ICS matrix, the status of v11

Currently, there is a constant evolution in the technologies and implementations made in Industrial Control Systems. On one hand, some of the most common implementations for the improvement of industrial systems infrastructures are digitalization and the use of cloud technology. On the other hand, the increase in communication protocols and IIoT devices (due to the growth of the Industry 4.0) generates a large volume of traffic that is difficult to control and secure.
All these aspects make it easy to carry out attacks on companies or entities with industrial processes, regardless of their sector and service. The existence of a large number of threats in ICS is a reality, and their objectives can range from intrusion into the system, the theft of data or credentials, the search for and exploitation of vulnerabilities or the disabling of the service provided, among other things.
-Industry 4.0 branches. Reference-
Knowledge of how such attacks are carried out is of vital importance. To this end, MITRE data source, more specifically MITRE ATT&CK Tactics and Techniques for Industrial Environments, provides very detailed information on attacks on industrial structures. This collection of tactics and techniques gives organizations the ability to improve their architecture and defense systems so that, in the event of an attack, they can effectively repel or mitigate it thanks to the knowledge obtained beforehand.
This article aims to show the new tactics and techniques included in the ICS Matrix.
General developments in the ICS Matrix
The ICS Matrix from MITRE ATT&CK has undergone changes since its initial implementation, to reflect new attacks employed by adversaries, from techniques, the tactics, to procedures employed.
The ICS Matrix initially consisted of eleven tactics employed by attackers: Initial Access, Execution, Persistence, Evasion, Discovery, Lateral Movement, Collection, Command and Control, Inhibit Response Function, Impair Process Control and finally Impact.
To these tactics mus be added the inclusion of the Privilege Escalation tactic, which currently has two techniques already catalogued and which have been used by different attackers in attacks on infrastructures with industrial control systems. These two techniques are: Exploitation for Privilege Escalation and Hooking.
In addition, MITRE’s ATT&CK ICS matrix, version 11, provides and overview of the adversary’s capabilities throughout the attack lifecycle, as well as the inclusion of new examples and direct relationships between tactics, techniques, and specific ICS cases. All of this is supplemented with information from DHS and the FBI on how different actors have used the technique to carry out the attack.

-Life cycle of an attack according to MITRE ATT&CK version 11-
In the following, both the new tactics and the two techniques implemented in the MITRE ATT&CK ICS Matrix will be further detailed. In addition, some updated techniques of the tactics present since the inception of the ICS Matrix will also be introduced.
Updating tactics and techniques
One of the most important new features of the latest updates of the matrix is the inclusion of the Privilege Escalation tactic. This tactic is very important for adversaries, since, during an attack, the agent that is raiding the system may have access to explore the network through base privileges but requires privilege escalation to achieve more ambitious goals.
Therefore, this tactic refers to the process in which an adversary who has limited access to the industrial system and has achieved this through the application of Initial Access tactic techniques, could increase the scope and scale of his access permissions.
Therefore, from an attacker’s perspective, this tactic will be used to gain privileges vertically or horizontally, starting from a standard user (easier to breach) to a user with administrator, root, or even full system access. There are two types of access that are the final target of any attacking agent on the system.
- Access NT Authority\System: Full access to the system.
- Access to the Admin\Domain: Full access to the network.
Currently, there are a large number of vulnerabilities, both in industrial devices and in different types of software, which allow attackers to perform privilege escalation.
In the following illustration, its possible to see the graphical meaning of privilege escalation horizontally and vertically.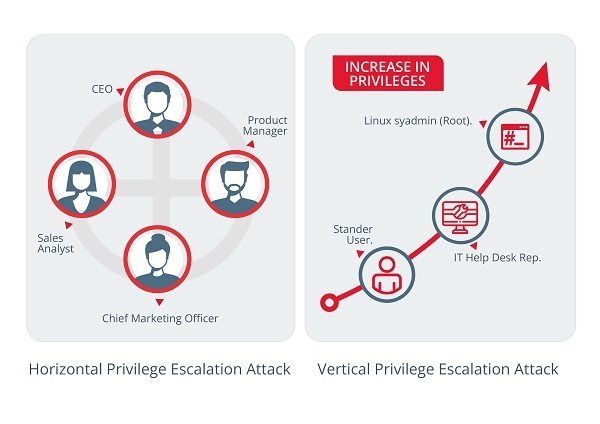
-Privilege escalation horizontally and vertically; Reference-
- Vertical escalation of privileges: Process by which an attacker or a process obtains a higher level of access than it initially had.
- Horizontal escalation of privileges: In this case, an attacker or process manages to gain access to resources that would not normally be accessible. This a more limited escalation than vertical escalation.To prevent this type of attack, both vertically and horizontally, some basic security measures can be implemented:
- Strengthen from less to more: The security of a user architecture is stronger then more protected its most basic level, i.e., the standard users.
- Reinforce the password Policy: Require passwords to be changed from time to time, demand minimum complexity and use two-factor authentication mechanisms.
- Creation of special users and user groups with minimum privileges: Proper administration of users and roles is essential to avoid these attacks.
- Avoid errors in programming of applications that may erroneously gran administrator permissions.
- Modification of default credentials since they can usually be known or calculated by attackers.
- Supervision of default credentials since they can usually be known or calculated by attackers.
- Protection of databases where user groups are stored.
The two techniques used by the attackers to achieve the goal of escalating privileges on the industrial system that were included in the matrix are:
- T0890 Exploitation for Privilege Escalation: Technique by which adversaries can exploit software vulnerabilities to escalate privileges in the system. This exploitation occurs when the attacker takes advantage of an error in the programming of a program, service or the operating system itself to introduce malicious code. Examples of procedures include: INCONTROLLER and TRITON. There are different possible mitigations for this technique:
- Use of Sandboxing.
- Applications with exploit protection exploits.
- Continious software updates.
- Logging applications for access control.
- T0874 Hooking: Technique by which attackers can use and exploit API functions used to redirect call to means of execution and privilege escalation. Examples of procedures include TRITON and Stuxnet.There are also possible mitigations to avoid the Hooking technique:
- Audits, System and permissions scanning.
- Restricting the use of unknown libraries (remote DDL).
In addition to the tactics and techniques described above, other modifications and implementations of the techniques already established in the ICS Matrix have also been made. The matrix is shown below with the updates marked in red:
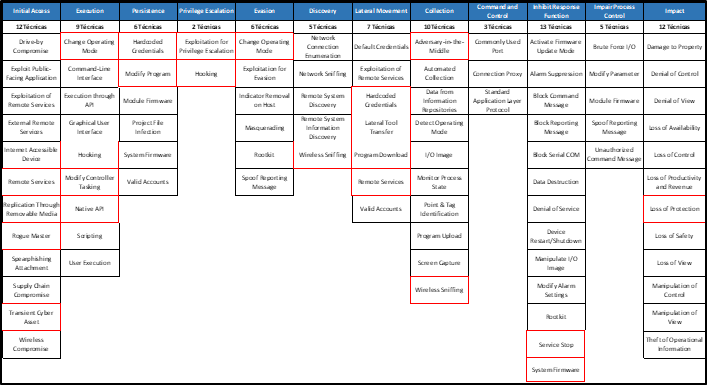
-ICS Matrix from MITRE ATT&CK in v.11-
The most noteworthy new developments are as follows:
- T0837 Loss of Protection: Through this technique, the attacker compromises the system’s security functions, potentially causing damage to equipment, prolonged process interruptions or risks to the personnel.
- T0881 Service Stop: Technique whereby the attacker attempts to disable services or systems to make them inoperable by legitimate users.
- T0886 Remote Services: The attacker attempts to maintain a remote connection to the targeted industrial equipment.
- T0887 Wireless Sniffing: Technique used to try to capture radio frequency traffic.
Conclusion
As we have seen throughout the article, the constant advances in Industrial Control Systems have generated a high interest for different attackers. Because of this, the work done by MITRE with constant updates of the different matrices is very important.
ICS are, on many occasions, embedded in critical systems or infrastructures, where special attention to security is required. MITRE ATT&CK's ICS Matrix provides insight into the most current tactics and techniques used by attackers. For infrastructures with industrial processes, this can mean the ability to detect or mitigate attacks effectively.









