The great robotic crusade
The robotic technology began to be developed and applied in the industrial environments decades ago. With the advent of the Industry 4.0 and all the technological innovations of recent years, smart factories are now a reality. The advent of the digitalization has meant and exponential growth in the implementation of automation systems, where robots have become a fundamental part, replacing in many times the human work due to their efficiency and speed in solving repetitive task.
Top up this growth of robotic devices in context, it is estimated that in Spain, in 2030, there will be an equal number of workers and robots, according to data from the World Economic Forum.
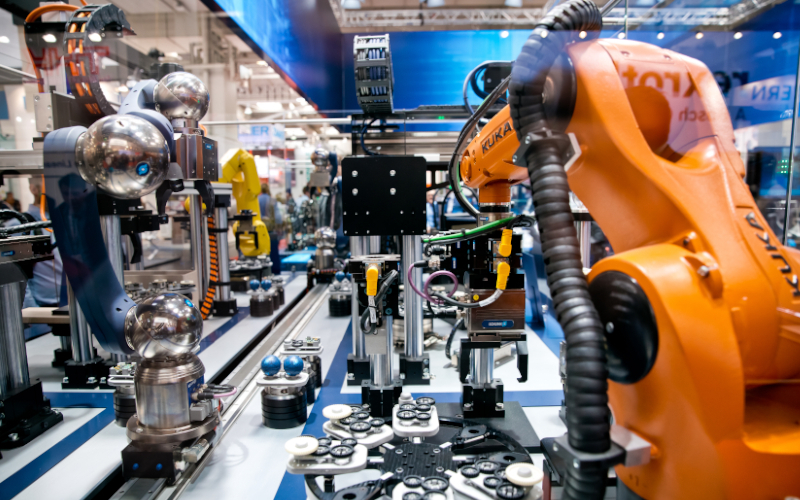
-Industrial robotic-
Robotics in the industrial world is widespread. Some of its main applications are the process automation, such us, the robotic arms implementation in assembly lines, mechanical cutting, grinding and overflowing of sheet metal or measurement, inspection and quality control, etc. In addition, with the new technological advances in robotic aspects, implementations in other environments or sectors, such as healthcare, are a reality.
Another of the principal characteristics of these new industrial environments is the hyperconnectivity between the robots themselves and of these with other industrial devices, which has meant an increase in the complexity of the networks, but at the same time a substantial improvement in the speed of communications, in the accuracy of data and in the creation of models. All this, together with the integration of artificial intelligence, has led to a boom in the automation of industrial processes, thanks to robotic technology.
The advantages of the robotization of industrial processes are obvious, but the risks that this evolution may entail in terms of security must also be taken into account, since a rapid growth in the number of robotic elements has been accompanied by a growth in the vulnerabilities they present, which today, with the growth in cyberattacks in industrial environments, can pose a serious risk to any highly robotized industrial process.
More specifically, an attack on a robotic element could cause damage, both in the economic field of the company that receives the attack, by a possible stoppage of production, as well as in the physical safety of the plant employees due to accidents resulting from attacks on robots. In addition, a vulnerable robot can be a gateway to the industrial network in which it is located.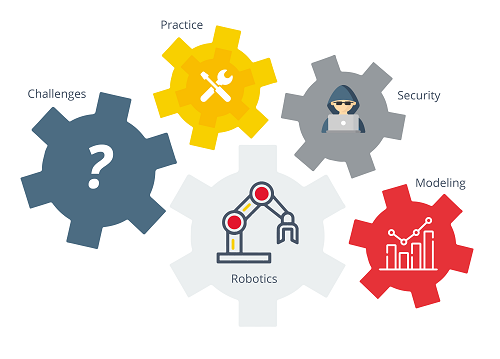
-Interrelationships of robots in the industrial world. Reference.-
Cybersecurity challenges for robots
As it has been already seen, the expansion of robots in industry raises major problems at the safety level. Another of theses major problems is programmed obsolescence or the suspension of updates after a certain point in the robot’s useful life, the lack of software to protect robots or failures in interoperability between systems.
The following explains the main challenges in terms of cybersecurity for robots:
- Combating programmed obsolescence: This is one of the biggest problems in today’s robotics industry, since most manufacturers design their robots so that after a certain period of time they start to fail, require new spare parts and stop upgrades. This problem is critical nowadays and is universal, not only in industrial processes, but also in other sectors, such as the medical or airport sectors. This programmed obsolescence provides a gateway for attackers because the companies that install this robotic technology do not have the necessary capital, in many cases, to be buying new robotic versions and, therefore, continue to use outdated versions that are susceptible to attack.
- Installation of software to secure robots: The Robot Immune System (RIS) is sotware designed to detect, prevent, stop and report threats that affect the robot, thus protecting it from possible malware attacks. RIS is considered as a new generation antivirus for robots and provides the following capabilities:
- Adaptative firewall.
- Data encryption.
- Intrusion prevention mechanism.
- Data loss prevention.
- Interoperability between networks: Another challenge facing the robotics industry is the link between botnets and IoT networks along with the inclusion of artificial intelligence in robotic systems. Interoperability between systems is complex due to the large number of manufacturers and the junctions between networks represent a vulnerable point and accessible for the attackers.
ROS System – Robot operating system
Robots, like a computer, need software to operate, and currently, the most widely used is called ROS or Robot Operation System. It is a middleware for robotics, i.e., a collection of frameworks designed to facilitate the development of software for robots.
ROS is not classified as an operating system, but provides standard services, such as hardware abstraction, low-level device control, implementation of commonly used functionality, message passing between processes and package maintenance.
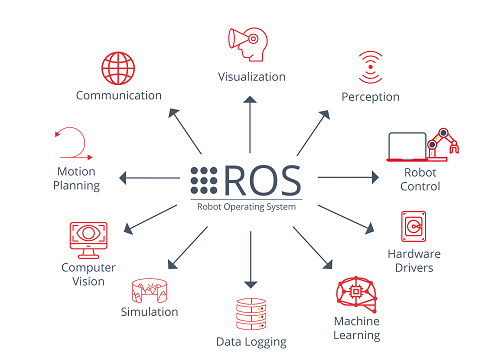
-ROS functionalities. Reference.-
ROS is composed of two basic parts:
- The “Operating system”: Called ROS itself, being free software, under terms of the BSD license that allows freedom of commercial and research use.
- The ROS-Pkg packages: Consist of a suite of user-contributed packages capable of implementing functions other than the basic ROS functions, such as localization, simultaneous mapping, planning, perception, simulation, etc.
ROS is under continuous development and the latest versions and updates are focused on increasing robotic safety. Some of its new implementations are the integration of the Data Distribution Services (DDS), as a transport layer that will guarantee authentication, access control and message cryptography.
Specific attacks on robots and specific defense methods
In this section, it will be specifically defined some attacks to which robots are susceptible and how to defend against them:
- Alteration of controller parameters: Attack by which an adversary alters the configuration file transmitted to the FTP server by the programming operator:
- The implementation of secure transmission protocols such as SFTP or HTTPS greatly reduces the risk of this very specific attack by encrypting the data sent so that it cannot be modified.
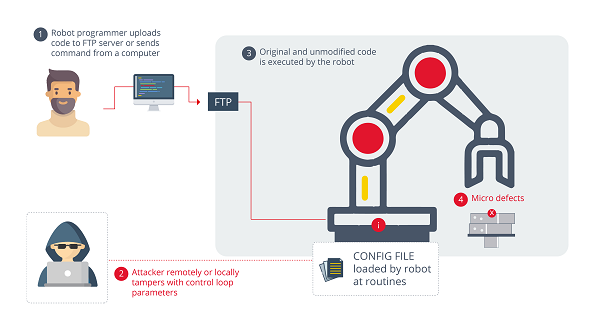
-Attack on configuration file on FTP server. Reference. -
- Alteration of the robot state: In this case, the attacker attacks the robotic system using malware to induce a false signal in the operating state. The operator, in remote state, will not know the real state emitted by the robot. This attack vector is commonly used to perform stoppages in the production line.
- In this case, the inclusion of the mentioned RIS would allow detecting an alteration in the robot’s state, the presence of the malware and its removal. In addition, it is always advisable to have a double check to look for the robot status.
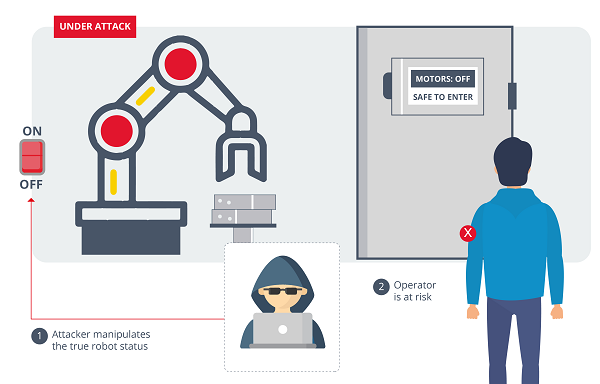
-Alteration of the signal sent by the robot to the operator. Reference. -
These are some very specific examples of the attacks that an attacker can perform on an industrial robot. The consequences can range from the alteration or sabotage of the elements produced, ransom demands, since the company would not know which elements have been affected, physical damage on production elements or the robots themselves, or the exfiltration of confidential data found in the robot configuration files.
Conclusions
Although the robotics world has historically neglected security, the field is now evolving at a rapid pace. Industrial robot standards must consider threats in the same way as ICS standards. A thorough analysis of the risks to which the industrial process is exposed with the inclusion of robots in its processes is necessary in order to determine and implement defense strategies against possible cyberattacks.
In the role of robot security in industrial processes, the figure of suppliers must stand out, who must understand that robots have a long useful life and must put aside programmed obsolescence and start providing patches and solutions on an ongoing basis, so that companies can have the latest version of the software, thus reducing the chances of suffering an attack.









