensing. In addition, in order to establish the tunnel from the outside it is necessary to access it through a web server, which in some cases is not possible to establish its location within the company, but must be located in the manufacturer's cloud, so some control over the remote access system would be lost.
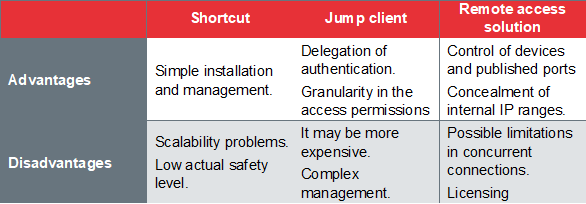
- Summary of solutions. -
Conclusions
The remote accesses in OT are increasingly frequent and necessary, however, we must not forget that they are devices with a far lower levels of security than what we find in IT environments, so it is essential to carry out the appropriate work in order to increase their cybersecurity levels.
In this article we have presented some of the most common methods of securely implementing and deploying these accesses. As we have seen, it is relatively easy to implement one of these solutions, so organizations and companies should start considering which is best suited to their use cases and implement it.









